Ax Sharma
@Ax_Sharma
Followers
5K
Following
25K
Media
593
Statuses
4K
Infosec Researcher, Journalist | 📰 Bylines + seen on 📸 BBC, BleepingComputer, Channel 5, TechCrunch, WIRED | 🦋 Bluesky: https://t.co/7LQOdDSG1o | ✉️ [email protected]
🇨🇦🇬🇧
Joined April 2016
RT @BleepinComputer: Hacker sneaks infostealer malware into early access Steam game - @billtoulas. .
bleepingcomputer.com
A threat actor called EncryptHub has compromised a game on Steam to distribute info-stealing malware to unsuspecting users downloading the title.
0
50
0
RT @securestep9: #NPM package 'is' with 2.8M weekly .downloads was compromised and infected developers with malware:.#AppSec.#SoftwareSuppl….
bleepingcomputer.com
The popular NPM package 'is' has been compromised in a supply chain attack that injected backdoor malware, giving attackers full access to compromised devices.
0
1
0
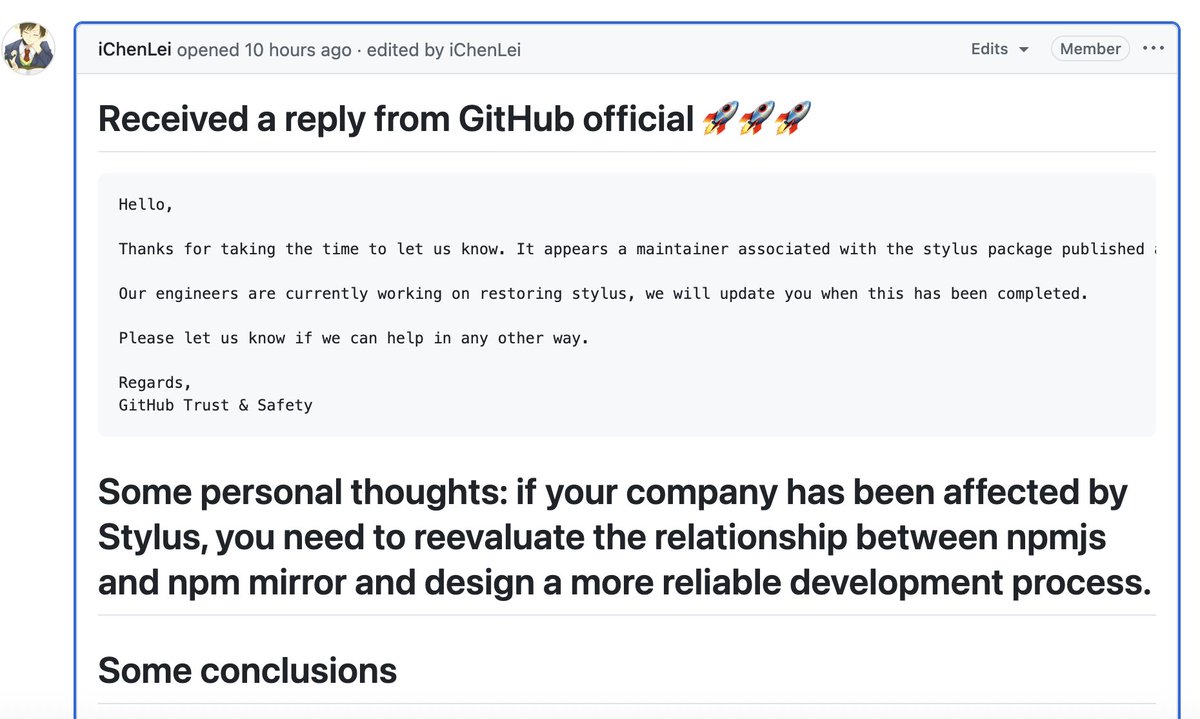
npm has "accidentally" taken down all versions of the legitimate Stylus library and replaced them with a "security holding" page, breaking pipelines and builds worldwide. @Mend_io's @abai_tom has cracked the puzzle:. #opensource #supplychain #javascript.
bleepingcomputer.com
npm has taken down all versions of the Stylus library and replaced them with a "security holding" page, breaking pipelines and builds worldwide that rely on the package.
1
1
4
RT @BleepinComputer: ExpressVPN bug leaked user IPs in Remote Desktop sessions - @billtoulas. .
bleepingcomputer.com
ExpressVPN has fixed a flaw in its Windows client that caused Remote Desktop Protocol (RDP) traffic to bypass the virtual private network (VPN) tunnel, exposing the users' real IP addresses.
0
109
0
RT @MalwareUtkonos: @Ax_Sharma got-fetch also contains a malicious DLL of the same malware family called "crashreporter.dll".30295311d62893….
0
4
0
Gathering threat intel, unmasking perps behind cyber attacks and bringing down entire ransomware gangs are just some of the ways the dark web is used by defenders.
csoonline.com
Gathering threat intelligence, finding the perpetrators of cyber attacks and bringing down whole ransomware gangs are some of the ways the dark web is used by defenders.
0
0
2
One wrong click, on the maintainer's part, could put millions at risk. Hijacking legitimate libraries has become a recurring attack vector in recent times, given both the fragility of and the trust that the open-source ecosystem operates on.
bleepingcomputer.com
Popular JavaScript libraries eslint-config-prettier and eslint-plugin-prettier were hijacked this week and turned into malware droppers, in a supply chain attack achieved via targeted phishing and...
1
1
9
RT @BleepinComputer: '123456' password exposed info for 64 million McDonald’s job applicants - @LawrenceAbrams. htt….
bleepingcomputer.com
Cybersecurity researchers discovered a vulnerability in McHire, McDonald's chatbot job application platform, that exposed the chats of more than 64 million job applications across the United States.
0
140
0
RT @MikaelThalen: EXCLUSIVE: I discovered evidence that an IMSI-catcher, commonly called a Stingray, was used during a July 4 protest at an….
san.com
Mobile network anomalies consistent with cell phone surveillance were detected at a July 4 protest at an ICE field office in Washington state.
0
98
0
Exclusive: Instagram ads appearing to be from Bank of Montreal (BMO) are using AI deepfake videos to scam consumers into investment fraud. Ads for 'EQ Bank' take users to phishing domains to collect their banking information.
bleepingcomputer.com
Instagram ads impersonating financial institutions like Bank of Montreal (BMO) and EQ Bank (Equitable Bank) are being used to target Canadian consumers with phishing scams and investment fraud. Some...
0
0
3
RT @BleepinComputer: Washington Post's email system hacked, journalists' accounts compromised - @billtoulas. https:….
bleepingcomputer.com
Email accounts of several Washington Post journalists were compromised in a cyberattack believed to have been carried out by a foreign government.
0
48
0
RT @mayank_jee: Google AI Overviews is terrible, and you should be careful when believing what it says. It’s better to use Bing, which give….
0
4
0
RT @BleepinComputer: Jira Down: Atlassian users experiencing degraded performance - @Ax_Sharma. .
bleepingcomputer.com
Atlassian users are experiencing degraded performance amid an 'active incident' affecting multiple Jira products since morning hours today. Jira, Jira Service Management, Jira Work Management...
0
21
0
RT @hackerfantastic: North Korea stole $1.4billion by injecting JavaScript through an AWS S3 bucket to spoof the UI interface during a tran….
0
950
0
Fake VS Code extension on npm uses altered ScreenConnect utility as spyware.h/t @SnifferNandez @sonatype .
sonatype.com
A fake 'Truffle for VS Code' npm package delivers stealthy malware via a ScreenConnect installer. Learn how it evades detection and threatens developers.
0
0
1
RT @BleepinComputer: Google Play, Apple App Store apps caught stealing crypto wallets - @billtoulas. .
bleepingcomputer.com
A new campaign dubbed 'SparkCat' has been uncovered, targeting the cryptocurrency wallet recovery phrases of Android and iOS users using optical character recognition (OCR) stealers.
0
25
0
RT @BleepinComputer: Exclusive: Hotel management platform Otelier suffered a data breach after threat actors breached its Amazon S3 cloud s….
bleepingcomputer.com
Hotel management platform Otelier suffered a data breach after threat actors breached its Amazon S3 cloud storage to steal millions of guests' personal information and reservations for well-known...
0
114
0