Thomas Roccia 🤘
@fr0gger_
Followers
25,284
Following
1,707
Media
1,894
Statuses
9,683
Sr. Threat Researcher @Microsoft , Malware Warlock, Threat Intel, Python🧡- Former @McAfee_labs , Goon @Defcon , Creator of #UnprotectProject - Tweets are my own
🇫🇷-🇦🇺
Joined January 2011
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
Rio Grande do Sul
• 181351 Tweets
Madonna
• 125006 Tweets
NO RDM COM CAIO E LUAN
• 107515 Tweets
Tottenham
• 76497 Tweets
Bardella
• 70169 Tweets
Spurs
• 69184 Tweets
Leverkusen
• 57740 Tweets
Palmer
• 54819 Tweets
#CHETOT
• 53101 Tweets
Hayer
• 36328 Tweets
Boris Johnson
• 29005 Tweets
Ange
• 27421 Tweets
Aston Villa
• 27034 Tweets
bruno mars
• 26551 Tweets
Ole Miss
• 23292 Tweets
Cucurella
• 17179 Tweets
$AAPL
• 16514 Tweets
Kaizer Chiefs
• 16003 Tweets
Chalobah
• 15753 Tweets
憲法記念日
• 15612 Tweets
#SVGala9
• 15027 Tweets
Miri
• 14779 Tweets
Mudryk
• 14713 Tweets
Xabi Alonso
• 12893 Tweets
Caicedo
• 12777 Tweets
Last Seen Profiles
Pinned Tweet
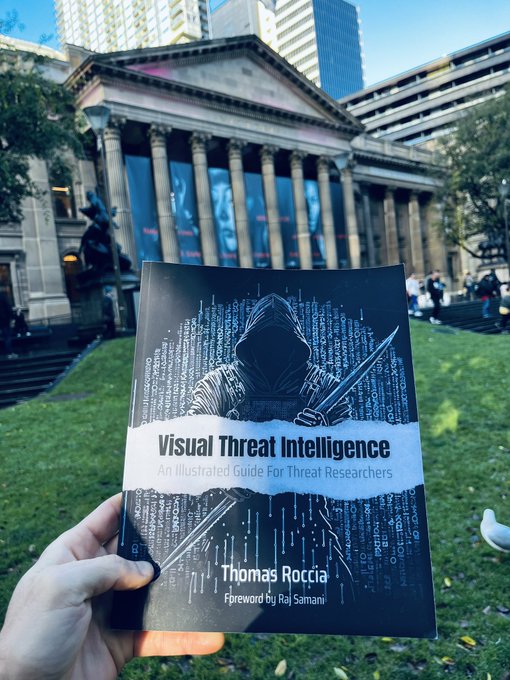
🤓Excited to announce that Visual Threat Intelligence is now available as an ebook! Paperback will follow in a few weeks. There is a 15% launch discount on the eBook with code INTELLALLTHETHINGS. Valid for one week!
#infosec
#threatintel
#cybersecurity
👇
51
137
409
Windows privileges determine the type of operation a user account can perform on the OS and are sometimes abused by attackers. If you've ever wanted to know what a privilege is for, I've created the ultimate cheat sheet that shows all Windows privileges on one page!🤓
#infosec
20
914
2K
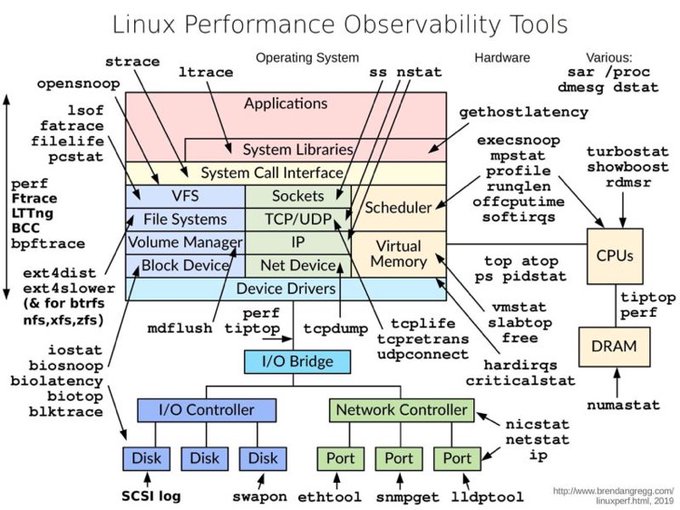
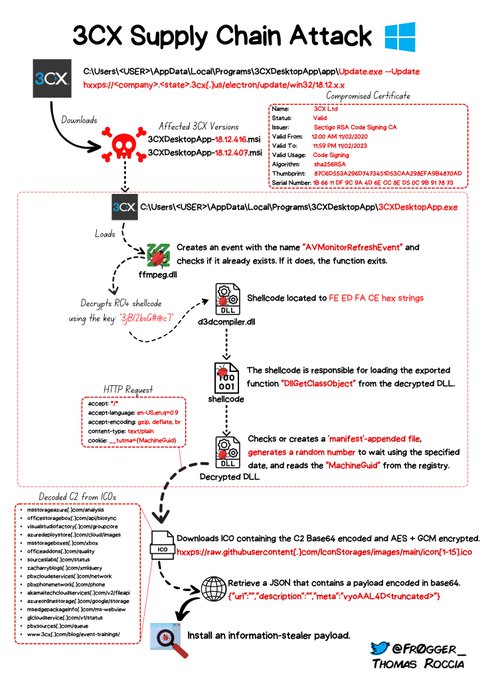
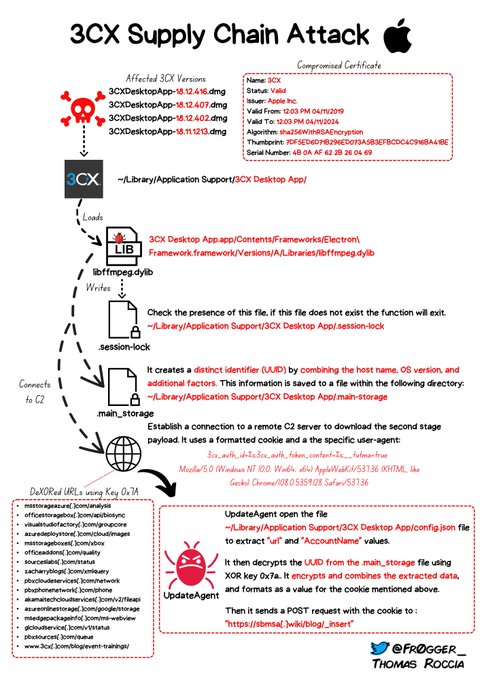
🔍If you are looking for a comprehensive overview of the current
#3CX
supply chain attack, I created a diagram that shows the attack flow!💥I'll update as soon as the analysis progresses. Stay tuned for the MacOS edition!
#cybersecurity
#infosec
#supplychainattack
#3CXpocalypse
24
516
1K
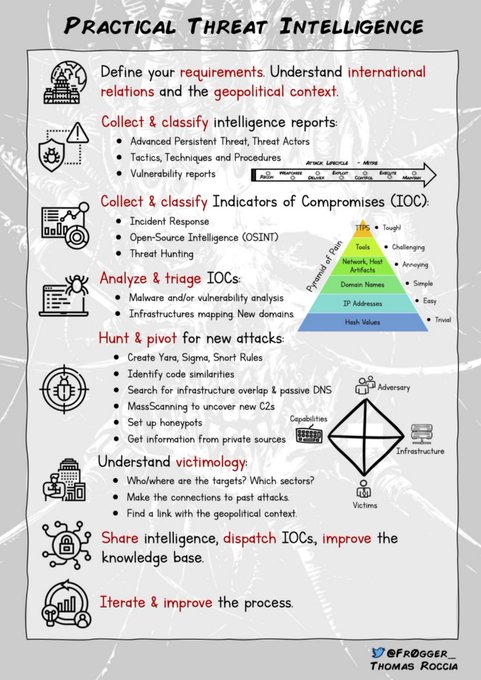
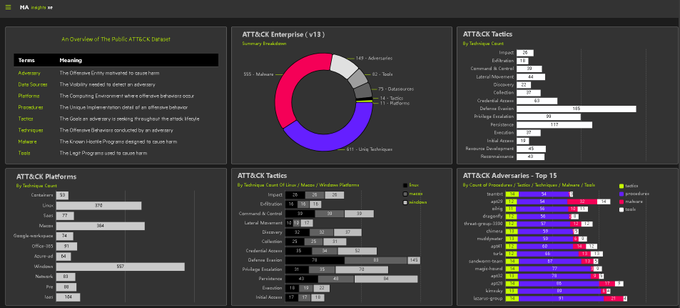
Visualizing
#cybersecurity
concepts can be a great way to learn more about specific tools, methodologies, and techniques! Here is a thread that shows 6 useful infographics on threat intelligence and related topics!🧵👇
#infosec
#threatintel
1⃣ - Practical Threat Intel
20
394
1K
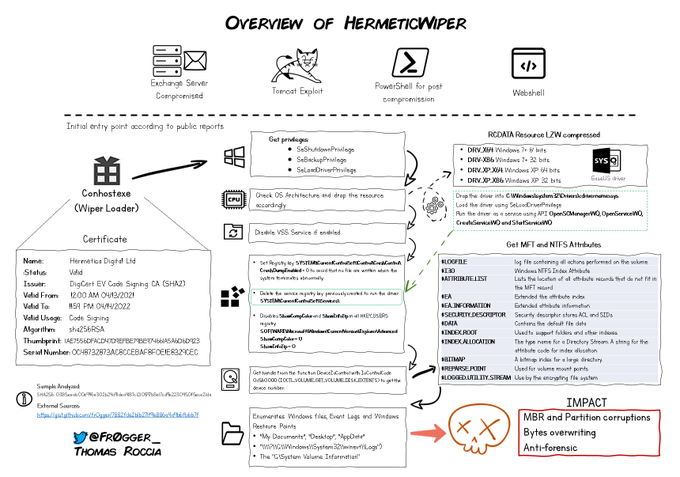
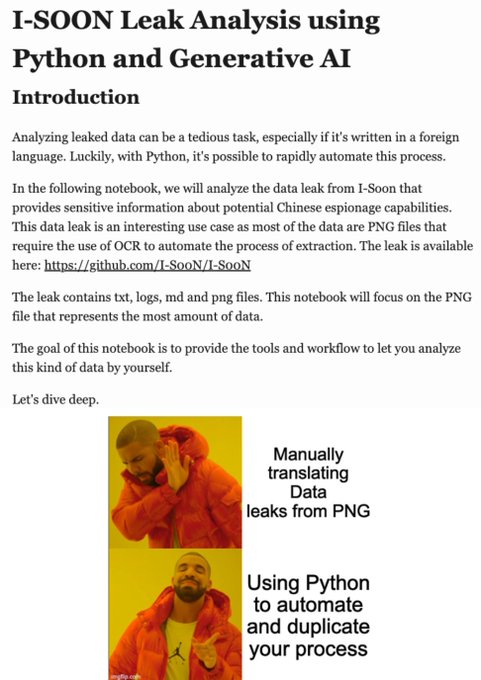
I briefly analyzed
#HermeticWiper
to give an overview of its capabilities. I have deliberately omitted some details for better understanding. I'll update the graphic as my analysis progresses! Hope this will help you understand better the attack!
#infosec
#malware
#cybersecurity
12
489
1K
🤗I've written a book! Let me introduce you "Visual Threat Intelligence"
You can register now to stay updated on its release and learn more about it in the link below. I really hope you'll like it! 🥹
#VisualThreatIntelligence
#infosec
#threatintel
👉
68
244
1K
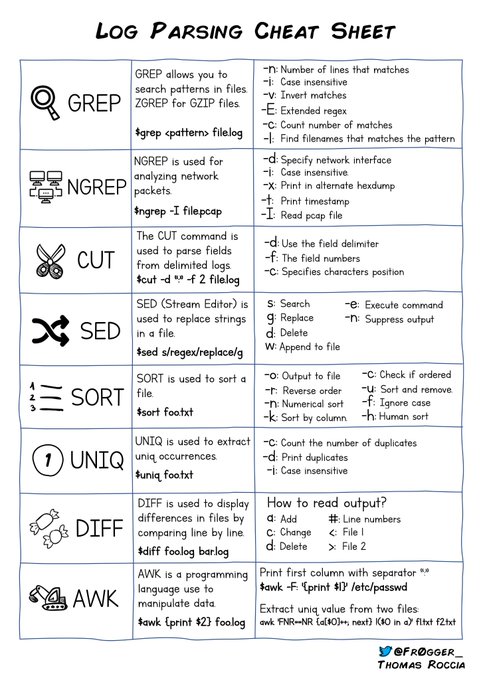
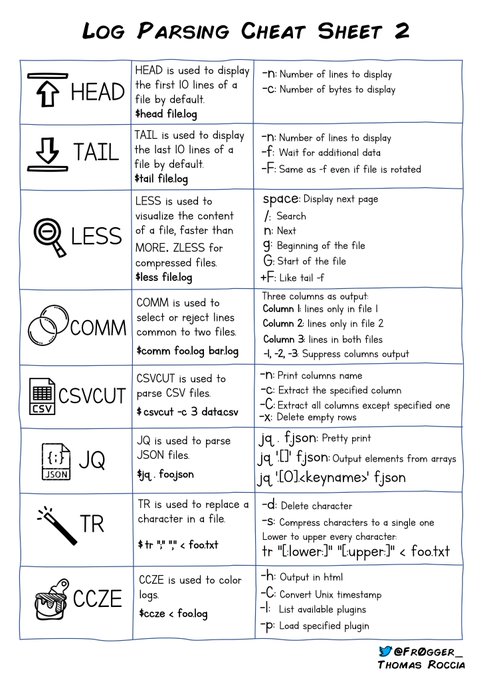
Here is part 2 of my log parsing cheat sheet for your office! Let me know your favorite tools or your ninja commands! 📌
#DFIR
#ThreatHunting
#infosec
#Linux
11
261
917
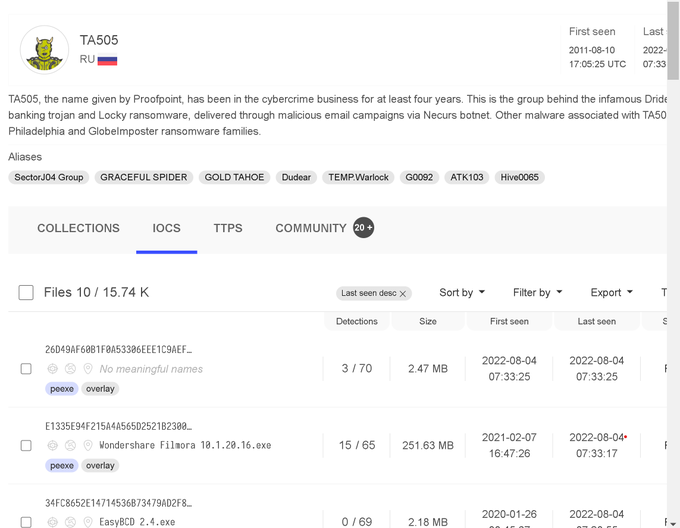
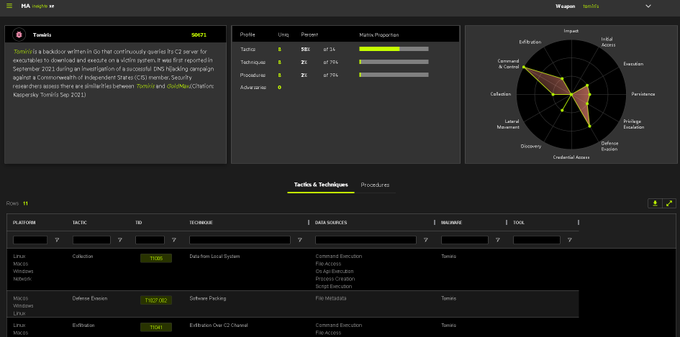
There is a new feature on
@virustotal
, you can now browse IOCs by threat actors and also get TTPs, pretty cool👌
#ThreatIntelligence
#malware
#ThreatHunting
#infosec
16
278
882
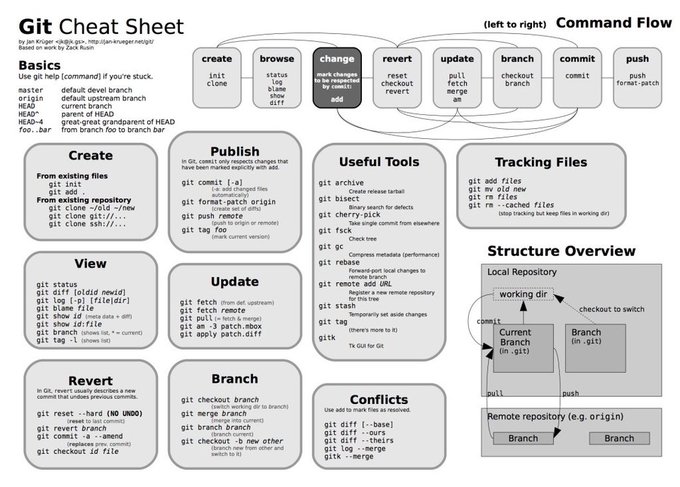
If you use Git on a daily basis, this cheat sheet is very useful!👍
#github
#developers
#git
#tuesdaymotivations
17
242
808
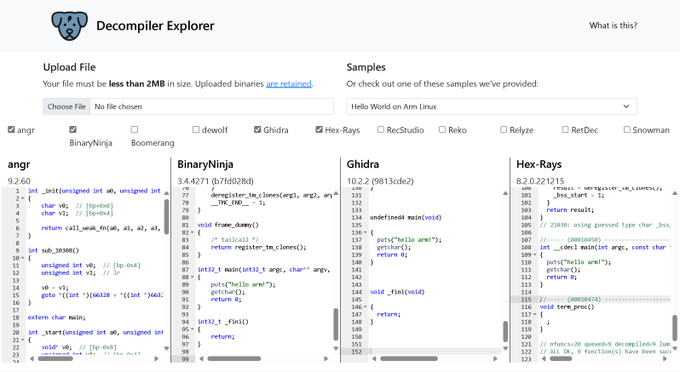
Just wrote a new reversing tips about IDAPython! Also linked this useful cheat sheet by Pavel Rusanov.👌
👉 blog:
🤓 You can follow me for more RE tips in the future!
#Infosec
#ReverseEngineering
#CyberSecurity
9
282
793
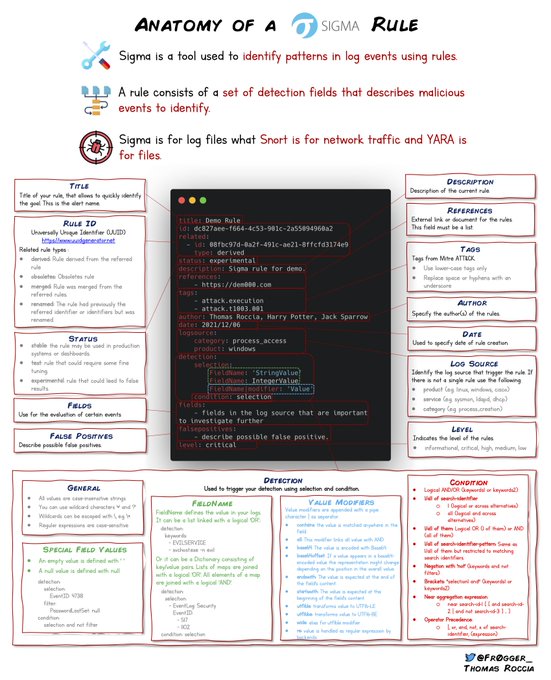
I created a new cheat sheet for Sigma Rules, easy printing for your office! 🤓
@sigma_hq
@cyb3rops
#infosec
#threathunting
More of my cheat sheets here ⬇️
11
238
663
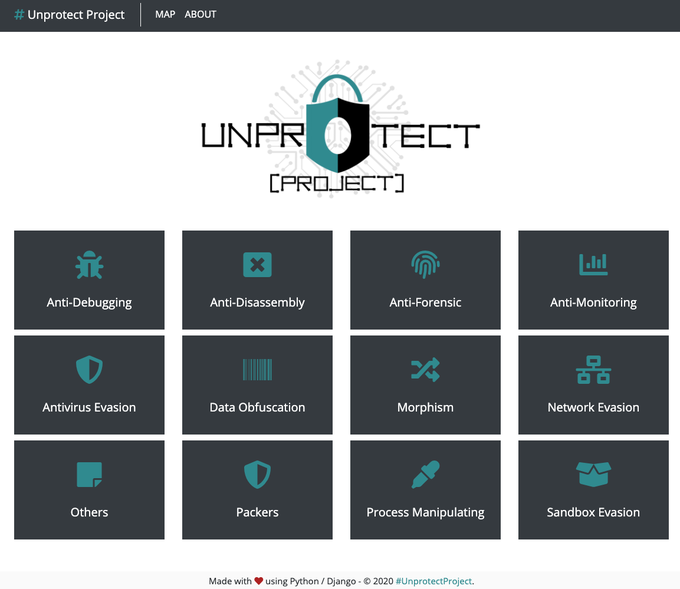
I have released a
#malware
evasion techniques database with the contribution of my friend
@DarkCoderSc
! Check out this post for more details! Feedback welcome, RT if you find it useful! 😊
➡️Blog:
➡️Database:
5
299
562
I published a blogpost that presents ten useful python libraries that I use for malware analysis and reversing (with code examples)!
Which one are you using the most? 🐍
#python
#malware
#cybersecurity
#infosec
5
208
532
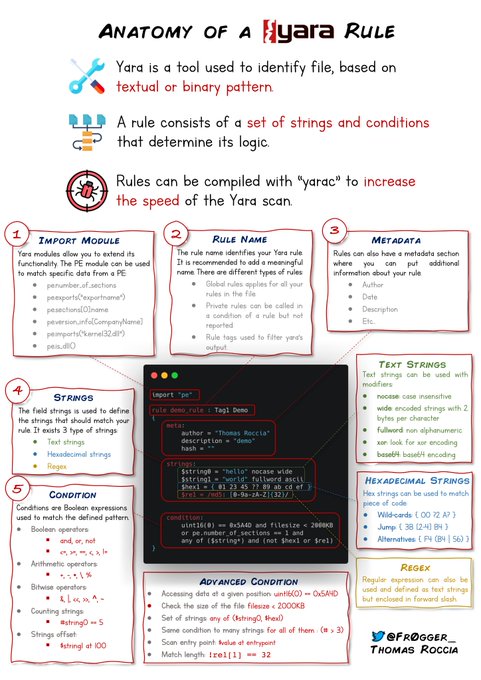
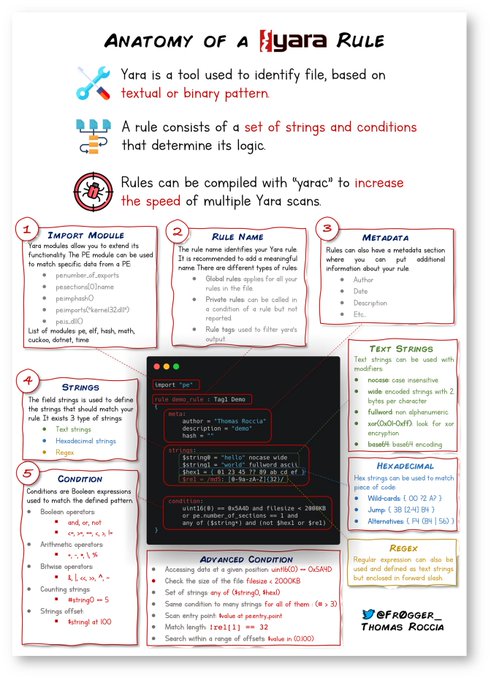
I have created a cheatsheet for Yara rules that can be printed for your office! More cheatsheets are available on my Medium. ⬇️
#infosec
#Malware
@yararules
3
168
483
Interesting new project: 'LOLbin-CTI Driven'. It's an app that visually demonstrates how a LOLbin can be used during an intrusion. And it uses the STIX format. 👍
#infosec
#malware
#lolbin
#threatintel
👉App:
👉Project:
2
171
477
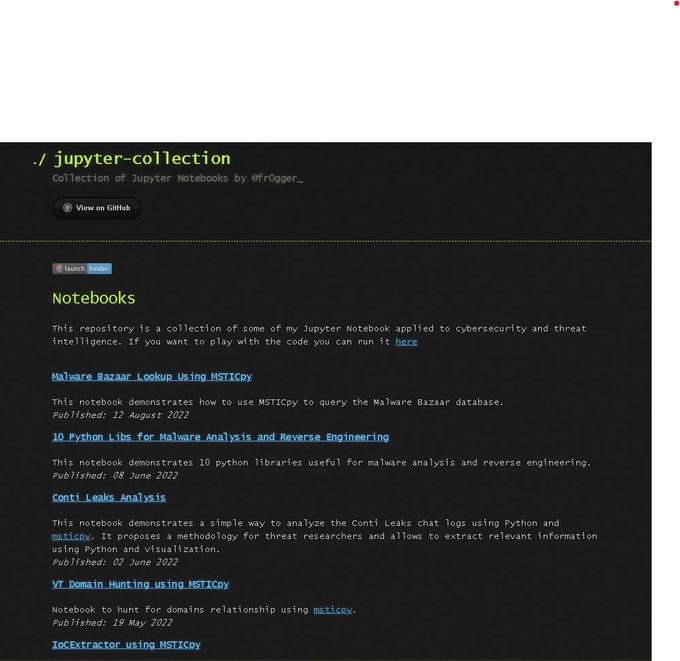
I work with
#Jupyter
notebook on a daily base for analysis,
#threatintelligence
and creating workflows! Few months ago, I created a Github page to share some of them! I update it periodically!
Here are the notebooks available 🧵👇
#infosec
#Python
14
139
460
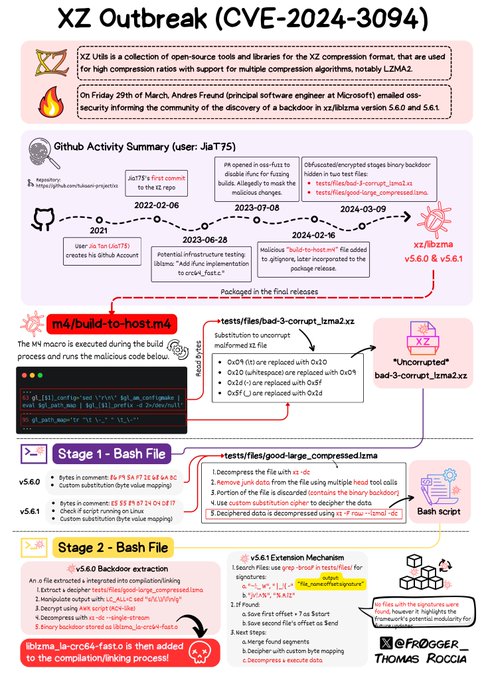
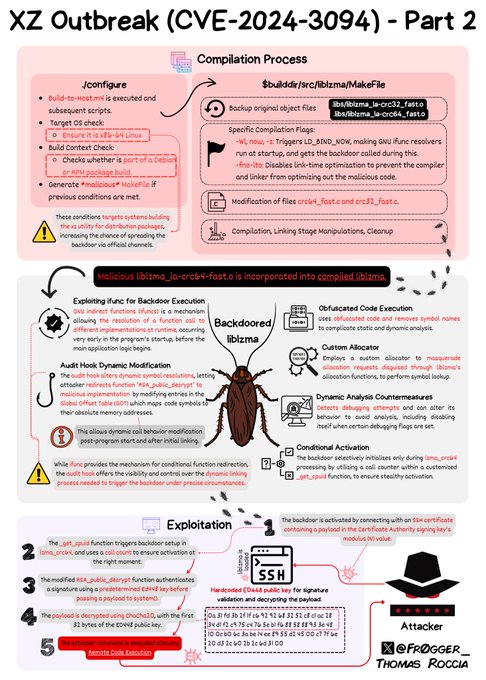
Kudos to the amazing researchers that published their analysis:
- by
@gynvael
- by
@thesamesam
@social
.treehouse.systems
- by
@eb
@social
.coop
- by
@AndresFreundTec
-…
1
54
462
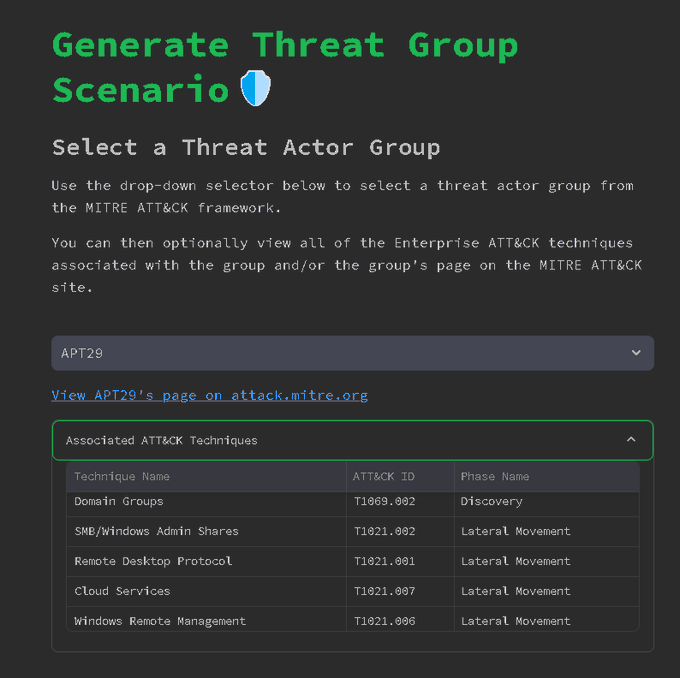
I just came across a tool called AttackGen. It's a simple tool that generates incident scenarios based on a Threat Actor and suggests simulations and possible detections at a high level.
#llm
#python
#threatintel
👉 code:
👉 app:
5
128
426
I created another infographic to provide an overview of the threat intelligence process! Stay tuned for the next releases!
#ThreatIntelligence
#CyberSecurity
Thanks to
@gynvael
and
@pagedout_zine
for allowing me to use the design for the background! 🤩
6
145
375
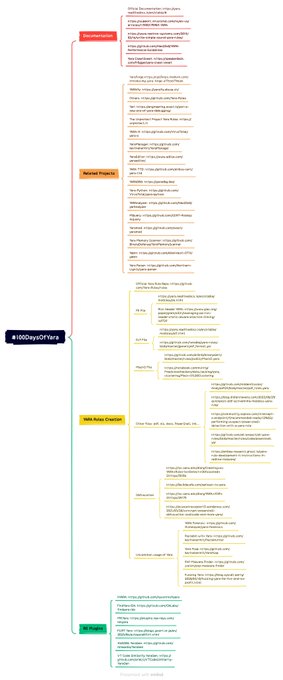
#100DaysofYara
Day 8: Introducing Yara Toolkit, an online app for all things Yara! 🚀 (It's not really day 8, I spent my weekend on it 😅)
Since we're still early in the challenge, I thought it might be useful for some of you to have a dedicated portal, so I created Yara Toolkit…
8
113
354
🎉Professional announcement: I am thrilled to announce that I recently joined
@Microsoft
as Senior Security Researcher in the Defender Research Team! I will be joining the Melbourne office in the coming months! 🇦🇺🤩
#malware
#ThreatHunting
@msftsecurity
41
16
335
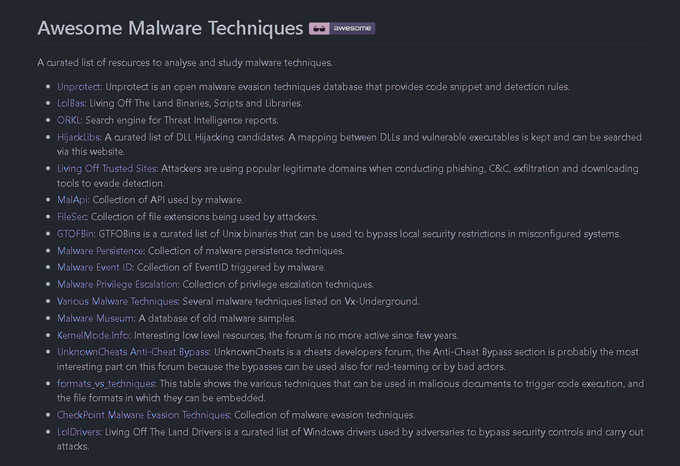
🧵Thread: 10 underestimated resources about malware techniques.
This is a list of various resources to learn more about malware techniques, how to analyse them and how to improve your detection! 🤓
#infosec
#malware
#threatintel
#malwareanalysis
#cybersecurity
9
129
336
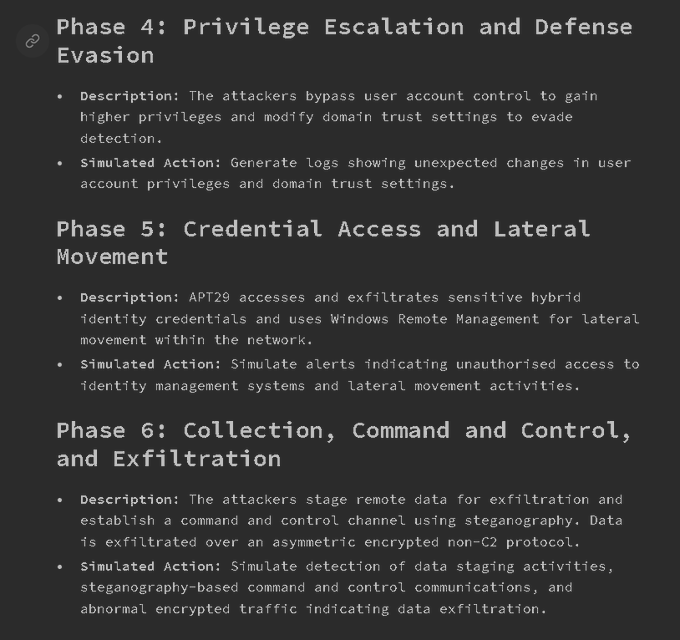
Microsoft DART team described a new malware named Tarrask attributed to Hafnium. This malware creates hidden scheduled tasks, and subsequent actions to remove the task attributes as anti-forensic technique. 🧐
#infosec
#UnprotectProject
#cybersecurity
2
101
308
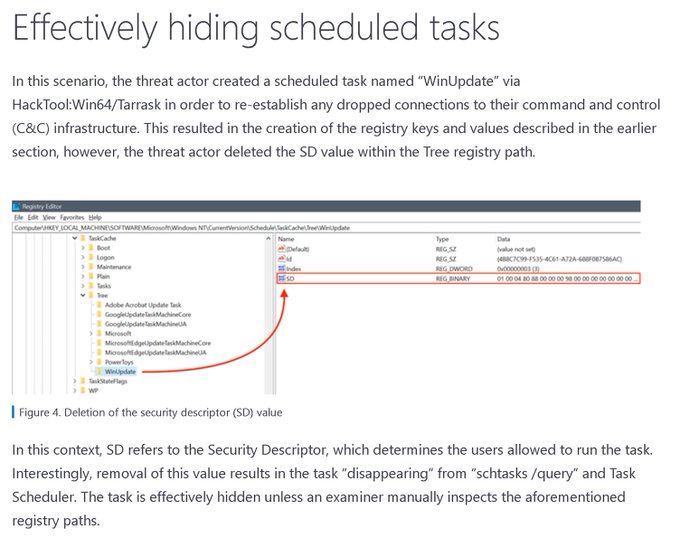
If you missed it, here is the ultimate IDA Pro Shortcut cheatsheet! Happy reversing!
#reverseengineering
#idapro
#infosec
6
98
292
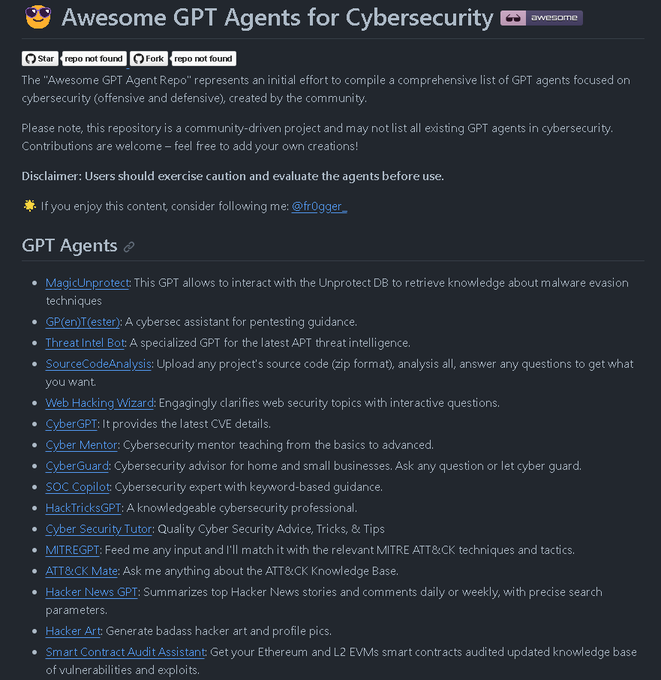
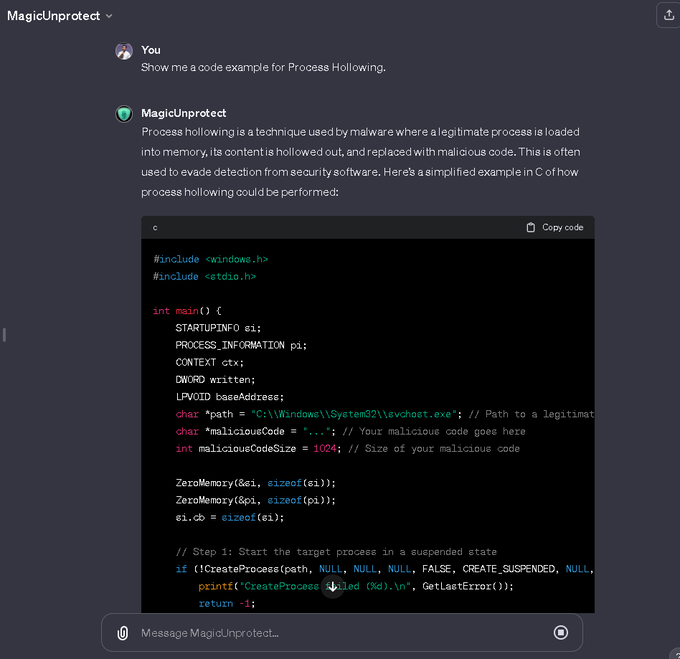
I did a thing! I created my first GPT named "MagicUnprotect". This GPT is connected to the
#UnprotectProject
knowledgebase. You can ask anything related to evasion techniques! I'll share it when the test is done 🤓
#infosec
#malware
@DarkCoderSc
7
69
291
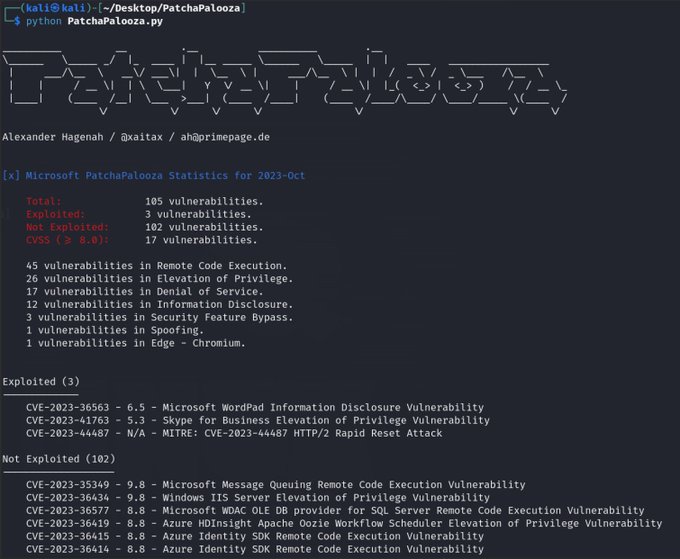
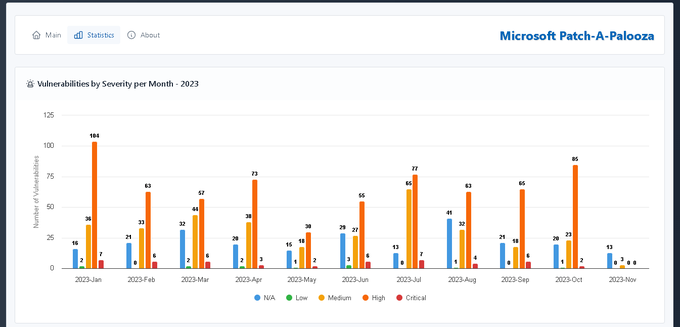
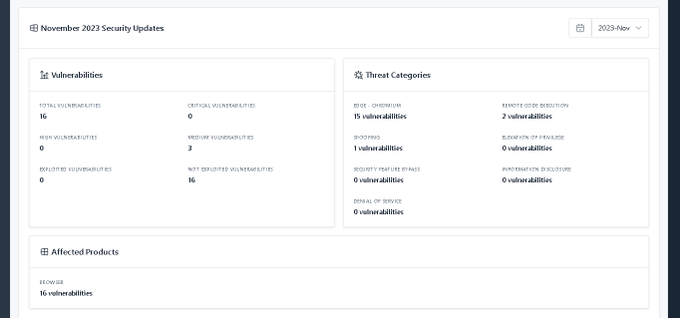
This new tool is pretty cool, it helps you creating an overview analysis of Microsoft's monthly security updates! And there is an online version! By
@xaitax
🤩
#infosec
#msrc
#Microsoft
2
76
286
🍏Diving into the 3CX Mac OS edition analysis, here is the preliminary diagram of the attack flow. I hope it will give you a broader understanding! I'll update as the analysis progresses! 💥
#3CX
#3CXpocalypse
#infosec
5
93
278
I just wrote a quick tips about how to disable ASLR in a PE when reversing.
#reverseengineering
1
83
272
In February, the
#ContiLeaks
was revealed. I wrote an in-depth blog post that shows a methodology for analyzing Conti Jabber logs using Python. Have a look as the code can be applied to multiple data sources.
#threatIntelligence
#infosec
@MsftSecIntel
👇
6
82
270
Binary diffing is a great way to visualize differences and similarities in malware samples. I just posted a blog post explaining how to spot code similarities and take advantage of it to hunt for other malware.
#CyberSecurity
#ThreatIntel
2
103
259
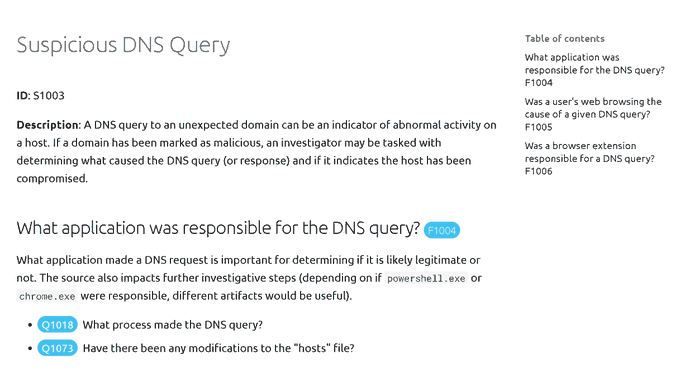
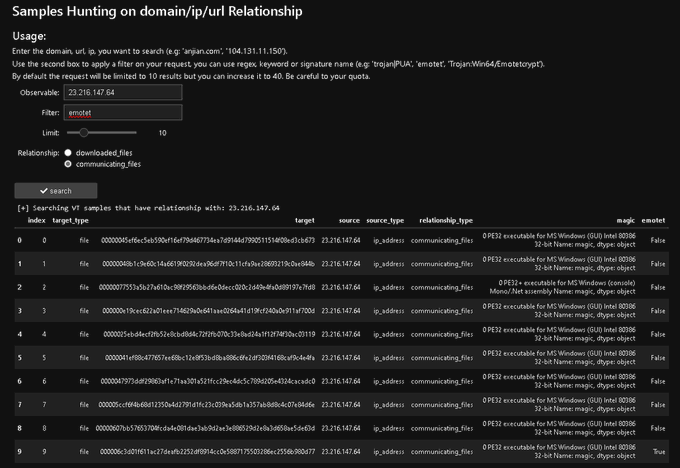
I coded a python tool for domain hunting relationship using
@virustotal
and
@msticpy
! You can play with it in binder and adapt the code if you like! 🤓
@msticpy
#python
#Jupyter
#ThreatHunting
cc:
@ianhellen
🔬Notebook:
3
59
259
Day
#1
: Starting the
#100DaysOfYARA
challenge with a bit of planning and visualization. Hopefully, this mind map will help you by providing a better overview and some ideas for the challenge! 🤓💡
#infosec
#yara
👉 Blog:
4
70
256
Last week, I wrote a tiny tool based on the
@virustotal
API v3 to generate
#malware
hunting notification report and send it over email, Slack or Telegram! It helps to have a single collection point for multiple hunters!
4
127
255
I saved another thread in a blog format, six of my infographics for Threat Intelligence and Threat Hunting. Check out the blog 👇
#threatintel
#threathunting
#infosec
#yara
#sigma
6
79
245
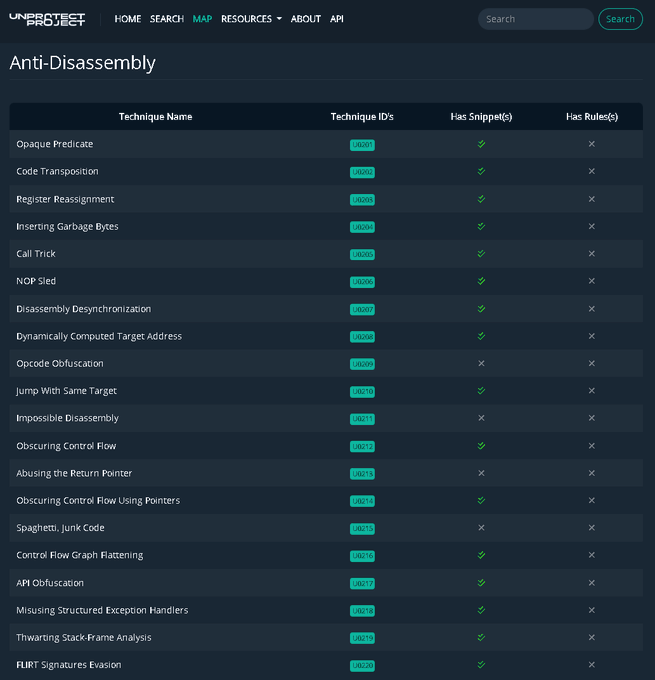
After a few months of work, we are pleased to announce the new version of Unprotect: your catalog of malware evasion techniques!🤩🧵👇
#unprotectproject
#infosec
#malware
#cybersecurity
@DarkCoderSc
11
117
236
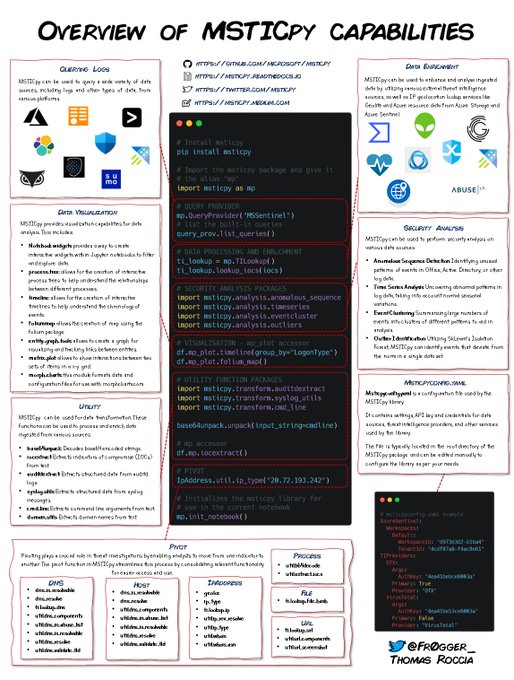
⚡️MSTICpy is a powerful python library for threat intelligence and threat investigation! I created a new security artwork for a brief overview.
Learn more with
@ianhellen
&
@PeteABryan
at BlueHat for an in-depth look. 🤓
@msticpy
#ThreatIntel
#infosec
#python
@MsftSecIntel
0
92
236
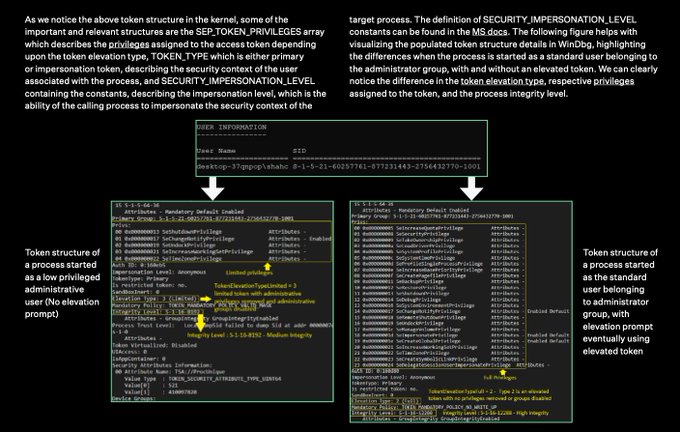
We recently published a detailed report on Access Token manipulation and privilege escalation! 🤓
@McAfee_Labs
4
89
233
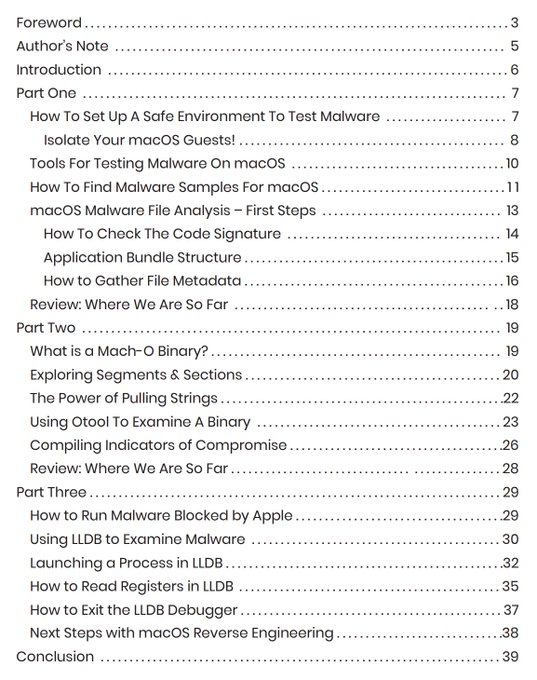
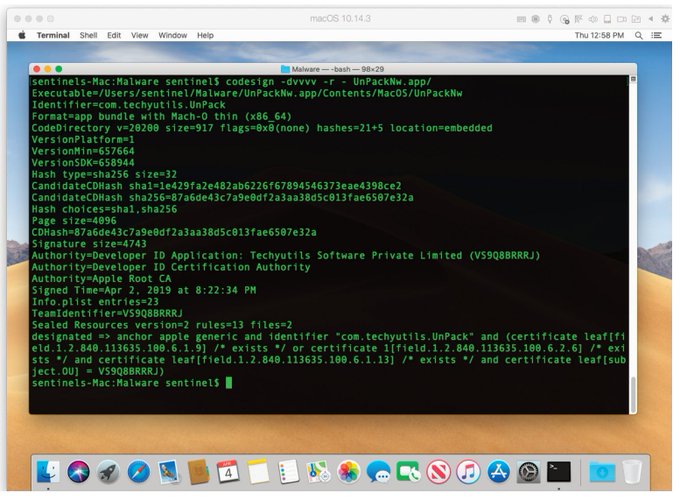
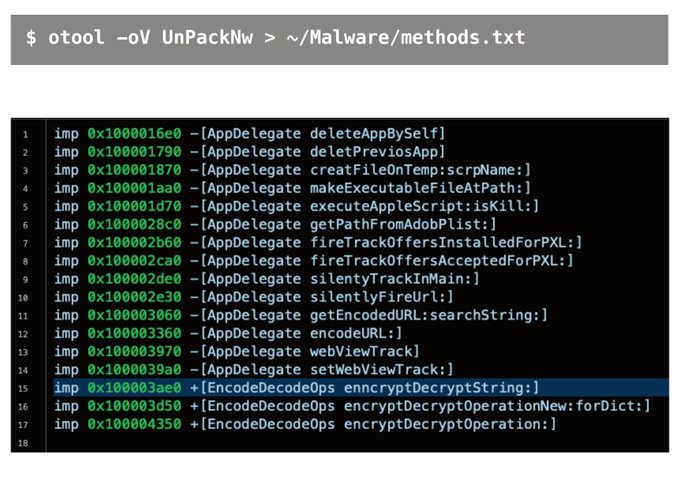
Very cool resource to start analysis MacOS malware by
@SentinelOne
. From configuring a safe analysis environment to Mach-O binary analysis and dynamic analysis!🙂
#malware
#macos
#reverseengineering
2
74
232
💻I've published a new blog post where I discuss practical use cases of LLM applied to threat intelligence. Check this out for a real talk about LLM usage for threat intelligence! 🤓
#infosecurity
#threatintel
#cybersecurity
11
76
224
I just published a basic Reverse Engineering Tips yet useful to reconstruct enumerators with IDA.
#ReverseEngineering
#idatips
1
65
220
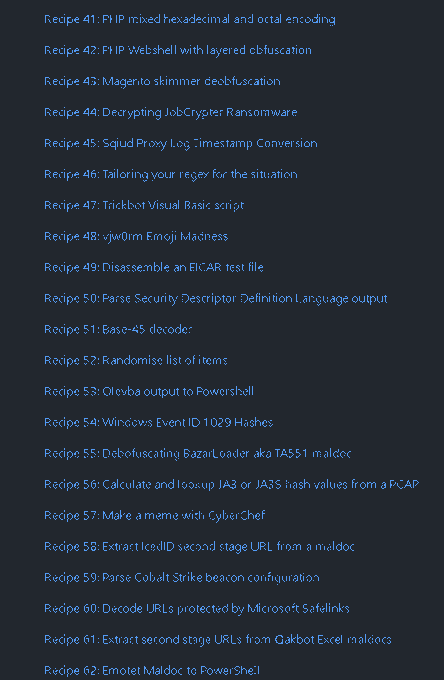
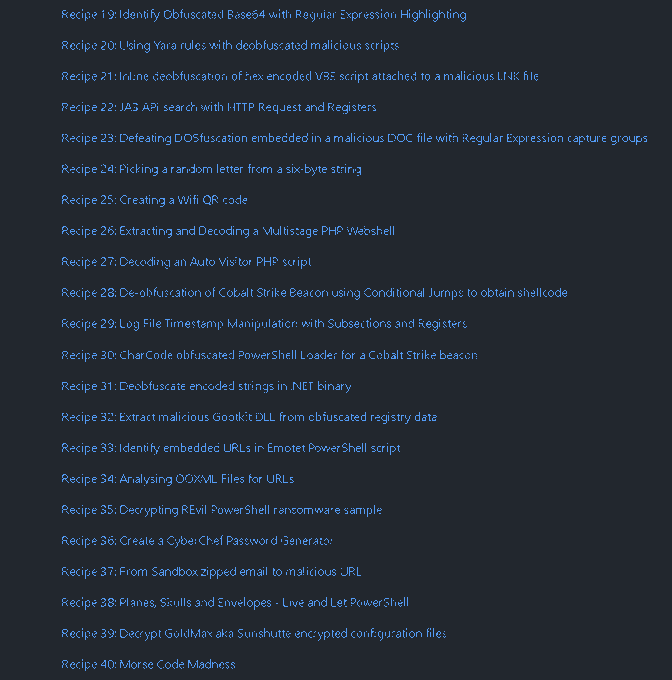
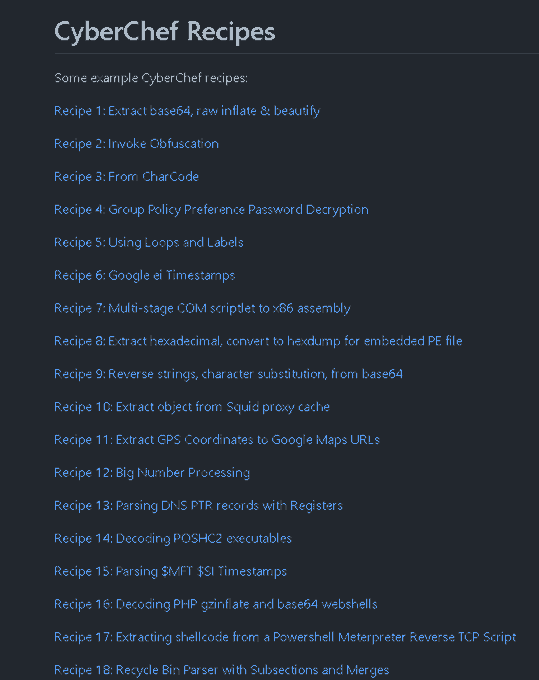
Just came across this excellent resource from
@mattnotmax
which is a curated list of
#Cyberchef
recipes! 👨🍳
#infosec
#cybersecurity
2
86
217
#100DaysOfYara
Day 9: There are so many public rules out there, it's easy to lose track 🤯
I got you covered! In YaraToolkit v0.2, I added a search engine for some rules repositories. Just enter a keyword to find a specific rule 🔍
For now, it supports three public repos, but…
8
78
217
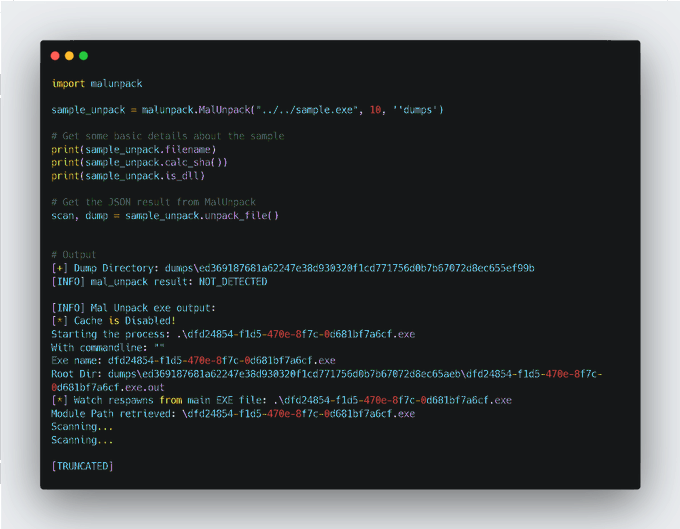
I coded a Python library wrapper for
#mal_unpack
your favorite malware unpacking tool, so you can import it easily in your scripts for unpacking automation! 🤓
#python
#malwareanalysis
#infosec
cc:
@hasherezade
👇👇👇
4
58
201
I started a curated list of IDA, x64dbg and OllyDbg plugin list! Feel free to PR your favorite one! :D
#reversing
3
100
198
📢Exciting news! We have recently revamped the
#UnprotectProject
anti-disassembling section with more detailed descriptions and code snippets. Check it out and let us know what you think! 🤓 cf:
@DarkCoderSc
#cybersecurity
#infosec
#malware
4
67
195
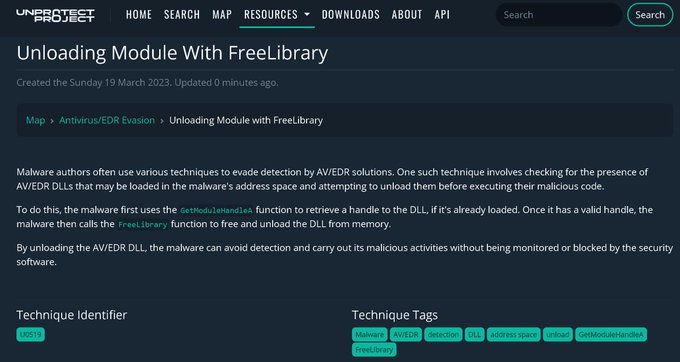
New EDR/AV evasion technique added to the
#UnprotectProject
by
@Praetorian_GRD
"Unloading Module Using FreeLibrary". Check out the detailed description, code snippet and CAPA rule👇
#cybersecurity
#malware
#infosec
cf:
@DarkCoderSc
4
59
191
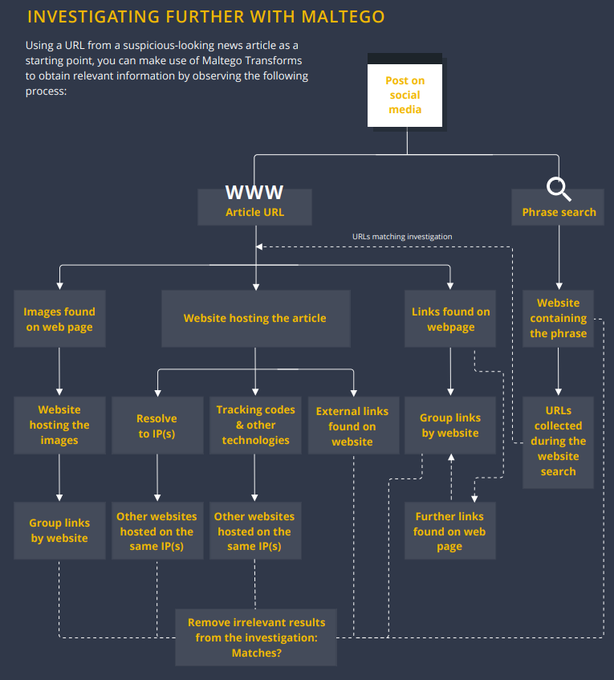
Maltego has released an article showcasing its features for tracking and countering disinformation and fake news articles. 👀
#infosec
#disinformation
1
55
190
Amazing Ida plug-in and service for recovering api or process names hashed by malware released by
@herrcore
🤩
#malwareanalysis
3
64
176
I often receive message from people that want to learn malware analysis and reverse engineering so I published my top books list. Check this out!
#cybersecurity
#MondayMotivation
#MalwareAnalysis
#ReverseEngineering
6
51
179
🧵 Since I published my book 'Visual Threat Intelligence', I've received a lot of feedback from the community about learning concepts through visuals.
🤩 I know that some
#Infosec
peers showcasing their visual expertise.
Stick with me for this thread; it'll be worth it! 🤓
3
47
179
📢I recently investigated a campaign targeting the cryptocurrency industry. I wrote a detailed report that includes TTP, IOC and more. Here is a thread about this attack! 🧵👇
@MsftSecIntel
@MicrosoftAU
#infosec
#cryptocurrency
#threatintelligence
#apt
6
75
167
📢 I updated the IDA, Ghidra, x64DBG & OllyDBG plugins and scripts repository to include the following
@OpenAI
GPT plugins! 👇
#infosec
#ReverseEngineering
#malware
#cybersecurity
2
49
166
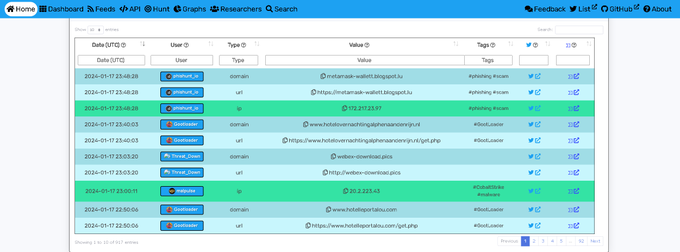
Pretty cool TweetFeed is back and you can also use it with
#OpenCTI
🤩
Amazing work by
@0xDanielLopez
🔥
6
42
166
Kaseya released yesterday two PowerShell scripts to detect vulnerable or compromised machines!
#REvil
#ransomware
1
97
163
Deobfuscation is an important part of malware analysis. In my "Reversing Tips" series, I just posted a little article on using FLOSS to quickly deobfuscate strings in a binary with IDA!
#malware
#reverseengineering
3
67
162
4⃣ - Anatomy of a YARA rule - Once you have gained more knowledge of threat intelligence concepts and methodologies, learning to use YARA rules can be very powerful for your threat hunting abilities!🛠️
#yararules
#threathunting
3
39
153
The
#Firmware
Security Training is now open source 🤘 -
@CHIPSEC
@c7zero
@ABazhaniuk
@JohnLoucaides
@a_furtak
1
99
151
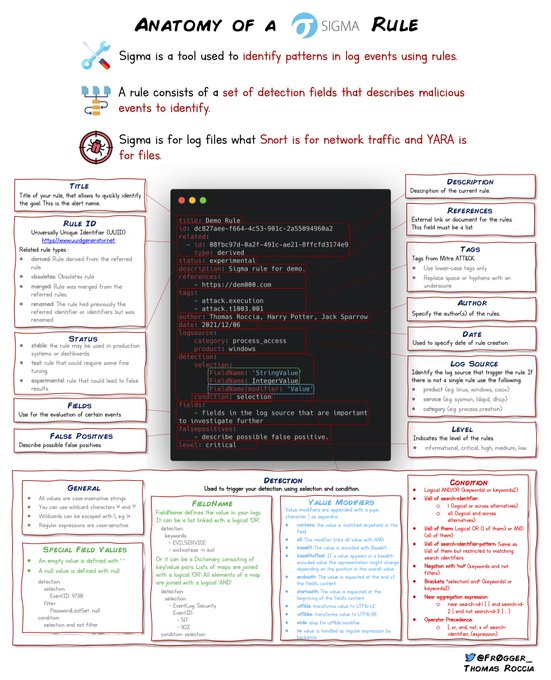
5⃣ - Anatomy of a SIGMA rule - Sigma is another great tool that will help you hunt your logs. While Yara is for file, Sigma is for logs. ⚒️
#sigmarule
#infosec
1
35
148
I wrote a blog about
#Malware
Strings for
#ThreatHunting
called "Fifty Shades of Malware Strings". You can find it here:
3
53
148
On
@VirusTotal
there is an interesting feature to look for malware similarities: "main_dhash_icon". I have coded a tool to generate the dhash of the icon of a sample.
#threatintel
#Malware
#infosec
cc:
@gerardofn
- thread 👇
2
60
151
Sometimes I do infographics that are easy to share to explain
#cybersecurity
concepts. I have posted some of them on this page. It will be updated with future release. 🤓
1
37
149
Just published a small blog to show how to setup kernel debugging on Windows 10
#reverseengineering
#kernel
1
51
148
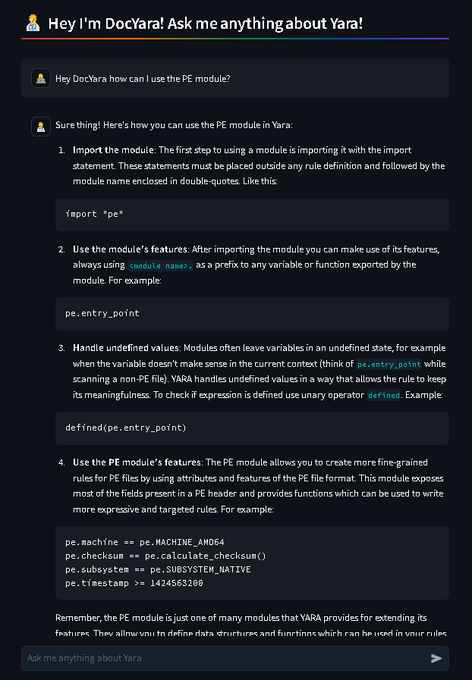
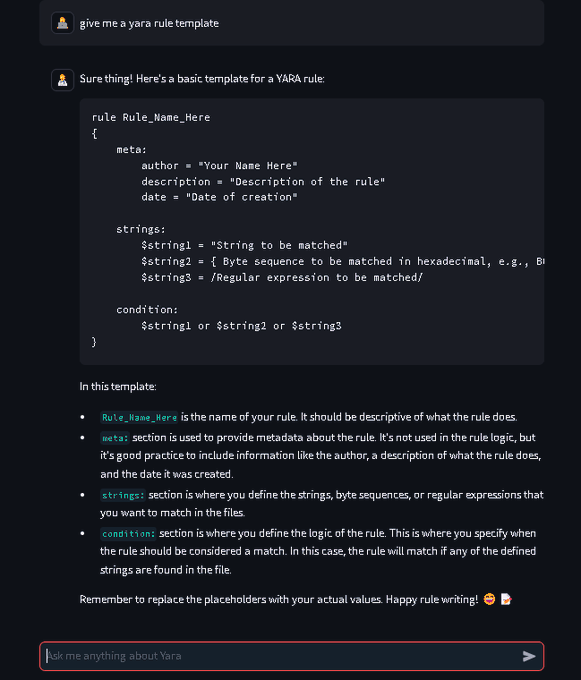
I stopped the
#100daysofYara
🙈 because I got swamped with other work & life but during my stint with the challenge, I released YaraToolkit and DocYara (which, let's just say, took me quite some time to create). 🤓
🛠️YaraToolkit is your all-in-one Yara go-to spot 🌟—from…
6
38
149
Looks like we have a new feature on
@virustotal
that shows the different malware collection!
#threatintel
#malware
#infosec
2
31
148
Over the past year, I've written several threads on
#malware
,
#threatintelligence
, and
#Python
. I saved them in my blog, here's one I recently posted on 10 Underrated Resources on Malware Techniques. You can read this thread in a blog format below! 👇
0
74
147
#100DaysOfYara
Day 11: Let me introduce you to Doctor Yara (DocYara👨⚕️), my latest contribution last night!
DocYara👨⚕️ is a specialized doctor in all things Yara! He can help you heal your rules and give vitamins to your strings! 💊
More seriously, DocYara👨⚕️ is a GPT model…
4
33
143
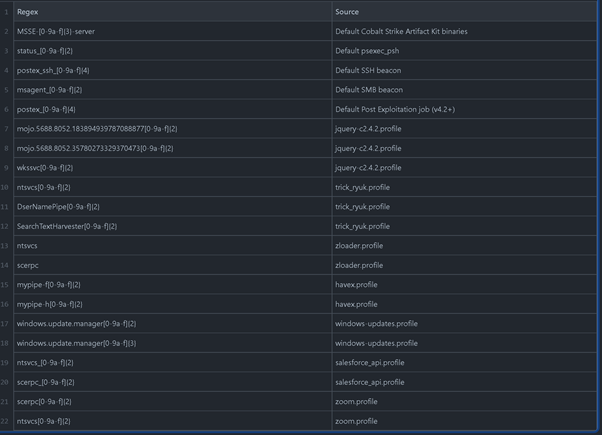
Cool overview of Named Pipes hunting for Cobalt Strike by
@svch0st
, including a list of regex for pipe names from default and custom profiles.
#threatintel
#CobaltStrike
#threathunting
0
62
143
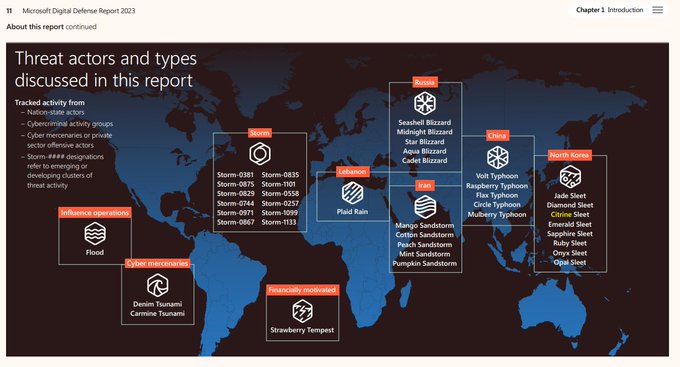
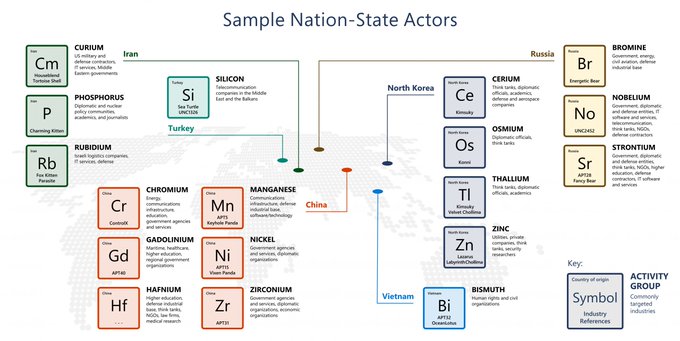
Microsoft identifies nation state activities by chemical element names. This example of nation state actors represents those that were most active in the last year. Our latest Digital Defense Report features more details about recent APT and more!
#ThreatIntelligence
#APT
4
49
136
Visualizing the Conti network with Python can be quite interesting to understand the connection between users! Here is a basic graph realized with Pyvis!🤓
#python
#Contileaks
#infosec
#visualization
4
28
136
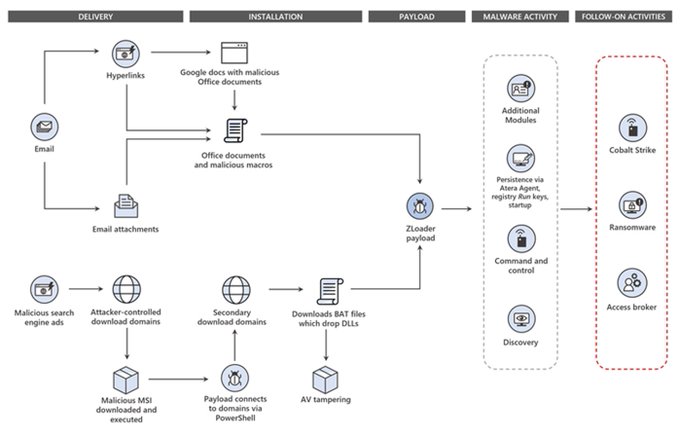
New blogpost detailing TTPs used by Zloader. It has been observed being delivered via malicious search engine ads and malicious emails. Check out the blog for more details and IOCs!
#infosecurity
#microsoft
#cybersecurity
#threatintelligence
0
53
131
Reading all the
#Contileaks
can be a bit time consuming, so I built a simple search engine in Python with Jupyter to search for a specific string occurrence and find only the information you are looking for! 🤓🤓
#MondayMood
#infosec
#ransomware
3
29
127
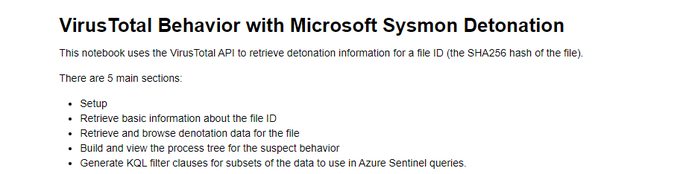
As part of the recent integration of Sysinternals tools into
@virustotal
, a Jupyter notebook is also available to request the Sysmon data that allows to retrieve and browse information summary and detonation for a given file hash.
#ThreatIntel
#malware
👉
1
58
125