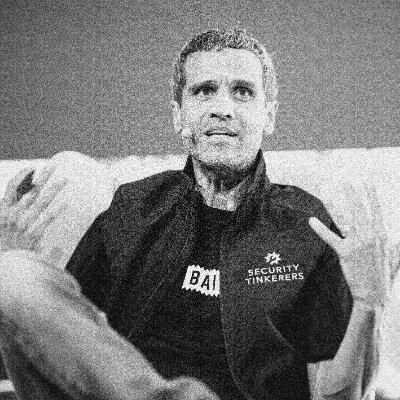
Ryan Naraine
@ryanaraine
Followers
27,739
Following
878
Media
1,577
Statuses
29,789
I write about hackers and the business of cybersecurity. Podcast + newsletter: . Columns: @securityweek . Conference: @labscon_io
Joined August 2007
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
Usyk
• 429326 Tweets
WALK IN SKECHERS WITH APO
• 221824 Tweets
Joshua
• 138580 Tweets
オークス
• 99177 Tweets
#RingOfFire
• 67981 Tweets
#precure
• 66249 Tweets
プリキュア
• 50271 Tweets
#ブンブンジャー
• 40702 Tweets
#nitiasa
• 36072 Tweets
しんちゃん
• 23789 Tweets
ゴーオンジャー
• 22713 Tweets
#仮面ライダーガッチャード
• 22152 Tweets
切り取り
• 15462 Tweets
しんのすけ
• 14988 Tweets
Hardy
• 11717 Tweets
コラボ回
• 10381 Tweets
Last Seen Profiles
Azure Backdoors: How to Hide Them, How to Find Them
Conclusion: "There has never been a better time than right now to get involved in Azure abuse research."
Watch the
@_wald0
talk:
Slides:
1
115
405
So, some personal news: I've joined
@window
's team at Intel to work on security community engagement. Get in touch and let's talk (DMs open)
44
26
367
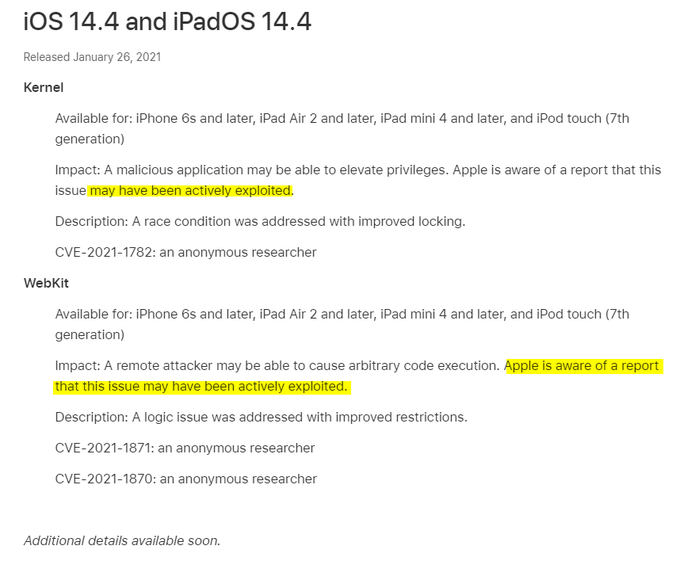
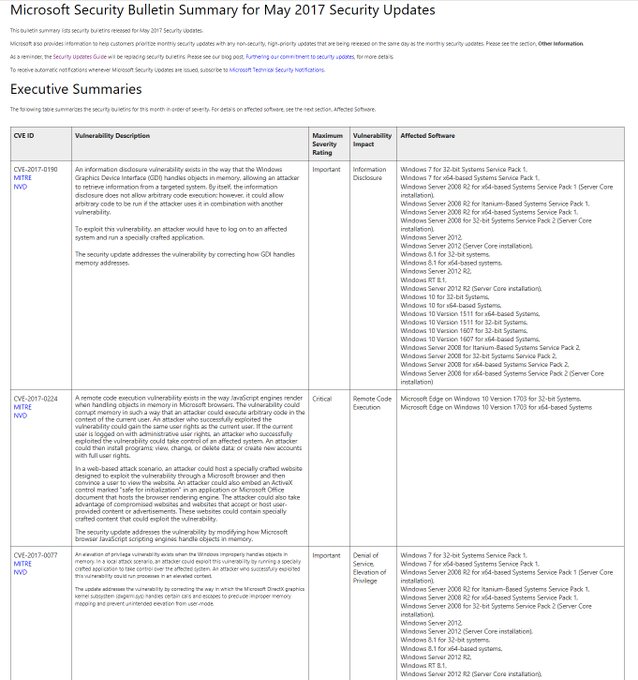
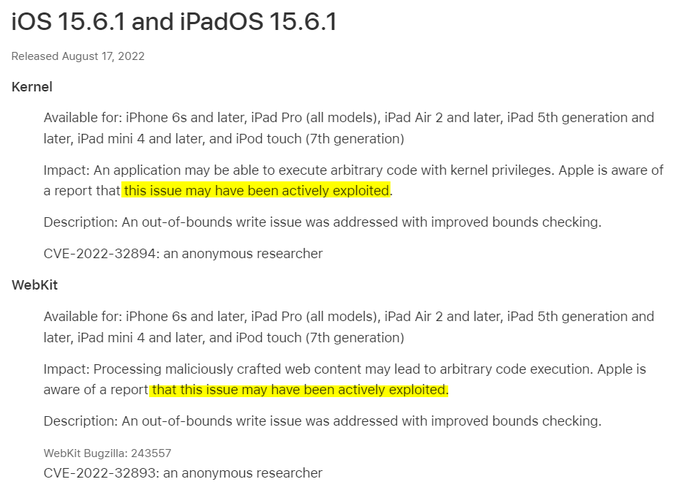
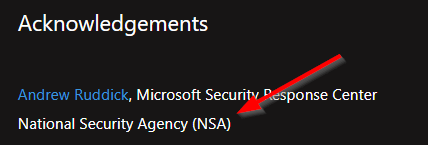
Microsoft Patch Tuesday is a doozy this month:
- 114 documented CVEs
- 4 critical MS Exchange Server vulns
- 2 pre-auth code execution vulns found by NSA
- 1 in-the-wild 0day found by Kaspersky ninja
@oct0xor
- 0 Pwn2Own bugs fixed
2
182
351
Okta is blaming the recent hack of its support system on an employee who logged into a personal Google account on a company-managed laptop.
16
79
301
Orange Tsai (
@orange_8361
) at Black Hat:
"Fun fact - even you found a super critical bug like ProxyLogon, Microsoft will not reward you any bounty because Exchange Server On-Prem is out of scope."
12
62
268
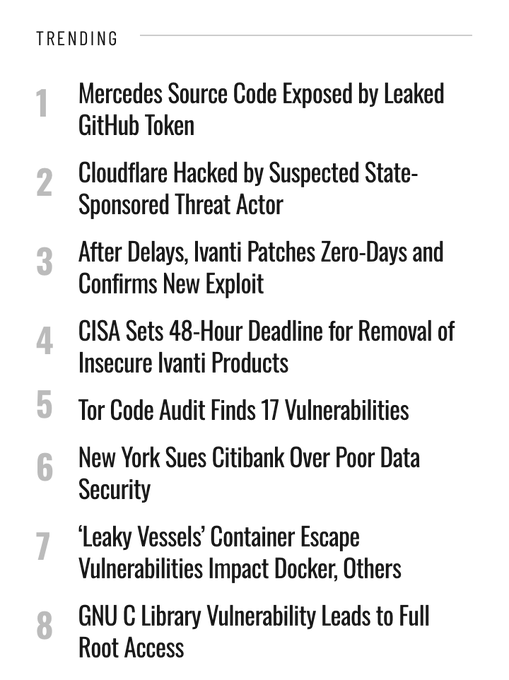
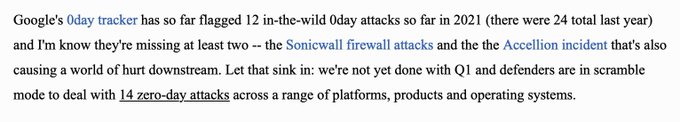
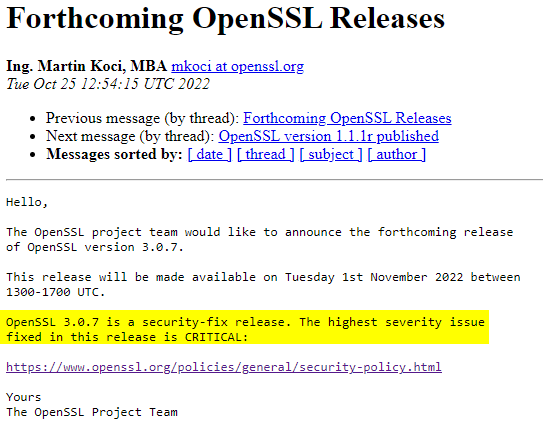
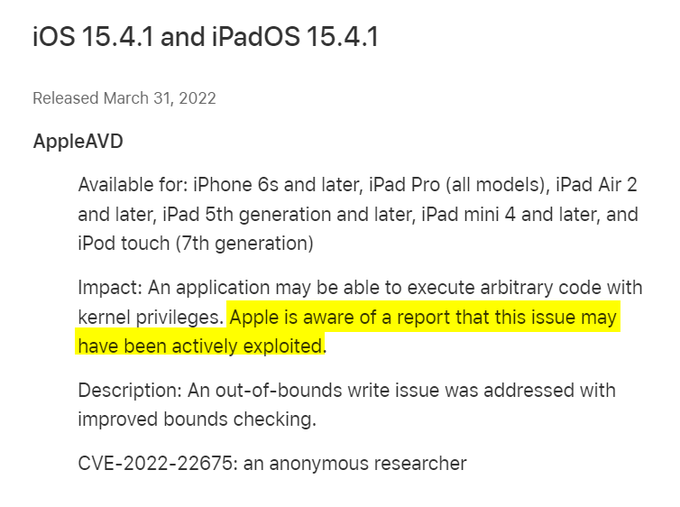
0days everywhere 👀
Cloudflare, Google and AWS on a new zero-day named ‘HTTP/2 Rapid Reset’ being exploited by malicious actors to launch "the largest distributed denial-of-service (DDoS) attacks in internet history"
<- reporting by
@EduardKovacs
4
134
265
NEW! DARPA program manager Perri Adams chats about her love for CTF hacking competitions and the hunt for leapfrog security technologies in the AI cyber challenge
<-- episode sponsored by
@binarly_io
9
76
189
Rachel Tobac has done more for MFA adoption than $10 billion worth of big-tech companies combined.
Salute! 🏆
2
52
188
I asked DEF CON CTF organizer Perri Adams about the make-up of a good capture-the-flag player and for recommendations for someone now getting started
@perribus
7
31
170
Microsoft’s terrible decision to hide info on security bulletins has led to this. A senior Microsoft security guy sharing a script to find the info
If you want a report summarizing today's
#MSRC
security bulletins, here's a script that uses the MSRC Portal API:
9
112
196
4
116
171
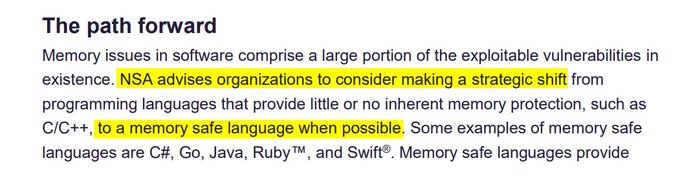
New! A fun conversation with Google Project Zero's Maddie Stone (
@maddiestone
) on 0days, disclosure transparency, memory safety vulns, exploit/samples sharing, and more...
12
36
144
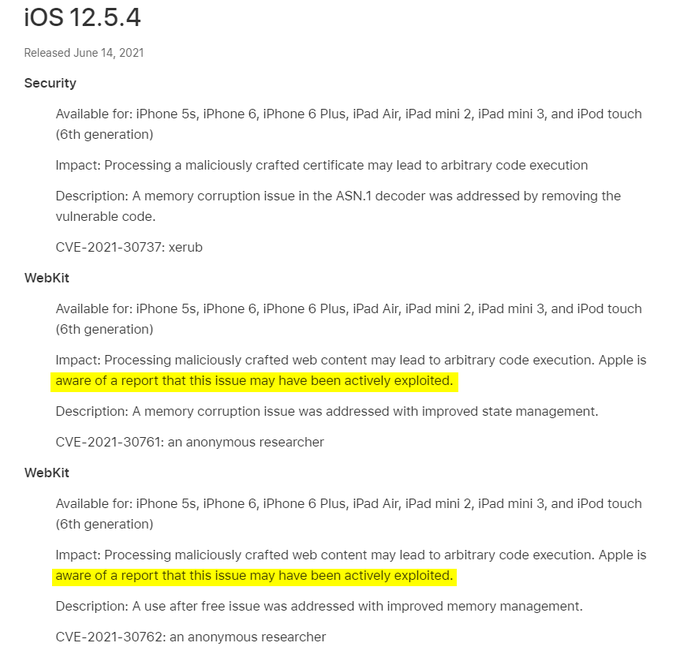
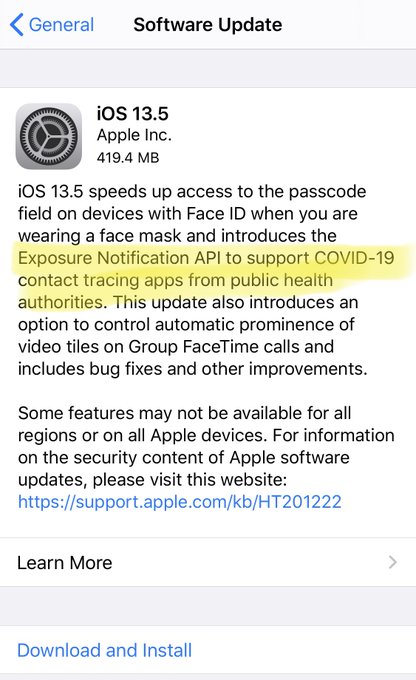
Apple iOS
#FacePalm
patch is live
Two bug finders credited:
CVE-2019-6223: Grant Thompson of Catalina Foothills High School, Daven Morris of Arlington, TX
1
40
125
🎙 New podcast with Shubs Shah (
@infosec_au
), an Aussie hacker who mastered the bug bounty hacking game and is now rewriting the rules of continuous pre-hack reconnaissance.
Enjoy
0
28
131
🥰 DARPA's Dr Sergey Bratus shows love to hackers!
"If you want to understand how systems work or how to break them, go to DEF CON or read Phrack."
@sergeybratus
@DARPA
5
34
132
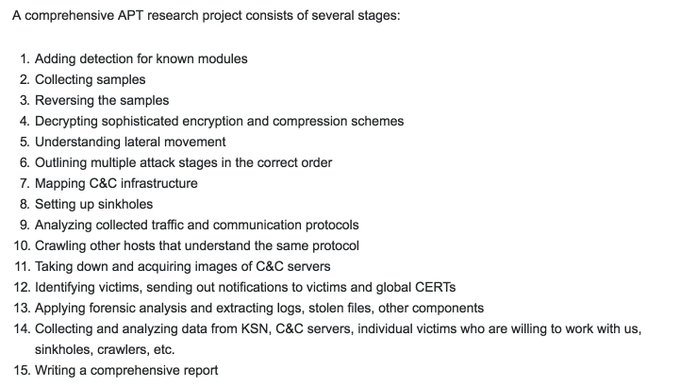
NSA's Rob Joyce (
@RGB_Lights
) at Enigma 2016:
"There’s a reason it’s called advanced persistent
threats. Because we’ll poke and we’ll poke and we’ll wait and we’ll wait and we’ll wait, right? We’re looking for that opening and that opportunity, to finish the mission."
3
37
129
With all the zero-day exploit chatter, I'm republishing this 2013 podcast interview with VUPEN/Zerodium CEO Chaouki Bekrar.
I believe it's the only podcast interview
@cBekrar
has granted and I'd glad I'm able to salvage it for the public record:
2
42
110