Katie Nickels
@likethecoins
Followers
54,328
Following
2,819
Media
2,424
Statuses
16,245
Director of Intel at @redcanary . SANS Certified Instructor for FOR578: CTI. Senior Fellow at @CyberStatecraft . She/her. Mastodon: @likethecoins @infosec .exchange
Joined September 2008
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
JIMIN IS COMING
• 578725 Tweets
Mbappe
• 410396 Tweets
#EURo2024
• 378350 Tweets
Lukaku
• 163074 Tweets
Grace
• 117263 Tweets
Kylian
• 99958 Tweets
Kante
• 98431 Tweets
Belgium
• 92813 Tweets
Eurocopa
• 78671 Tweets
Thuram
• 67454 Tweets
Jack Black
• 66256 Tweets
Katy Perry
• 64954 Tweets
#AUTFRA
• 57877 Tweets
Leila
• 56434 Tweets
Slovakia
• 55145 Tweets
#DiamondTemaTutuklansın
• 45634 Tweets
Bélgica
• 44276 Tweets
Joey
• 34432 Tweets
#FRAAUT
• 27172 Tweets
Dembele
• 24182 Tweets
Saliba
• 24147 Tweets
Samantha
• 22788 Tweets
Eslovaquia
• 21534 Tweets
الزمالك
• 19125 Tweets
Griezmann
• 18170 Tweets
Deschamps
• 16584 Tweets
Camavinga
• 16228 Tweets
Rabiot
• 16156 Tweets
ベルギー
• 11846 Tweets
Coman
• 11607 Tweets
Giroud
• 11149 Tweets
Ceci Flores
• 10939 Tweets
Openda
• 10669 Tweets
Autrichiens
• 10531 Tweets
Last Seen Profiles
New blog post and start of a series! I know it's tough to get started in
#CTI
, especially if you don't have $ for formal training. I'm sharing a self-study plan that brings together links to free resources and a couple questions to consider for key topics.
76
464
2K
This is an *extremely* cool reference from
@CISAgov
that breaks down the cost, impact, and complexity of implementing different security controls...plus TTPs addressed. This is awesome because it helps orgs prioritize! (h/t
@MSAdministrator
)
16
295
1K
Today in my latest post, I share my top 10 recommendations for free resources to check out if you're getting started in
#threatintel
. I mixed it up with well-known classics as well as some lesser-known and newer sources - it was tough to choose just a few!
18
365
886
🍾 because I got the news that I am now a
@SANSInstitute
Certified Instructor! Taking a moment to celebrate even in tough times. This has been one of the most difficult yet rewarding challenges I've tackled. I wouldn't be here without the support of a LOT of people... (1/n)
144
27
882
The long-awaited Part 2 of my CTI self study plan is here! This one covers OSINT, pivoting, clustering/naming groups, and attribution. Enjoy!
#ThreatIntelligence
#CTI
23
259
805
I have bittersweet news: today was my last day with MITRE, and tomorrow I start as a Principal Intelligence Analyst with
@redcanaryco
. It's really tough to leave my MITRE teammates, but I'm excited to join the awesome team at Red Canary! (1/n)
132
22
690
JUST PUBLISHED. Today, we wrote a blog post about an incident this month where we saw Bazar + Cobalt Strike. We took action to help a medical center avoid a
#Ryuk
#ransomware
outbreak. We're sharing analytics that worked for us - we hope they help you too.
19
274
684
It appears there is a *second* Log4J vulnerability that requires another patch.
First CVE from last week:
New CVE today:
15
312
668
I have some exciting news - I am a Senior Fellow with the Atlantic Council's Cyber Statecraft Initiative! Thank you to the
@CyberStatecraft
for the opportunity. I'm excited to help bridge policy & practice...while working with very smart people!
74
28
549
It's an honor to be recognized as a 2020 Difference Maker! I'm grateful that I've made some small difference in such a rough year. I couldn't do any of this without this awesome community (that's you!) and my amazing teammates and mentors. Congrats to all the other winners!
76
14
548
New blog post! I'm often asked about getting started in
#threatintel
, so I compiled my perspectives. Featuring career paths from
@selenalarson
,
@chriscochrcyber
, and
@ForensicITGuy
. What other questions should I answer? What different views do you have?
20
214
522
What an honor to win the Security Changemaker award at the
@msftsecurity
Excellence Awards! Thank you all for being part of changing this community for the better, and I'm grateful to play a small role in that. ♥️
#RSAC
72
27
492
I have some REALLY exciting news... this year's
#CTISummit
is FREE!!!!!! You can get more info and register here: , and don't forget our CFP is open - please submit your awesome talks!
#threatintel
#CTI
#threatintelligence
15
235
480
OMG OMG
@C_C_Krebs
said my name!! And a nice shoutout to the wonderful
@MITREattack
team's work. Fangirling so hard right now! 😂
#CTISummit
13
9
466
This is one of the more detailed graphics I ever recall seeing from Microsoft that breaks down groups they track. This is worth a read.
#threatintel
Today we are releasing a new annual report highlighting
#cybersecurity
trends We have observed at Microsoft during the past year. More on Microsoft’s Digital Defense Report in my blog:
3
169
315
10
142
455
I love this tip from
@lennyzeltser
. It's incredible how many "extra words" you find when editing your writing.
13
131
444
An awesome young red teamer taking the OSCP asked a question that struck me: "If burnout is such a tough problem in the tech field, and especially security, why does
@offsectraining
push for this long, grueling, day-and-a-half-long exam?" Thoughts? I think he's right.
50
71
438
He should really smile more.
The FBI and our partners also announced the seizure of $6.1 million in funds traceable to alleged ransom payments received by Yevgeniy Polyanin, a Russian national who allegedly launched Sodinokibi/REvil
#ransomware
attacks against multiple victims.
14
155
312
24
50
434
The 2023
@redcanary
Threat Detection Report is here! I'm very proud of our team for producing this report. Check it out, I hope you'll find actionable takeaways for your team!
12
133
395
Note that
@CISAgov
updated their bulletin today: . New info includes what I highlighted below and some new mitigations. The challenge I'm seeing for analysts now is keeping up with changes. An ask for all: please highlight and share any changes to products.
12
159
386
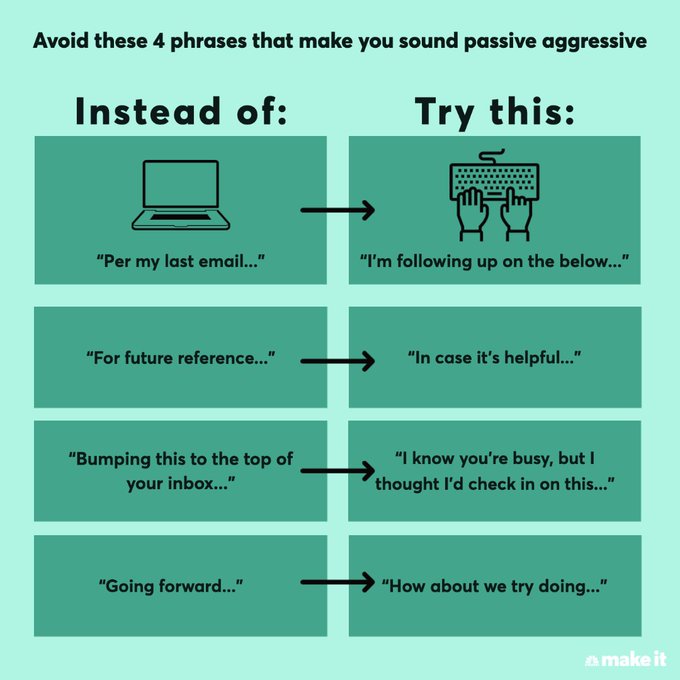
Uhh...just no. I haven't spent years coaching myself to be more direct just to have a random graphic I see on Twitter undo all that work. It's fine to be direct. If I say "Per my last email" I'm probably pissed, and you should know that.
30
24
393
Please note this is NICKEL not NICKELS. Very important distinction.
28
20
388
@ac1dgoddess
"I'm surprised to hear that and have a very different view. Could you walk me through how you got to that conclusion?"
8
6
348
I know a lot of excellent people are looking for jobs right now. We have several openings at
@redcanary
, including my peer, Senior Director of Detection Engineering, and a Threat Hunter on a team I lead. I hope you'll consider applying or sharing.
7
160
342
I have some exciting news...I'm a
@sansforensics
instructor for FOR578: CTI! Catch me as I team up with
@MalwareJake
in VA and
@RobertMLee
in DC, then it's all me in MD and TX. I can't wait to share my ❤️ of
#threatintel
with students!
@SANSInstitute
43
34
336
"I'm speaking." What every woman who has every been spoken over wants to say with the force
@KamalaHarris
just had. (Without being called any gendered insults...)
5
33
326
I saw some outstanding presentations at Derby, as well as some good ones that could have been outstanding with a few tweaks. Here's a quick thread on major things I saw.
#1
. Bigger fonts. Aim for at LEAST 20 point, but ideally larger. If you're doing demos, use a zoom tool. (1/n)
11
69
319
There's a lot wrong with this piece by
@allengwinn
, but this part is particularly egregious. Everyone makes mistakes, and every org has security incidents. Good luck hiring anyone, because people matching this description don't exist.
48
31
313
There is a LINE in the women's restroom at
#CYBERWARCON
. I repeat, a LINE. And everyone is happy about it.
@t_gidwani
#womenintech
12
23
302
I said it on
@riskybusiness
and I'll say it again:
@CISAKrebs
is awesome. He has the kind of character I endeavor to have. Speaking truth to power is a quality we should be so lucky to have in all public servants. Thanks for all you've done for the nation and community, Chris.
4
41
287
My boss said something useful to me: I'd rather have you do 100 things over the next few months than burn yourself out doing 20 things today. You can accomplish MORE over time if you stay at a manageable pace for you!
8
33
283
I'll attempt to live tweet this awesome webcast from
@Wanna_VanTa
and
@x04steve
on Ryuk and UNCs behind them! Roughly 1/5 ransomware intrusions have been related to Ryuk.
@Mandiant
@sansforensics
6
69
264
When you see "Cocaine Bear" trending and are relieved it's not a new
@CrowdStrike
group name.
18
45
264
A brief thread on the
@CrowdStrike
blog on SUNSPOT...as I read it. This confirms CrowdStrike was one of SolarWinds' IR firms, which we'd heard rumblings of before.
7
92
263
This is interesting research that's worth reading. I'd encourage readers to also consider what's NOT here - these groups didn't use LLMs to make new malware or find zero-days. They used them to help research and write scripts. I'm not panicking about this...
7
53
253
I'm honored to join the CSRB, and I look forward to working with my fellow members to drive positive change in the cybersecurity community.
23
16
251
Compromises happen to everyone, and it's how you respond that matters. Nice work to
@TalosSecurity
for sharing a detailed blog post on what happened during their incident: - along with a clear statement:
5
69
248
I often cite the stat that women make up only 11% of the
#infosec
workforce. But it becomes so real when I'm constantly the only woman in the room. I adore my male colleagues, but this has got to change for the good of the industry. Let's do this.
#womenintech
#bethechange
19
48
245
With the heat index over 100 degrees, it's a great day to dive into
@megan_roddie
's new book! I love to see threat severity as part of the triage process. 🔥Threat Intelligence + Detection Engineering = ❤️!
5
46
227
This is cool. I like that
@CISAgov
regularly recommends private sector blogs. For a long time the US government suffered from "not invented here" syndrome, and I'm happy to see signs of change.
⚠️
@CISAgov
recommends network defenders review the Microsoft blog on destructive malware targeting Ukrainian organizations.
#Cybersecurity
#InfoSec
12
227
414
7
25
243
Impostor syndrome mitigation of the day: when you kick ass at something, write it down. Next time you're flipping out about how you suck and know nothing, consult your "why I kick ass" list. Having raw data can help the fight against your self-defeating brain.
#impostorsyndrome
12
55
238
As you're reading this, note this point: adversaries likely had control of the AD server already. They were already in. There's a broader intrusion chain beyond just the wiper, it just isn't publicly known yet. I'm watching for any details on what happens BEFORE wiper deployment.
7
60
239
Here's a thread of resources where you can get up to speed on SCATTERED SPIDER, UNC3944, Oktapus, and Muddled Libra. (which we KNOW are not exact overlaps, but we're doing the best we can, okay??!?) Starting with
@CrowdStrike
, good one from
@realparisi
6
81
238
So...
@meansec
and I have some exciting news....WE'RE SPEAKING AT BLACK HAT!!!!!
#BHUSA
@BlackHatEvents
@MITREattack
28
11
236
I'm often asked how to go about starting a CTI team, so I wrote down a few high-level thoughts on what to consider. We also shared a few examples of how we've navigated these areas with our own
@redcanary
Intel Team as well. We hope this is helpful!
New blog from
@likethecoins
: While ingesting feeds of indicators or identifying state-sponsored adversaries can be part of your approach, cyber threat intelligence is a much broader field than any specific tool or data source.
3
60
163
9
60
233
The
@redcanary
2022 Threat Detection Report is here! We're sharing our insights into trends, threats, and techniques in the hopes it helps you improve your security posture. Don't forget to check out the playlist too!
7
99
233
A threat of thoughts + actionable detection ideas from the latest Microsoft
#Solorigate
post... ... this is a sweet diagram and hopefully helps make clear the different ways you could be impacted. Not every victim makes it past initial C2.
6
79
230
I don't want to fangirl about
@HuntressLabs
too much, but I'm so grateful for their candid approach - this is what this community needs. Great webinar earlier today!
13
24
231
On my way to Singapore to teach
#FOR578
! One of the cool things about teaching is that I get to visit new places. I would love any recommendations on what I should see or do while there!
34
3
229
I am proud that I was part of the
#RansomwareTaskForce
that released a report on combating ransomware today. My thoughts are here: . And the report is here:
10
74
226
I'm generally a pretty positive person, but it's Festivus, so let's blow off some steam and air our
#threatintel
grievances. Threat intel feeds are just data feeds, they're not threat intel. Please stop naming groups after malware, it's confusing AF.
30
34
215
I always thought I would be in
@Forbes
because I won the lottery...but instead, it's because of
@MITREattack
! It was great chatting with
@robertvamosi
a few months ago, and I can't wait to speak with
@meansec
on Wednesday at
#BHUSA
!
@BlackHatEvents
12
36
213
Exciting news - there are new FREE
@MITREattack
training courses through
@cybraryIT
! The courses are totally free, and the optional certifications through
@MITREengenuity
have a fee. Congrats to the team on making this happen!
0
81
213
I'm very happy to see this blog post from
@FireEye
on naming actors! If you're wondering why the actor behind the the
#SolarWindsOrion
compromise is named UNC, read this.
3
68
203
Nice blog from
@datadoghq
on the OpenSSL vulnerability - their description and graphic helped me better understand how this works. (h/t
@ForensicITGuy
)
3
84
203
If you're still focusing on PrintNightmare, it's time to shift and look at this NOW. Multiple reports are coming out, leading to increasing confidence there is something bad happening here.
6
77
199
Please don't retweet or trust random tweets from people on the Internet you don't know. (Including this one if you don't trust me.) Especially about threats exploiting
#log4j
. There's a lot of unverified junk that is just causing more fear, uncertainty, and doubt. NOT HELPFUL.
7
24
198
We released our
@redcanary
Threat Detection Report today! We hope it's useful to help you detect more adversaries. I wanted to highlight a couple things I'm excited about in a thread...
8
67
202
I don't know exactly how we handle this as a community. I do know when people like
@magpie2800
and
@chadloder
speak up, I feel like I'm not alone and it's not just me. If we show compassion and believe women, I think we can all help make this better. (5/5)
19
6
193
It's here! I'm proud of the whole team who worked for months on this report. I hope y'all find it helpful, it's full of threat analysis and recommendations to take action to improve your security posture!
6
39
195
Thank you all so much for coming to my
#Shmoocon
talk on threat modeling! You can check out my slides (complete with references) here: . Thanks to
@heidishmoo
,
@gdead
, and the amazing
@Shmoocon
volunteer crew for having me and making this event possible!
7
66
193