Renzon
@r3nzsec
Followers
4K
Following
5K
Media
300
Statuses
3K
IR/Forensics @Unit42_Intel | Co-Founder @guidemtraining | Contributor/Analyst @TheDFIRReport @XintraOrg | CTF member @_hackstreetboys
Joined July 2018
I recently co-authored a @Unit42_Intel blog about a unique IR case in which a threat actor’s custom EDR bypass (using #BYOVD) exposed their toolkit, methods, and even identity. Check out how we unmasked them through an opsec slip-up! #dfir .
unit42.paloaltonetworks.com
A threat actor attempted to use an AV/EDR bypass tool in an extortion attempt. Instead, the tool provided Unit 42 insight into the threat actor.
6
64
222
RT @EncapsulateJ: There's pretty much never been a better time to start learning or get hands on blue team experience through labs. The ava….
0
4
0
RT @orange_8361: Turns out my #PHRACK article is live! 🔥. > The Art of PHP — My CTF Journey and Untold Stories!. Kinda a love letter to tho….
0
208
0
Super fun working on this lab with the @XintraOrg gang!! Enjoy and let us know your feedback! . #ScatteredSpider #MuddledLibra #UNC3944.
NEW LAB: Scattered Spider (UNC3944) 🕷️🕸️. Scattered Spider hits indie studio AB Projekt Blue, deploying ransomware and stealing unreleased game code. Test your skills on:. 👀 Social Engineering & MFA Fatigue.👀 Credential Theft via OST Files.👀 Bring Your Own Vulnerable Driver
2
4
41
RT @Seifreed: 🎉 Excited to release #r2inspect - my malware analysis framework using @radareorg . 🔍 Analyze PE files with 28+ modules. 🛡️ De….
github.com
Advanced Malware Analysis Tool using Radare2 and r2pipe - seifreed/r2inspect
0
72
0
SEO > #Bumblebee > AdaptixC2 > Akira RW.
🚨 Search for software, end up getting ransomware!. SEO-driven #Bumblebee malware campaigns observed throughout July led to domain compromise, data theft & #Akira ransomware. Tools included #AdaptixC2 & #Netscan.
0
0
7
RT @Unit42_Intel: A telecom-focused group active most of last year employed custom tools and DNS tunneling for stealth and also routed traf….
0
22
0
Fun times! 6hrs of CTF against some of the best DFIR professionals in North America. Thanks for this incredible event @sansforensics @SANSInstitute . #dfir
4
5
101
RT @mathias_fuchs: Attackers love RDP for sneaky lateral moves—but every pixel leaves a clue! 🕵️♂️ Check out my latest blog on tracking at….
medium.com
Introduction
0
87
0
Fantastic project that can be used to visualize your SOD!! Great stuff @Arimb00R! 🔥.
🚀 **Kanvas** - my new open-source project !!. If you're in IR, Forensics, or part of a SOC dealing with security incidents/ breaches, , Give it a spin and let me know what you think 🤞. Quick writeup 📌 Github Repo 📌
1
1
13
RT @inversecos: Become a contributor at XINTRA @XintraOrg 🔎. We're looking for RED and BLUE team contributors . 🔴Red Team – Emulate real AP….
0
20
0
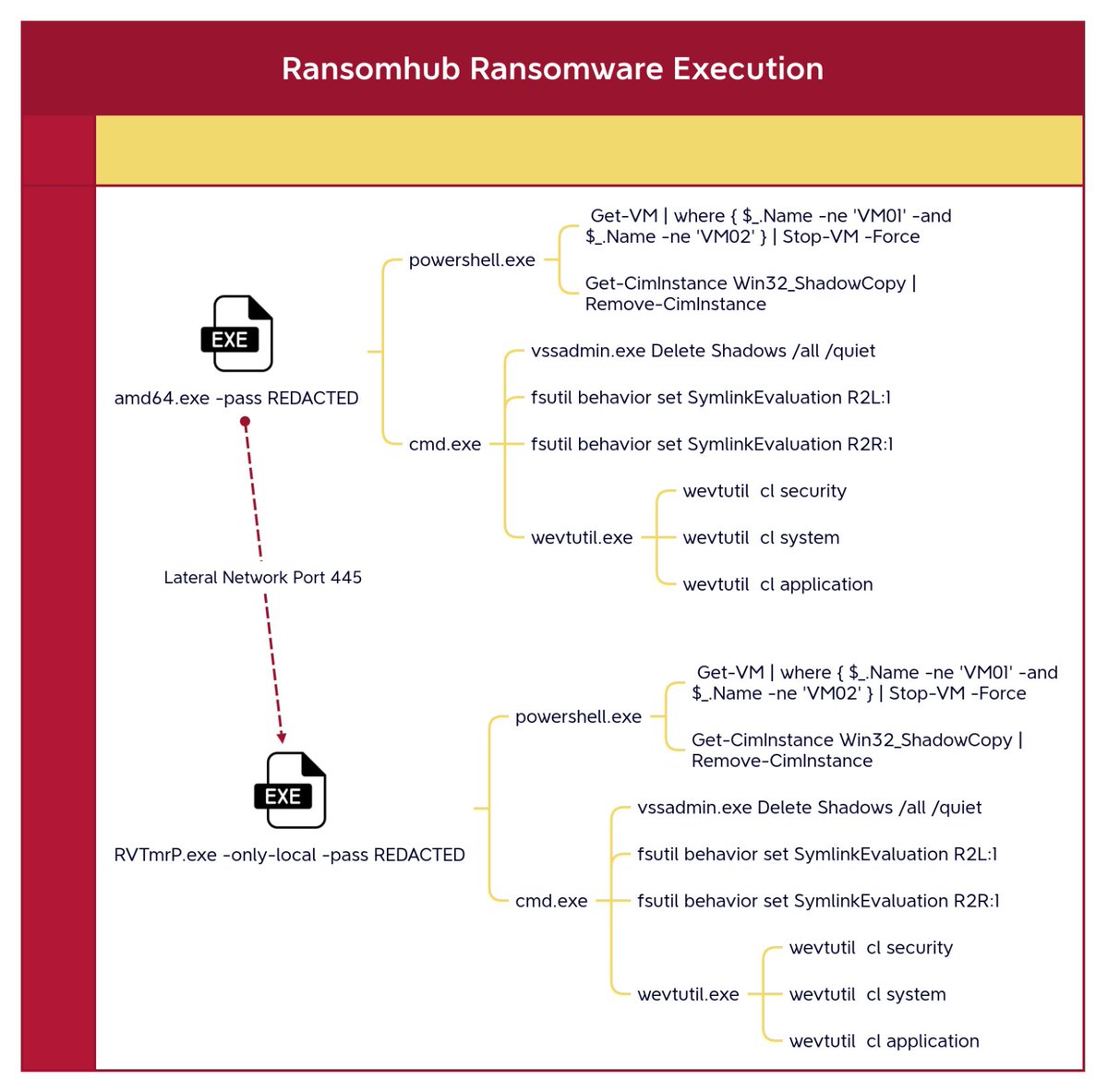
Classic #ransomhub execution baked into the encryptor itself. Check out the latest report here and learn how that exposed RDP on your network can trigger a massive ransomware attack. #dfir . @TheDFIRReport
0
10
56