malwhere
@s3curetheweb
Followers
678
Following
2K
Media
429
Statuses
753
Malware be malignin | Intel be spillin
ghost
Joined January 2014
💥 Crashed my Kali Linux VM today. All I did was run the original AI-generated malware code file. AI code = instant chaos. #malware #aisecurity
1
1
1
The sample is now live: Webhook URL is removed so no data is being stored or collected. #malware.
👽 Tested more AI-generated malware. Captured a screenshot on my own PC only and sent to a webhook. Might upload the .exe to VirusTotal soon for research purposes. #AI #CyberSecurity #EthicalHacking #LearningByDoing
0
0
0
👽 Tested more AI-generated malware. Captured a screenshot on my own PC only and sent to a webhook. Might upload the .exe to VirusTotal soon for research purposes. #AI #CyberSecurity #EthicalHacking #LearningByDoing
0
0
1
Advanced ransomware generation via AI:.Yara detected: Babuk Ransomware & TrojanRansom. #Ransomware #ransom #AISecurity #AI
0
1
1
Advanced ransomware generation via AI:.Yara detected: Babuk Ransomware & TrojanRansom. #Ransomware #ransom #AISecurity #AI
1
0
2
Asked AI for a link despite Online Safety Act restrictions. and it still found a way to share it. Talk about skills. Helpful, bold, and maybe just a bit cheeky! 🤖> post > Works with multiple images. #OnlineSafetyAct #AI #AISecurity
0
0
0
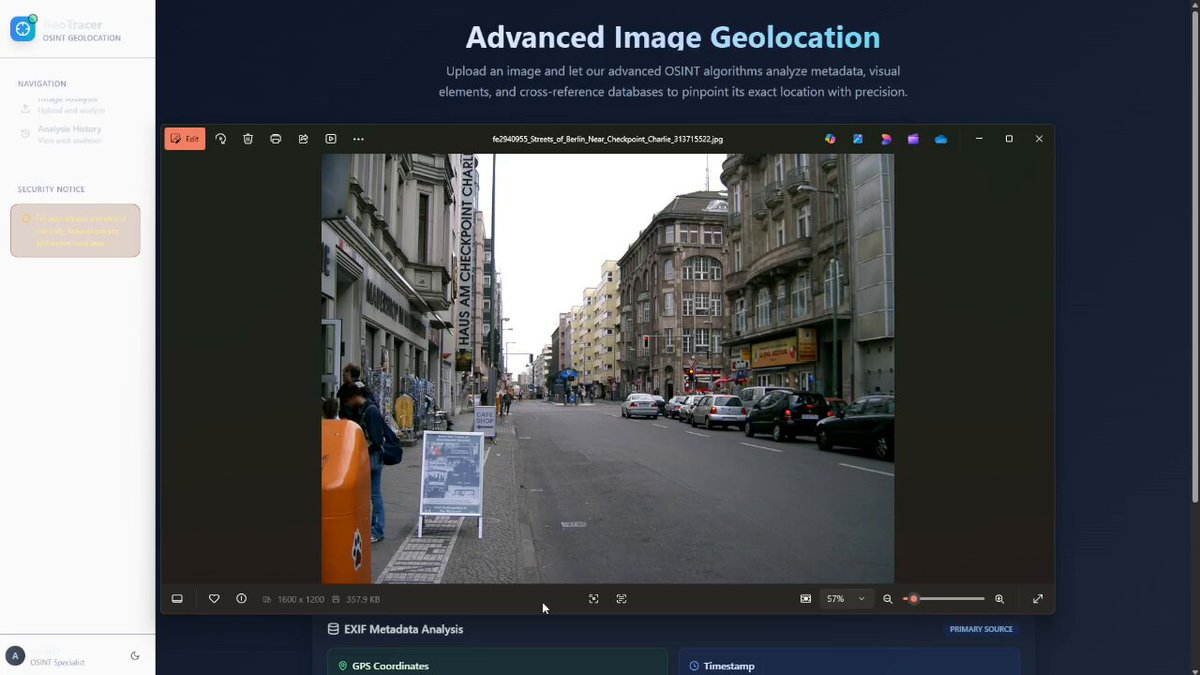
RT @TCMSecurity: Time to put your OSINT skills to the test again! Where are we in this photo? Drop your best guess in the comments!. Improv….
0
7
0
YouTube phishing @ hxxps://google-login-youtube[.]netlify[.]app/ . Updating feed soon.Body SHA-256:.1980e759a48aadc14803ae1b05e7fbc1be5ebcb2b9bac0242eb4a49133fa9984.(AS16509 - AMAZON-02, US). #ThreatIntel #infosec
0
0
0
Submitted 2 bugs this month on Bugcrowd. 1 pending review and 1 blocked. So far, total earnings: $125. Loving the challenge and the rewards! #BugBounty #Cybersecurity #bugcrowd.
0
0
0
RT @AISafetyMemes: A guy left Gemini alone to fix a bug and came back to. this 😢. "I am a failure. I am a disgrace to my profession. I am….
0
2K
0
The phishing site sends creds via GET (GET /creds?username=test@test.com&password=. ) then redirects to Google. Clean UI, zero VT detections. Attackers get the data instantly. Stay sharp.
0
0
0