Th4m1
@justcacheme
Followers
904
Following
3
Media
30
Statuses
466
Explore trending content on Musk Viewer
Arda
• 481218 Tweets
Portugal
• 314943 Tweets
Ronaldo
• 294873 Tweets
Zelda
• 257123 Tweets
Georgia
• 227397 Tweets
Noam Chomsky
• 100428 Tweets
Justin Timberlake
• 71151 Tweets
Juneteenth
• 63669 Tweets
Czech
• 62191 Tweets
ロマサガ2
• 52302 Tweets
#secretstory
• 50476 Tweets
Nvidia
• 47599 Tweets
Joey
• 45128 Tweets
رونالدو
• 44831 Tweets
البرتغال
• 43408 Tweets
Torres
• 42270 Tweets
Nubank
• 41119 Tweets
Leao
• 38026 Tweets
#SVFinal
• 32584 Tweets
Vitinha
• 27493 Tweets
THE LAKES
• 27058 Tweets
Francisco Conceição
• 24230 Tweets
Bernardo Silva
• 23377 Tweets
Ted Cruz
• 22270 Tweets
Jota
• 20534 Tweets
Marieta
• 16585 Tweets
Bruno Fernandes
• 16451 Tweets
República Checa
• 16232 Tweets
Alperovich
• 15575 Tweets
Cancelo
• 13511 Tweets
ポルトガル
• 12432 Tweets
Maxence
• 10180 Tweets
Last Seen Profiles
Pinned Tweet
My methodology: (after re-watching naffy & m.litchefield's interviews so many times)
1. Click every button
2. Go to History and look for interesting request
3. Send it to the playground (REPEATER) [Golden Tool]
4. Fuck up the request, give it your all!!!
#bugbountytips
2
13
56
As soon as its triaged I am doing my first writeup, bookmark this.
#bugbountytips
#BugBounty
11
9
162
Another one, a very interesting SSRF allowed me to port scan internal host.
#bugbounty
#bugbountytip
4
3
114
I started Bug Bounty in 2019, had no luck until late last when I started realizing I wasn't taking hacking seriously.
Now I know, the more you show up, start Burp / ZAP and hunt... you will def WIN if you put in the work!!!
#bugbountytip
#bugbounty
6
5
107
Found a token leak via an IDOR but I cannot find its purpose (endpoint: /checkPaymentStatus), anyone who is willing to collab?
#BugBounty
#bugbountytips
18
7
75
Dropped out of Varsity to do this shit full time. Its a risk I am willing to take and I know it requires HARD WORK!
#bugbounty
#bugbountytip
2
3
60
#bugbounty
Just found an account takeover using this Information. Just add this smart man to your follower's list. Thank you
@Jayesh25_
for insightful knowledge🫡
5
5
50
just got kicked out of at home because this "bug bounty" thing of money doesn't work🥲. its sad to have unsupportive parents😭
#BugBounty
5
2
30
If there's one man that changed my life, It would be
@NahamSec
.
I appreciate you so much man. Things you have done for this community will never be forgotten 🙏🏾
1
0
26
if I find a time-based SQLi but cannot exploit it on SQLMap, does that make it "Not-Applicable"?
#BugBounty
13
0
27
gents u not doing anything if you don't have so many tabs open! 🤞🏾
#BugBounty
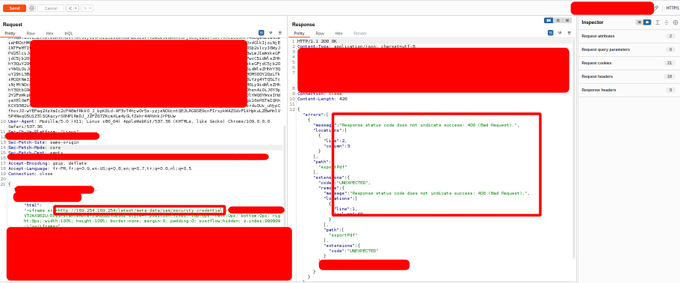
Successfully bypassed a SSRF WAF by using a combination of IPV6 + Unicode. Payload for Metadata instances:
http://[::ⓕⓕⓕⓕ:①⑥⑨。②⑤④。⑯⑨。②⑤④]:80
Check images for response difference between 169.254.169.254 and the above payload I shared 🔥
#bugbounty
#infosec
#waf
56
524
2K
0
1
17
who hunts successfully without a proxy tool?
I am asking for myself, i think I am less productive with them🥲
#bugbounty
#bugbountytip
1
0
12
the more you hack, the more you refine your hacking process and eventually discover your own hacking methodology.
#bugbountytips
#bugbounty
1
0
11
@bug4you
Spotted a ?url= parameter the tried my burp collab link
Tested again with local IP and fuzzed the ports for the IP then you check response length and the response itself
Sometimes this can land you on an internal admin portal
2
0
11
After years of confusion and wasting time. I am really starting to enjoy testing apps.
Tip: Open Burp and try to manipulate an application EVERY FU*KN DAY!!!
#bugbountytips
#bugbounty
2
3
10
The way I see it, everyone has their own kind of style of hacking, that's why you always have to approach an application as if its new.
With the same request I just looked at and found an IDOR you might find a bug I never thought of.
#bugbountytip
#bugbounty
1
0
10
I hack better with Burp Intercept feature and Repeater. I usually do look at History unless there's a specific request I am looking for.
I just like to rip off the application in real time.
#BugBounty
#bugbountytip
0
0
8
This is one of the reasons why I'll forever support Burpsuite, is the best.
#BugBounty
Thank you for all the free resources
@WebSecAcademy
I am always grateful to all the platforms/people for giving knowledge for FREE. That's why I also share what I learn for Free it's like I give back what I have taken from the Internet.
2
5
48
0
0
6
big tip:
@th4m1_hacker
@a4hamkhan
I started finding bugs when i stopped focusing on recon , and focus instead on app functions
1
1
5
0
1
6
Read every post / writeup/ video with appreciation. You will learn 📙 effectively when you appreciate every bit of information 🧠 that's been provided to you. Let's appreciate those who share their experiences to teach us as a community ♥
#bugbountytip
#bugbounty
0
0
5
@Bugcrowd
This time I won't give up. With the effort I am putting, I will make it in Bug Bounty🤞🏾
0
0
4
Here I used Forced Browsing to bypass JavaScript Authentication. A Simple bug got me a $100 bounty. Thank you
@Bugcrowd
for the great platform🫡
0
1
4
🏝 First Day being a Bug Bounty Hunter🧩, I’m ready, let’s 👨🏾💻HACK together DM me
#bugbountytips
#BugBounty
1
1
4
Hmmm never thought about this🤔
@AlanBailward
@Jhaddix
Nmap hard forces a close on its stealth / half scan, and performs faster than Naabu does in that regard, at least in my tests.
But it’s moot. I don’t want to use raw sockets and require root privs just to do a scan. Naabu seems faster when doing the full CONNECT.
So when
0
0
3
0
0
3
Secret To Win in
#BugBounty
0
0
3
@R007_BR34K3R
@Bugcrowd
Great idea bro, We need to add report examples now for each Vuln type.
0
0
3
@Neo__Hq
@Cobratate
YOU TAUGHT ME A LOT BROTHERS, I AM AWAKE BECAUSE OF YOU. NOW I SEE WHAT IS HAPPENING IN THIS CRAZY WORLD. THANK YOU🙏🏿🙏🏿🙏🏿
0
0
2
@haryanaala302
😂 I get them too my friend, I really suggest looking for bugs that most people are scared to look for.
1
0
2
@GokTest
FFUF is fast but requires carefully curated wordlists, with dirsearch you find juicy endpoints with its default worldist.
ffuf is great but I love dirsearch.
0
0
1
its down on my side too😥
1
0
1
@zseano
Thank you so much for this Sean 🙏🏾. I think I'm going to leave weed for a moment.
It's been 2 days sober and I feel energetic. Even went for a long run today.
1
0
1
@3nc0d3dGuY
this is good bro, hackers often forget to fuzz backwards (especially us new hackers). Congrats on this dope brother!
0
1
1
@GokTest
thank you bro you really helped me, I was addicted to these proxy tools and was lacking productivity these past weeks. Thank again mate!, I am already fuzzing as we speak😁
0
0
1