Virus Bulletin
@virusbtn
Followers
60K
Following
1K
Media
10K
Statuses
28K
Security information portal, testing and certification body. Organisers of the annual Virus Bulletin conference. @[email protected]
Oxfordshire, UK
Joined February 2010
We are thrilled to officially announce that VB2026 will take place in the vibrant city of Seville, Spain, from 30 September to 2 October 2026. 🇪🇸 More details coming soon on the venue, call for papers, sponsorship opportunities, and how to join us. Can't wait to see you there!
2
8
37
Zimperium zLabs identified a new ClayRat Android spyware variant. The latest version abuses Android’s accessibility services for keylogging and lockscreen bypass, screen recording, fake notifications and scripted button taps to block shutdown or removal. https://t.co/znP29gUFAT
0
8
18
Did someone order a change of scenery? You could be here by Friday.
0
2
9
Intel 471 reports new Android banking trojan FvncBot, targeting Polish users via a fake mBank security app. It abuses accessibility services for keylogging, employs web injects, screen streaming & HVNC, & has a new codebase not tied to leaked source codes. https://t.co/WbYHbzrdpq
0
11
34
We’ve joined @CISACyber & @cybercentre_ca to attribute the broad campaign using BRICKSTORM to China state-sponsored cyber actors. Review the report for guidance on how to detect BRICKSTORM backdoor activity and improve your cybersecurity posture against this targeting. 🔗
21
133
373
🔴 LIVE from inside #Lazarus APT's IT workers scheme. For weeks, @BirminghamCyber & @north_scan kept #hackers believing they controlled a US dev's laptop. In reality, it was our sandbox recording everything. See full story and videos ⬇️ https://t.co/gRb7GKIERQ
13
126
474
New Securonix Threat Research Advisory: JS#SMUGGLER. Our team identified a sophisticated multi-stage malware campaign that begins with an obfuscated JavaScript loader and ends with the silent installation of NetSupport RAT. 🔗 https://t.co/FseBpMOcMp
0
1
2
CrowdStrike has identified WARP PANDA, a China-nexus actor targeting vCenter and cloud environments with custom implants and long-term covert access. 🔗 Full analysis and recommendations: https://t.co/g06XzPlbS6
3
52
153
FortiGuard Labs observed UDPGangster, a UDP-based backdoor linked to MuddyWater. Recent campaigns use macro-enabled Word lures to target organisations in Turkey, Israel & Azerbaijan, with UDP for command execution, file exfiltration & payload delivery. https://t.co/Q7H8LKylLg
0
6
22
Splunk Threat Research Team analyses CastleRAT, a RAT first seen in March 2025 with Python and compiled C builds. It uses RC4 with a hard-coded key for C2, gathers host details, & can download further payloads and open a remote shell for attacker commands. https://t.co/xQuYSZesHb
0
10
53
Thinking of integrating AI into your operational technology environment? We’ve joined @CISACyber and others to publish guidance to help you safely and securely manage the associated risks and protect your environments. https://t.co/H0hu5vhUfn
23
113
350
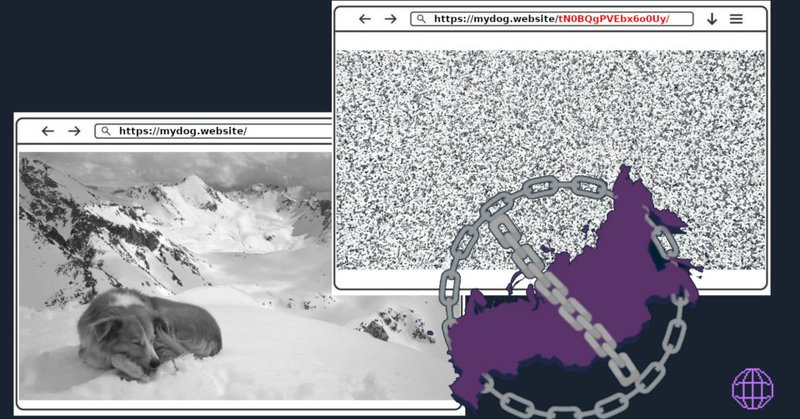
In 2025, Tor faced some of the toughest censorship yet. Thanks to real-time monitoring, community feedback that helped us improve and deploy new tools, Tor kept people connected when it mattered most. Want to help? You can support our mission by running a Snowflake proxy or
blog.torproject.org
In 2025, Tor faced some of the toughest censorship yet. From Iran’s wartime internet blackouts to Russia’s rapidly evolving blocking tactics. Tor’s anti-censorship team sprung into action and...
16
164
783
🚨 CRITICAL RCE ALERT: React & Next.js Vulnerability ↓ Critical remote code execution (RCE) vulnerabilities have been published affecting the React 19 ecosystem and Next.js. These vulnerabilities (CVE-2025-55182 & CVE-2025-66478) reside in the React Server Components (RSC)
3
71
262
"Defense is doable… We have to be brilliant at the basics... It’s about doing really good access management, really good principle of least privilege, really good network architecture..." -- Matt Duncan, E-ISAC VP of Security Operations and Intelligence
thecyberwire.com
In this episode of the Microsoft Threat Intelligence Podcast, host Sherrod DeGrippo is joined by Matt Duncan, Vice President of Security Operations and Intelligence at the North American...
0
4
20
🔴 🐭 𝗢𝗰𝘁𝗼𝗥𝗔𝗧: 𝗡𝗲𝘄𝗹𝘆 𝗦𝗼𝗹𝗱 𝗥𝗔𝗧 𝗦𝗵𝗼𝘄𝘀 𝗨𝗽 𝗶𝗻 𝗮 𝗠𝘂𝗹𝘁𝗶 𝗦𝘁𝗮𝗴𝗲 𝗔𝘁𝘁𝗮𝗰𝗸 𝗖𝗵𝗮𝗶𝗻 A malicious VSCode extension kicked off a multi-stage chain that delivered Anivia and OctoRAT. OctoRAT is a brand new RAT now circulating in underground
1
50
177
Browser-update-themed lures are fueling a surge in #ClickFix activity. We've seen 10K-plus hits on sites that lead to ClickFix pages pushing a variety of malware types through #pastejacking. Details at https://t.co/jLHXBHpx60
0
36
110
CRIL has uncovered an active V3G4 campaign using a Mirai-derived botnet alongside a fileless, runtime-configured cryptominer. https://t.co/G4yKt2uTW1
#V3G4 #Botnet #Cryptominer #ThreatIntelligence
0
4
2
SEQRITE APT-Team details a spear-phishing campaign against Russian HR, payroll and internal admin departments using bonus and policy-themed decoys. The chain relies on malicious LNK files, a new DUPERUNNER implant, and an AdaptixC2 Beacon for C2. https://t.co/HtwkP6uwuy
0
11
51
Amnesty Security Lab’s Intellexa Leaks investigation details the internal operations of the spyware vendor behind Predator. Leaked documents & materials show how its tools enable targeted surveillance of journalists, human rights defenders & civil society. https://t.co/6qEFGOK9A0
0
11
30
Trend Micro Research details a ValleyRAT campaign targeting job seekers via email, hiding behind a weaponized Foxit PDF Reader and using DLL side-loading for initial access. As a RAT, ValleyRAT enables remote control, monitoring and data theft. https://t.co/c12jyCzz55
1
24
91
On 10 December, a webinar hosted by the Cyber Threat Alliance will explore how adversaries & defenders are using AI, the challenges of securing AI systems, and what these trends mean for protecting our networks and critical infrastructure.
us06web.zoom.us
Zoom is the leader in modern enterprise video communications, with an easy, reliable cloud platform for video and audio conferencing, chat, and webinars across mobile, desktop, and room systems. Zoom...
0
2
8
🚩 7-Zip RCE Vulnerability Exploited in the Wild https://t.co/xww051lZKn Security researchers are warning that a remote-code-execution flaw (CVE-2025-11001) in 7-Zip is now being actively exploited. The bug stems from incorrect processing of symbolic links inside ZIP
cybersecuritynews.com
Hackers have begun actively exploiting a critical remote code execution (RCE) vulnerability in the popular file archiver 7-Zip, putting millions of users at risk of malware infection and system...
5
88
265