Chris Au
@netero_1010
Followers
1K
Following
650
Media
6
Statuses
160
Red teamer, my tools for red teaming: https://t.co/j6Z018m09L, my blog to share offensive security stuff: https://t.co/MKvSTjpWoi
Hong Kong
Joined November 2018
RT @binaryz0ne: Our @cyber5w's next month #DFIR webinar will be about Windows Scheduled Tasks and GhostTask Investigations. #DFIR #Cybersec….
academy.cyber5w.com
Discover the secrets of Windows Forensic Investigations in our exclusive online event. Learn how to master Scheduled Tasks and GhostTasks for enhanced digital investigations.
0
3
0
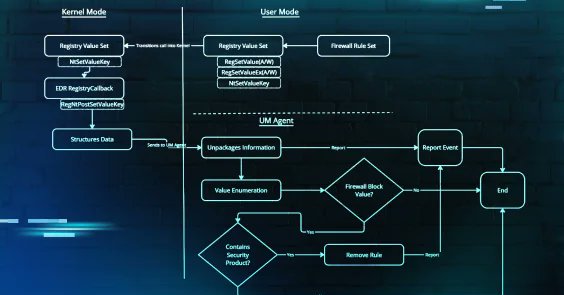
RT @jsecurity101: We have all heard about attackers leveraging firewall policies or WFP to block EDRs from communicating with their servers….
huntress.com
Discover how adversaries are using tools like EDRSilencer to tamper with EDR communications and learn how you can fight back.
0
124
0
Something interesting I found in SCCM remote control.
netero1010-securitylab.com
20 October 2024
6
44
135
RT @NinjaParanoid: Finally, the last release for this year - Brute Ratel v1.8 codename Mirage is here. Various internal updates for evasion….
0
23
0
RT @h4wkst3r: Today I am releasing a whitepaper and new tool (ADOKit) as part of my @XForce research I will be presenting at @BlackHatEvent….
github.com
Azure DevOps Services Attack Toolkit. Contribute to xforcered/ADOKit development by creating an account on GitHub.
0
128
0
Made a tool to create/modify schedule task using just registry keys. It has some requirements (require SYSTEM) but the beauty of it is it wont generate schedule task creation event log.
github.com
A tool employs direct registry manipulation to create scheduled tasks without triggering the usual event logs. - netero1010/GhostTask
6
127
361
RT @BleepinComputer: Microsoft Excel now blocking untrusted XLL add-ins by default - @serghei.
bleepingcomputer.com
Microsoft says the Excel spreadsheet software is now blocking untrusted XLL add-ins by default in Microsoft 365 tenants worldwide.
0
38
0
RT @KlezVirus: [RELEASE] After a little wait, I'm happy to present SilentMoonwalk, a PoC implementation of a TRUE call stack spoofer, resul….
github.com
PoC Implementation of a fully dynamic call stack spoofer - klezVirus/SilentMoonwalk
0
239
0
Having some fun to re-implement indirect syscall in C#.
netero1010-securitylab.com
19 September 2022
1
63
174
RT @Cneelis: It's #BOFFriday so time for a new @OutflankNL C2-Tool-Collection update:.> Psx - Show detailed process information incl. OPSEC….
github.com
A collection of tools which integrate with Cobalt Strike (and possibly other C2 frameworks) through BOF and reflective DLL loading techniques. - outflanknl/C2-Tool-Collection
0
38
0
RT @DebugPrivilege: I've wrote an article a few months ago about Kerberoasting with OpSec and I came across someone's work who wrote a tool….
github.com
OPSEC safe Kerberoasting in C#. Contribute to Luct0r/KerberOPSEC development by creating an account on GitHub.
0
145
0
RT @tiraniddo: I said I'd write up how you could exploit RBCD using a normal user account if you know the password. So here it is https://t….
0
233
0
RT @ly4k_: The first blog post is here. This one covers the technical details of CVE-2022-26923 (Active Directory Domain Services Elevation….
research.ifcr.dk
In this blog post, we’ll dive into a recently patched Active Directory Domain Privilege Escalation vulnerability that I reported through…
0
368
0
RT @rootsecdev: Have fun everyone. Certifried: Active Directory Domain Privilege Escalation (CVE-2022–26923).
research.ifcr.dk
In this blog post, we’ll dive into a recently patched Active Directory Domain Privilege Escalation vulnerability that I reported through…
0
233
0