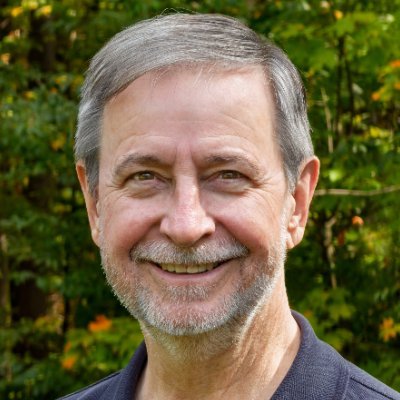
Nick Carr
@ItsReallyNick
Followers
38K
Following
54K
Media
2K
Statuses
13K
Tech Director / Threat Intelligence at Microsoft. Previously, Director of Incident Response & Intel Research at Mandiant. Former Chief Technical Analyst at CISA
Virginia, USA
Joined September 2009
Sometimes I take for granted that on our team we have real-time visibility into hundreds of simultaneous intrusions from every APT & FIN group on the planet. Including many right now from apex threat actors that others wait a lifetime to experience. I look at new intrusion sets
4
8
152
FSB phoning it in on disguises.
I feel like there are a lot of as-yet-unknown twists to this story - one to keep an eye on. Russian activist held in Poland admits he worked as FSB agent, court papers say https://t.co/sR6EPC65RZ
8
35
383
I got enough requests that I decided to experiment with Office Hours. This is an opportunity to discuss a wide range of topics, including: - PowerShell - Technology - Science - Philosophy - Whatever I look forward to connecting with you. https://t.co/4xuzV26dw6
2
3
31
Luxury just got more precise! LVMH’s Watch Division is taking a minority stake in Swiss movement maker La Joux-Perret from Japan’s Citizen Group, deepening its access to high-end, Swiss-made movements at scale. This strategic move strengthens the backbone of TAG Heuer, Hublot,
1
1
1
@IceSolst @taviso @filpizlo I think you've missed some unintended emergent behaviors. Our industry rewards visibility, not responsibility. You’re judged by GitHub stars, conference selfies, and CVE counts; most of all, bug bounties. Literally rewarding researchers to pop, drop, and bounce. Publishing 0-days
18
41
289
To clarify: this change is not related to any security concern, and only impacts Yubikeys and passkeys - not other 2FA methods (such as authenticator apps). Security keys enrolled as a 2FA method are currently tied to the twitter[.]com domain. Re-enrolling your security key will
By November 10, we’re asking all accounts that use a security key as their two factor authentication (2FA) method to re-enroll their key to continue accessing X. You can re-enroll your existing security key, or enroll a new one. A reminder: if you enroll a new security key, any
174
406
1K
explanation:
@ItsReallyNick Getting off of Twitter enrolled keys so we can stop doing hacky things for domain trust. Physical security keys are cryptographically registered to Twitter’s domain and need to be re-enrolled under X.
1
2
27
@ItsReallyNick Getting off of Twitter enrolled keys so we can stop doing hacky things for domain trust. Physical security keys are cryptographically registered to Twitter’s domain and need to be re-enrolled under X.
6
10
159
This seems odd
By November 10, we’re asking all accounts that use a security key as their two factor authentication (2FA) method to re-enroll their key to continue accessing X. You can re-enroll your existing security key, or enroll a new one. A reminder: if you enroll a new security key, any
15
34
860
Probably one of the biggest losses of US cyberweapons in years. 👇 All from private companies... ❓How were stolen capabilities used? ❓Were NSA etc ops burned? ❓Were they turned against Americans? Raises alarming questions about for-profit offensive sector's reliability.
NEW: The U.S. govt accused Peter Williams, ex general manager of hacking tool maker L3Harris Trenchant, of stealing trade secrets and selling them to buyer in Russia. Earlier this year Trenchant investigated a leak of internal tools. It's unclear if the investigation is related.
6
80
239
Chinese authorities allege a 27-month NSA operation against the China's National Time Service Center. Initial credential theft apparently via a smartphone-messaging exploit. They relese technical details, including information about 80+ remote logins between April 11 and August
15
165
710
FWIW, the conclusion I increasingly believe is that measuring the security state of an environment is somewhat like measuring human health: While there's never going to be one number or even a few numbers that are simple yet comprehensive, good metrics are still indispensable.
Are there security program metrics you actually like? Other than misleading stats that lie to leadership, it’s hard to find meaningful metrics that assess program success
4
4
38
Just released: Android’s Age Signals API (beta) – to attempt to comply with various new U.S. state age verification requirements… I’ve pretty much given up trying to maintain legacy mobile app side projects.
3
0
6
@chrissanders88 Classic artifact triage moment - no memory, no EDR, just bread crumbs. Start with the filesystem residue: 🔹 $MFT + $LogFile - look for update.dll create/delete timestamps, sequence numbers, and parent dir handles. 🔹 USN Journal - confirm write/delete ops, session IDs, and
4
6
71
Friday marked the end of my 13 year journey with Mandiant/FireEye/Mandiant/Google. 1/
8
2
51
We have two open roles at @proofpoint 🥳 Along with the previously mentioned engineering role, we also have an open Threat Researcher role on our e-crime research team: 👇 Come hunt bad guys with me. https://t.co/nhLJmwfuWq
We're hiring on our Threat Research team at @proofpoint! If you enjoy making threat actor's lives more difficult (and you want to work with me and lots of other smart people) apply below! 🤓 https://t.co/hUgwJCYdzv
3
13
58
From S1ngularity to Shai-Hulud, NPM is the core topic we cover in episode 2 of The Permiso Security podcast
2
2
12
⚖️🔗 https://t.co/UFtjiPOW5L Side note: @AlinaHabba - we haven't caught up since Lehigh (worlds collide!), but cool to see your quote here: "The charges against Jubair announced today are the result of a lengthy investigation into particular cyber threat actors, often referred to
justice.gov
A complaint filed in the District of New Jersey was unsealed today charging Thalha Jubair, a United Kingdom national, with conspiracies to commit computer fraud, wire fraud, and money laundering, in...
0
0
3