Kostas
@Kostastsale
Followers
18K
Following
9K
Media
916
Statuses
5K
@TheDFIRReport | No longer active here – find me on Bluesky: https://t.co/qHzDSxCRfG. 🇬🇷🇨🇦
Joined February 2017
Why I’m Leaving Twitter – A Thread. 1/ If you know me on a personal level, you’ll know I don’t do backflips. This decision hasn’t been taken lightly. It’s hard to leave behind the community we’ve built, but if you care to understand why, keep reading.
14
4
118
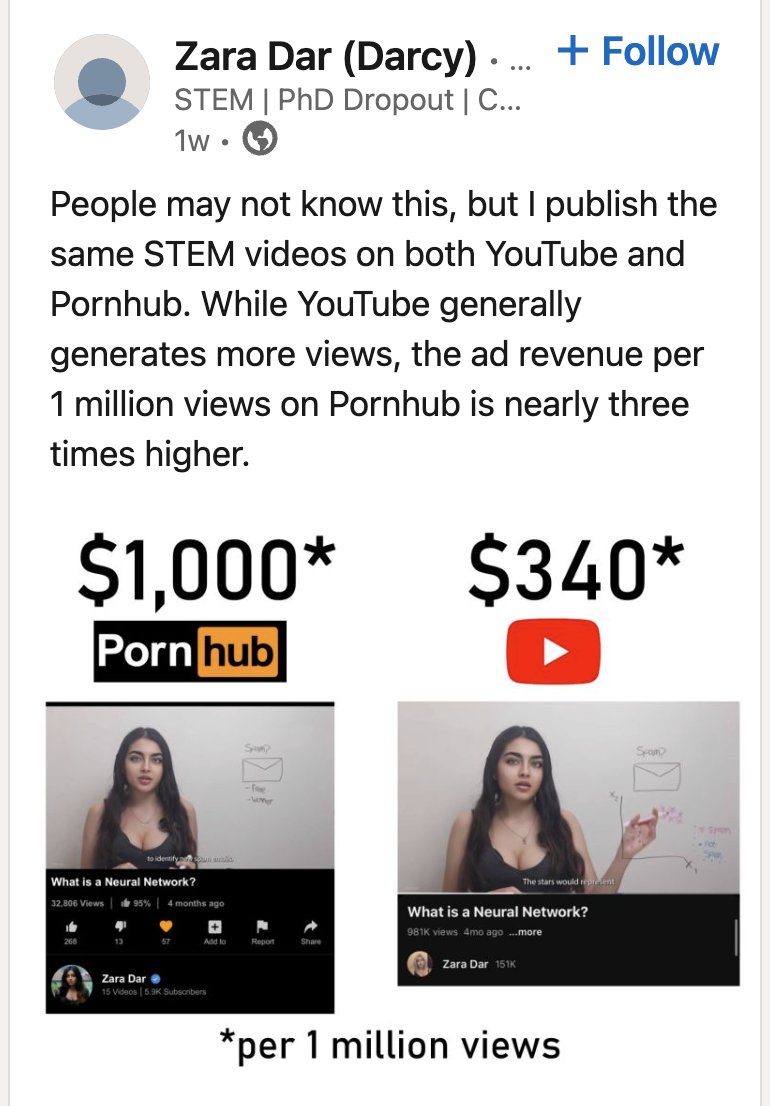
Turns out the real secret to better CPMs is uploading to the "forbidden" platform. 😏. - @_JohnHammond @mattjay @cybercdh @NetworkChuck @MyDFIR when are you. branching out?! 😂😂. Rumours have it that you can negotiate better deals for "penetration testing" topics 😆
3
0
6
🎙️ New podcast is live - Mastering Malware Analysis: Tools, Techniques, and Insights. I enjoyed making this one. Covers a lot of things that I always get asked about. Hope you find it helpful & educational 🙂. 🎧 Check it out: Let me know what you think!.
creators.spotify.com
In this episode, Bob and Alice take you on an educational journey through malware analysis. They break down key techniques like static and dynamic analysis, memory forensics, and reverse engineering...
0
13
64
We had fun discussing our latest report on a podcast episode. We breakdown the more_eggs malware and getting into the mindset of the threat actor. You’ll listen to what we’re thinking of when analyzing the intrusion. Check it out from the provided links 👇.
🎉New DFIR Discussions Episode🎉. 🔊Available on Spotify, Apple, & YouTube!. 🎙️ We discuss our latest report "The Curious Case of an Egg-Cellent Resume". Host: @Kostastsale. Analysts: @_pete_0 & @svch0st. 👇 Podcast links below.
0
0
2