Explore tweets tagged as #broken_access_control
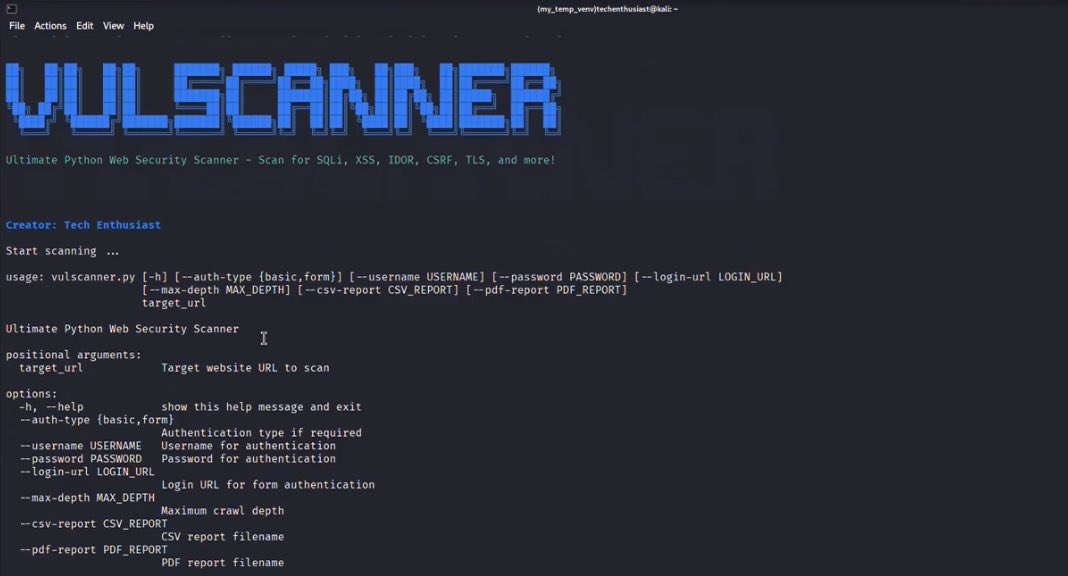
VULSCANNER - Web Security Scanner . This tool automates comprehensive web app security checks - including SQL Injection, XSS, broken access control, missing security headers - and includes powerful OSINT lookup! . #OSINT.#Cybersecurity
16
198
1K
Fuzzing vs broken access control bugs feat. @arthurair_es #bugbounty #bugbountytips #bugbountyhunter
0
3
49
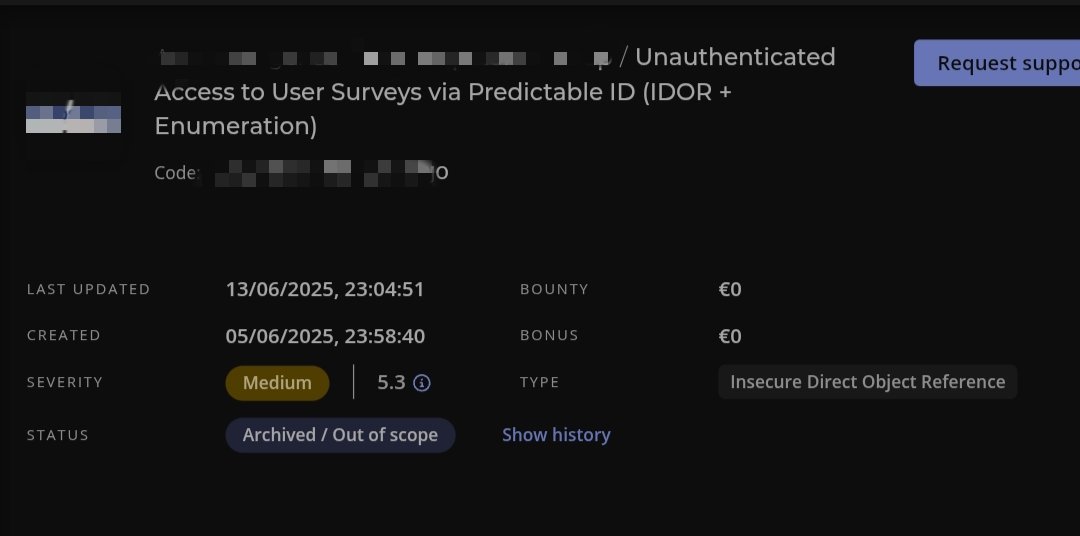
How broken access control vulnerabilities are closed as out of scope and informative,. I started to suffer @intigriti
2
0
22
I’m thrilled to share that a critical bug I reported has been officially resolved by the @USDOD 🦅🇺🇸. Where, just for PoC I was able to exfiltrate 72+ users sensitive information including address and payment info!🚨. 🔍Bug: Broken Access Control (BAC). #BugBounty #CyberSecurity
0
2
24
Bug Bounty Broken Access Control: la vulnerabilidad que abre más puertas de las que imaginas. #bugbounty #bugbountytips #bugbountytip.
1
5
13
⚡ Broken Access Control (IDOR) in Booking Detail and Bids Could Leads to Sensitive Information Disc. 👨🏻💻 back2arie ➟ Bykea .🟥 High.💰 None.🔗 #bugbounty #bugbountytips #cybersecurity #infosec
0
5
42
Thanks to Allah♥️. Thousands Users PIIs leaked due to Broken Access Control at Discourse API. - Accepted.- Public BBP. # Tips and bug details : in the rest tweet thread :-. #bugbountytips .#CyberSecurity
5
9
121
*Broken Access Control* marked as Duplicate on @Hacker0x01, write-up will be published soon on @Medium .#BugBounty #bugbountytips #bugbountytip #hackerone #togetherwehitharder #cybersecurity #appsec #infosec #PenetrationTesting.
1
0
12
Broken Access Control: The Gateway to Unauthorized Privilege Escalation. #bugbounty #bugbountytips #bugbountytip.
0
2
6
🚫 What is Broken Access Control?.It’s when users gain unauthorized access to data or actions they shouldn't. A top cause of .data leaks in apps. 🔐 Learn how to identify & prevent this critical flaw: #AccessControl #AppSecurity #CyberSecurity #InstaSafe.
0
0
0