topotam
@topotam77
Followers
4K
Following
6K
Media
19
Statuses
5K
All I know is that I know nothing. I like Windows, Active Directory and IoT/Hardware hacking. "Responsable mais pas coupable" de PetitPotam
Paris
Joined June 2015
RT @Oddvarmoe: Many people wanted my slides from the Windows Client Privilege Escalation webinar yesterday. Here are links to the slides a….
0
125
0
RT @eliran_nissan: I am excited to share with you my latest research - "DCOM Upload & Execute".An advanced lateral movement technique to up….
github.com
DCOM Lateral movement POC abusing the IMsiServer interface - uploads and executes a payload remotely - GitHub - deepinstinct/DCOMUploadExec: DCOM Lateral movement POC abusing the IMsiServer interf...
0
247
0
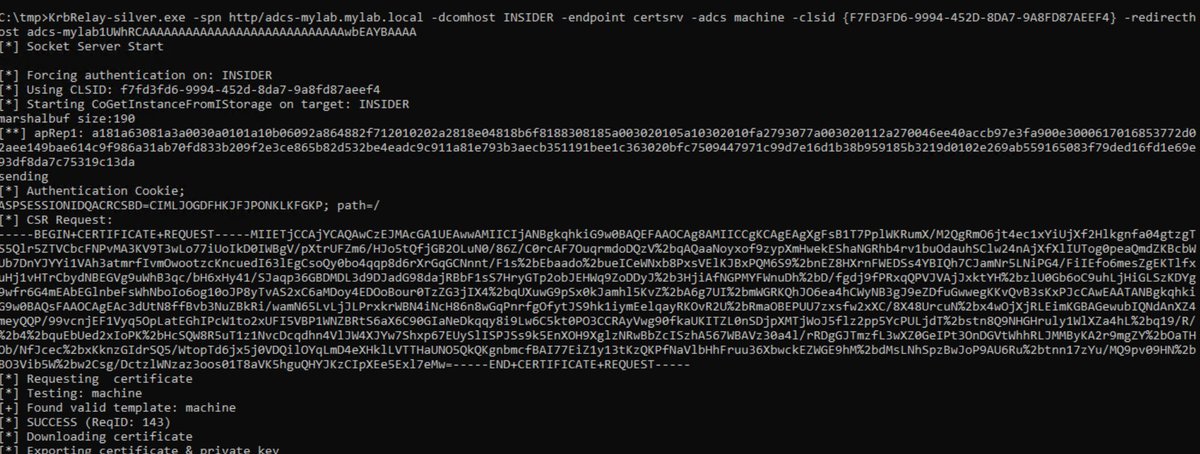
RT @Synacktiv: You can now relay any protocol to SMB over Kerberos with and the latest PRs from @hugow_vincent. Tha….
0
205
0
RT @mariuszbit: 🔥 Super excited to soon present my lifetime project publicly🤩. - 4yrs of R&D + 1y in commercial sale.- Weaponization of 95+….
0
135
0
RT @domchell: Here's a sneak peak of a new feature we have coming up in the next #Nighthawk release @peterwintrsmit….
0
12
0
RT @ksg93rd: #exploit.1. CVE-2024-46483:.Pre-Auth Heap Overflow in Xlight SFTP server. 2. CVE-2024-38812:.VMWare vC….
github.com
Pre-Authentication Heap Overflow in Xlight SFTP server <= 3.9.4.2 - kn32/cve-2024-46483
0
3
0
RT @SinSinology: 🔥💀After 40 hours of constant reversing of weird looking c++ and no sleep, I Finally cooked the .CVE-2024-47575 fortimanage….
0
180
0
RT @pentest_swissky: Inside Xerox WorkCentre: Two Unauthenticated RCEs @_mohemiv .
swarm.ptsecurity.com
Every organization has printers. In this writeup, I will cover two unauthenticated RCE vulnerabilities that I discovered in Xerox WorkCentre.
0
27
0
RT @hacknspeak: 🇫🇷🎙️Nouvel épisode du podcast Hack'n Speak avec @_p0ly_ & @vdehors triple vainqueurs de la Pwn2Own 🏆🏆🏆. Au programme, un re….
creators.spotify.com
Twitter : https://x.com/_p0ly_ Twitter: https://x.com/vdehors Twitter: https://x.com/mpgn_x64
0
18
0
RT @Synacktiv: We just rewrote the AsOutsider part of #AADInternals in Python to enhance compatibility and ease of use in Linux environment….
github.com
Python3 rewrite of AsOutsider features of AADInternals - synacktiv/AADOutsider-py
0
41
0
RT @kha1ifuzz: Excited to share that the @malcrove Red Team just dropped new blog and new tool SeamlessPass!.utilizing Microsoft’s Seamless….
0
54
0
RT @_wald0: Nine new functions in BARK:. Get-AllEntraRoles.Enable-EntraRole.Get-EntraDeviceRegisteredUsers.Get-IntuneManagedDevices.Get-Int….
0
86
0
RT @0gtweet: Fancy DLL sideloading? Add built-in licensingdiag.exe to your toolbox. It will load everything listed under Windows NT\Current….
0
166
0
RT @netbiosX: If you’ve found value in and would like to support, we would greatly appreciate any donation you can….
pentestlab.blog
Offensive Techniques & Methodologies
0
5
0
RT @rvrsh3ll: It's crunch time with class for @bsideskrakow with @BHinfoSecurity . Come join us for #OOAFA Offensive Operations Against Fo….
0
6
0
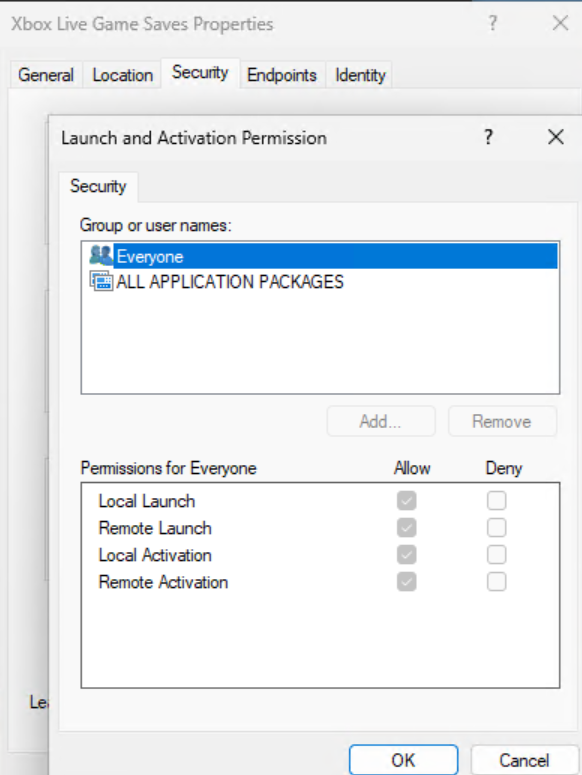
RT @decoder_it: #FakePotato (CVE-2024-38100) post is out! Check out the short write-up on this unexpected vulnerability 😅 .
decoder.cloud
While exploring the DCOM objects for the “SilverPotato” abuse, I stumbled upon the “ShellWindows” DCOM application. This, along with “ShellBrowserWindows”, is we…
0
107
0