Malcat
@malcat4ever
Followers
2K
Following
199
Media
37
Statuses
237
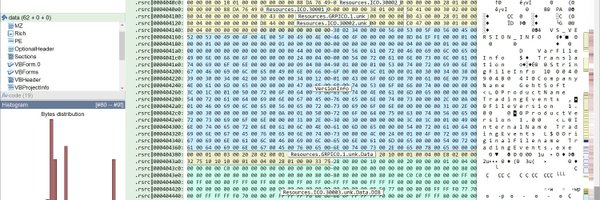
https://t.co/jeuFqKrpaH, a hexadecimal editor / disassembler / decompiler for #malware analysis, #DFIR and #SOC.
Lyon, France
Joined February 2021
First steps with #malcat? Here is a tutorial video, courtesy of @InvokeReversing : https://t.co/PZY6Ecbpmz
0
11
34
#Malcat tip: The strings view shows dynamic and stack strings. Clicking on the base64 string, I can see it isn't a straight string. Right-click -> transform, to base64 decode Highlight the URL, right-click > "Download and Analyze". Keep working without leaving the app.
Possible interesting, "Sahlmén Software AB" (SSL Corp given cert) signed "invoiceNov2025_DocumentReader.com" sample, seen from Ukraine: 200769e30e583f97dd8163427cbdcffe3d4ed040e566455996c6c231426f5b5a 🤷♂️
2
11
49
My humble contribution to the Malware Analysis Community. Hope it helps ! Thanks @malcat4ever From WinWord to PureLogsStealer with @malcat4ever
#malcat #malware #purelogsstealer
https://t.co/7A0t8Vuk2G
prfalken.org
I recently had a suspiciously large attachment to analyze. After a few minutes, I discovered that the reason it was that big was because it was embedding a complete Python 3.10 environment. The...
2
15
69
#Kesakode updated to1.0.45 ! ● New malware entries: Fullmetal, Laplas, RoningLoader, ShadowRat, Silentsweeper and SystemShock ● Updated malware entries: 29 ● FP-fixed signatures: 931 ● 16587 new clean programs whitelisted ● 3452882 new functions ● 165257 new strings
0
4
19
#kesakode DB update to 1.0.43, with again a focus on the clean set: ● 18 new malware entries ● 53 existing entries updated ● FP-fixed signatures: 749 ● 5280 new clean programs whitelisted ● +2M unique functions ● +300K unique strings
0
0
11
Hello! I just dropped a new article about an old but very up-to-date subject. Please let me know if you find anything incorrect or not well-explained. https://t.co/Abno7ODe1u
#malwareanalysis #reverseengineering #malcat #x64dbg #pebwalk #shellcode
moval0x1.github.io
Practical Techniques for Shellcode & Reversing
2
20
64
The ReversingLabs research team analyse an evolving Discord-based RAT family operated by a threat actor group who call themselves "STD Group". https://t.co/3pU85VonWS
0
8
25
Downloading CertCentral's DB or using it in automation is useful as I don't have a lot of time to tweet about revoked certs. 🥲 In 2025, we're seeing an average of 67/mo. Relatedly, if you want to get involved, feel free to reach out or join the discord: discord[.]gg/dvGXKaY5qr
Someone pointed out that it wasn't obvious how to download the whole Cert Central database; so, I've added some buttons. The database can also be downloaded from the same url without authentication: certcentral[.]org/api/download_csv
0
4
16
#kesakode updated to 1.0.42: * New entries: Brickstorm, Butoflex, Ladvix, NetStar, Pantegana, Tendyron, Tsunamikit and VampireBot * Updated entries: AuraStealer, Latrodectus, NightshadeC2 and QNAPCrypt * 33275 new clean programs whitelisted * FP-fixed signatures: 1028
0
1
6
Please note that https://t.co/VXslVb3y4S is NOT the official homepage of #pestudio The official homepage of pestudio is
2
7
29
Discover a new linux backdoor hidden for 10 YEARS in a critical HTTP server, waiting for a "magic packet" to wake up. Undocumented TTP. Full report: https://t.co/omP65ga7e9
#Malware #ThreatHunting #Cybersecurity @ExaTrack @LoginSecurite
1
12
20
Updated #Kesakode to 1.0.41: * New malware families: 14 * Updated malware entries: 16 * FP-fixed signatures: 1340 * 33 new malicious samples * 52010 new clean programs whitelisted * 13093705 new unique functions * 7778950 new unique strings
0
5
16
If you’re into malware analysis, you should really give Malcat a try. It’s an all-in-one tool with hex and structure views, disasm and decomp, integrated Yara, python scripting and similarities scanning... A very handy and well-designed time saver!
1
23
133
Malcat version 0.9.11 has been released, with support for ARM and Mach-O program analysis. More details below: https://t.co/kvL8eS5MVk
malcat.fr
Malcat version 0.9.11 is out! With this release, Malcat is now able to analyse MacOS programs. That means: addition of Armv7, Armv8 and Aarch64 disassemblers and decompilers as well as MachO, DMG and...
1
6
29
thanks to #flareon12 5th binary, #Malcat will better handle big-ass switch constructs in the future!
3
1
39
#Malcat tip #10: analysing backdoored clean software can be hard. A quick win is to pivot around known constants, thanks to Malcat's 400k+ constants DB (here a #Tropidoor dlder):
0
8
25
Updated #Kesakode to 1.0.39: * New malware entries: HybridPetya, MostereRAT, PhantomStealer, SatanLockV2 and Yurei * Updated malware entries: 38 * FP-fixed signatures: 381 * 3285 new library objects seen * 2622 new clean programs whitelisted * 905652 new unique
1
3
11