bom
@bomccss
Followers
6K
Following
2K
Media
513
Statuses
4K
bomb💣 / マルウェアへ感染する日本語の #不審メール ばらまきメールの発信 , Japanese #malspam notificator / focus #ursnif #cutwail #emotet / 組織から独立した個人の活動 , work with community by @Sec_S_Owl
JST(UTC+0900)
Joined March 2017
日本語のマルウェア付きメールが確認されています。.■日時.2025/07/07.■件名.Swiftコピー支払い、デビット金額:3,800,000円 = 26,296.336 USD. ■添付ファイル.attachments[.]zip -> jpy3,800,000 Debit copy.vbs.情報窃取マルウェア #Darkcloud
1
19
35
■URL.hxxps://purchase.vroozi[.]com/admin?nbcu=true#/pr-display/683d93a7167d734268d9e1b9?unitId=54&loginUrl=hxxps://medadliby[.]net/July.exe.-> hxxps://medadliby[.]net/July.exe.■ダウンロードされるファイル.リモートアクセスツール #ConnectWise.
tria.ge
Check this report malware sample 305869d7e90a25f089856e46a82b0e8fce6b04de9e7ee8bad48fdaabcedd0f0b, with a score of 8 out of 10.
0
0
4
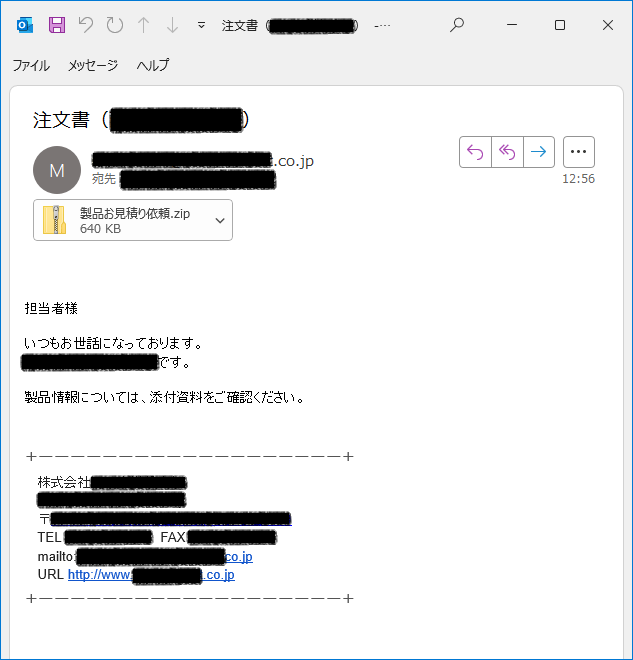
日本語のマルウェア付きメールが確認されています。.■日時.2025/06/27.■件名.注文書([会社名省略]).■添付ファイル.製品お見積り依頼.zip -> .exe.情報窃取マルウェア #VIPKeyLogger ( #SnakeKeyLogger )
0
9
19
日本語のマルウェア付きメールが確認されています。.■日時.2025/06/25.■件名.【お見積もり依頼】 AJYJ-DRD-SPAM-000011825 AM JYOTI.■添付ファイル.【お見積もり依頼】 AJYJ-DRD-SPAM-000011825 AM -> .exe.情報窃取マルウェア #VIPkeylogger
0
9
14
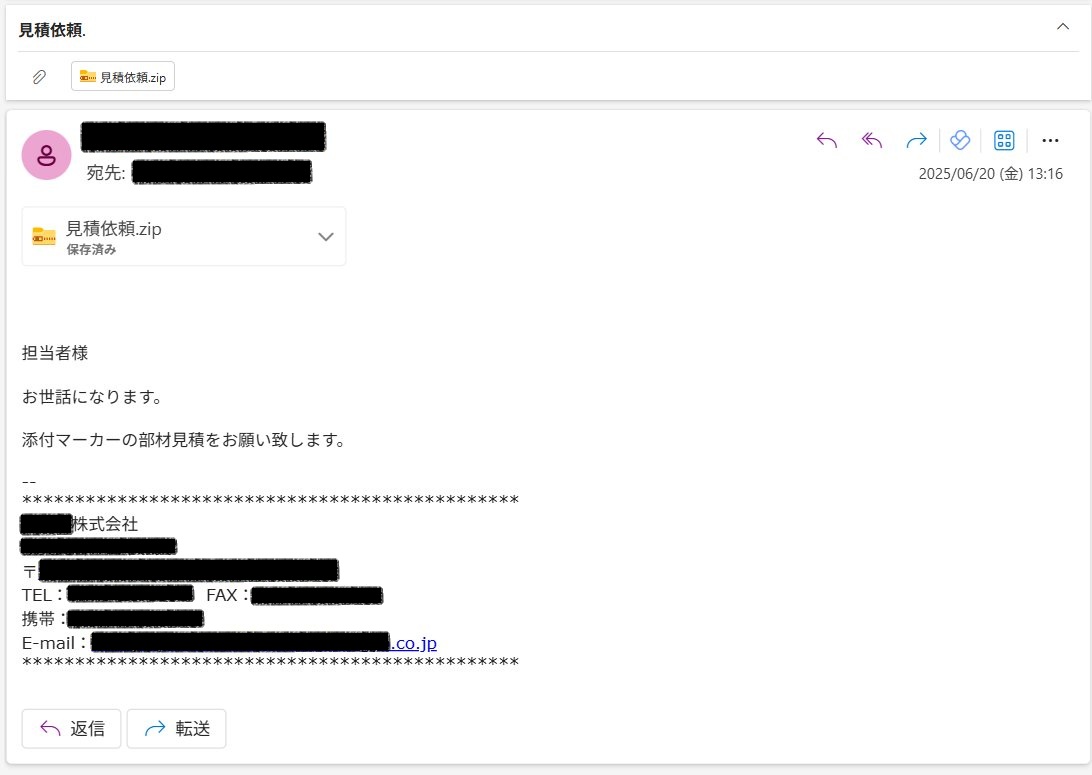
日本語のマルウェア付きメールが確認されています。. ■日時.2025/06/20.■件名.見積依頼. ■添付ファイル.見積依頼.zip-> .exe.情報窃取マルウェア #VIPkeylogger ( #SnakeKeyLogger )
0
7
15
日本語のマルウェア付きメールが確認されています。. ■日時.2025/06/12.■件名.見積依頼.■添付ファイル.見積依頼フォーム-> .exe.情報窃取マルウェア #VIPkeylogger ( #SnakeKeyLogger ).
tria.ge
Check this report malware sample b8609dddbf093a66ade9a481961e60e7c63ef97e79a68b9ea11f5a209d546f52, with a score of 8 out of 10.
日本語マルウェアメールの接到を確認しています。 #malspam in Japanese.件名 : 見積依頼.MD5: f03cccdc1a45d00b805d5e5b70c4a1ce.C2 : api[.]telegram[.]org.Sample :
0
7
19
昨日、日本語のマルウェア付きメールが確認されています。. ■日時.2025/06/11.■件名.給与 - 要スタッフ確認.■添付ファイル.Salary_Approval.rar -> .exe.マルウェア #Remcos.
tria.ge
Check this remcos report malware sample 645e77f1311ebc3904768208d0193543d52b2ab2aa4d710d0b3762ddaa572e6c, with a score of 10 out of 10.
日本語マルウェアメールの接到を確認しています。.#malspam in Japanese #remcos. 件名 : 給与 - 要スタッフ確認.MD5: adb5b08ab045e67493a7eaf83700977b.C2 : 196.251.72[.]191:5001.Sample :
0
3
5
RT @58_158_177_102: 日本語マルウェアメールの接到を確認しています。 #malspam in Japanese.件名 : 見積依頼.MD5: f03cccdc1a45d00b805d5e5b70c4a1ce.C2 : api[.]telegram[.]org….
0
4
0
RT @58_158_177_102: 日本語マルウェアメールの接到を確認しています。.#malspam in Japanese #remcos. 件名 : 給与 - 要スタッフ確認.MD5: adb5b08ab045e67493a7eaf83700977b.C2 : 196.….
0
16
0
昨日、日本語のマルウェア付きメールが確認されています。. ■日時.2025/04/30.■件名.消耗部品お見積り依頼の件。.■添付ファイル.消耗部品お見積り依頼の件。.zip -> .exe.情報窃取マルウェア #SnakeKeyLogger (#vipkeylogger)
0
15
39
日本語のマルウェア付きメールが確認されています。. ■日時.2025/04/24.■件名.給与支払通知書 - お客様の状況をご確認ください.■添付ファイル.payroll list.rar -> .exe.#Guloader + #Remcos.
tria.ge
Check this guloader report malware sample 5f64f43a5b646d5d756321ac9c3a63b0bcb317bee2b80f09b117ae31cb7071b1, with a score of 10 out of 10.
日本語マルウェアメールの接到を確認しています.#malspam in Japanese #Remcos + #Guloader. Subject : 給与支払通知書 - お客様の状況をご確認ください.MD5 : 1e46d547d109ac4a4d53cb22dcad51cb.Payload from : drive[.]google[.]com.C2 : 196.251.116[.]218:2007.Sample :
1
10
29
RT @58_158_177_102: 日本語マルウェアメールの接到を確認しています.#malspam in Japanese. 件名 : [DHL Japan]ジャパン – 貨物に関する書類不足のご案内.MD5 : b69cd646fa1baa710b2f4be2dfc1e7….
0
10
0
日本語のマルウェア付きメールが確認されています。. ■日時.2025/04/08.■件名.注文書(西日本常盤商行).■添付ファイル.常盤注文書.zip -> .exe.情報窃取マルウェア #SnakeKeyLogger (#vipkeylogger)
0
11
26
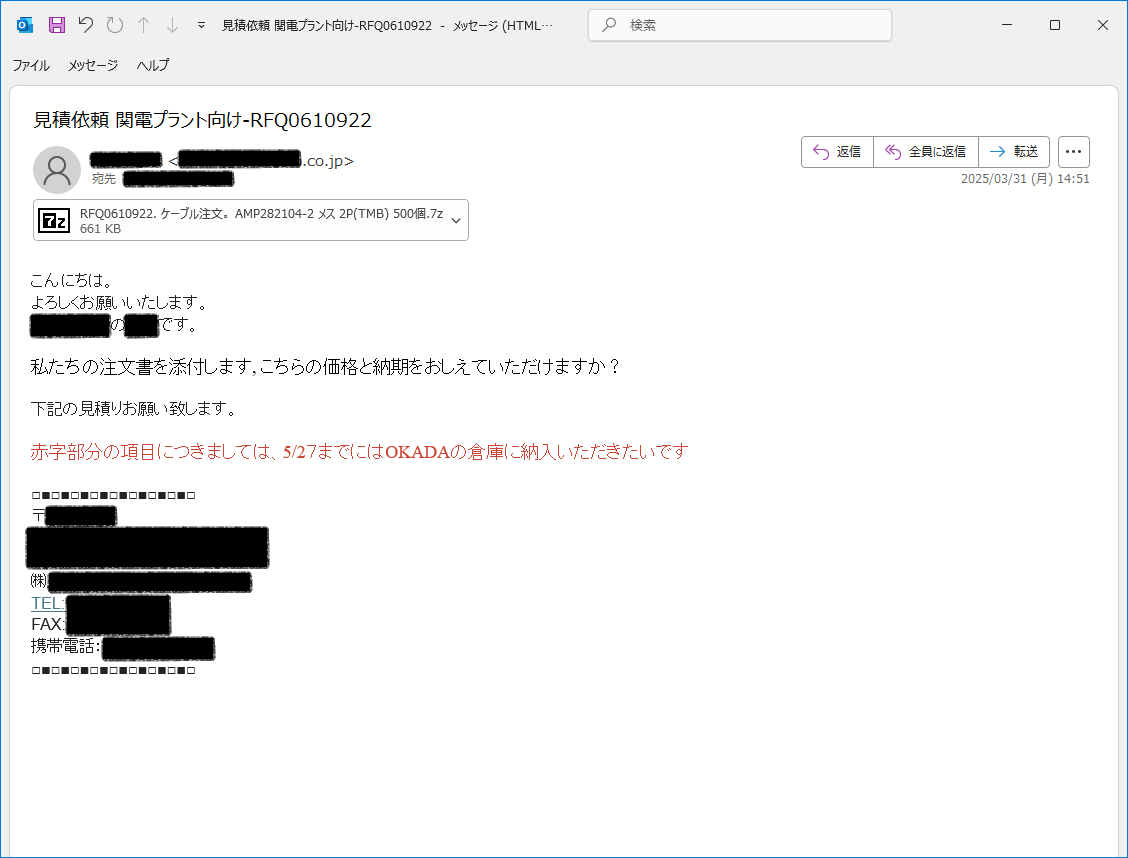
日本語のマルウェア付きメールが確認されています。. ■日時.2025/03/31.■件名.見積依頼 関電プラント向け-RFQ0610922.■添付ファイル.RFQ0610922. ケーブル注文。 AMP282104-2 メス 2P(TMB) 500個.7z -> .exe.情報窃取マルウェア #SnakeKeyLogger
0
20
54