0xDamian
@damnsec1
Followers
6K
Following
36K
Media
3K
Statuses
21K
Ex Instructor @Cisco x @Cyblackorg | 21 | NG 🇳🇬 | Speaks 🇩🇪🇷🇺 sometimes | eJPTv2 | WebApp and Network Pentester | INTJ | Refuses to elaborate further
Sexurity Conslutant
Joined January 2022
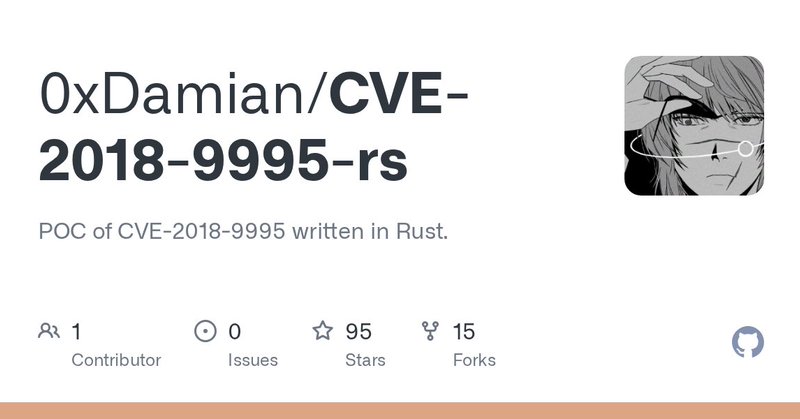
Hack CCTV cameras using my tool written in Rust. Ethically, of course. GitHub Link: https://t.co/tk0cadNnxf
github.com
POC of CVE-2018-9995 written in Rust. Contribute to 0xDamian/CVE-2018-9995-rs development by creating an account on GitHub.
18
133
964
I did have a target of getting to 10k followers by the end of the year, not sure why, it's just a nice round number. Only 195 to go, if you like web app security, CTF or full stack dev give us a follow, if you already follow give us a share 🙏
2
9
31
It's called "SOLO Leveling", bro. Not "A show with an actual plot and well written characters that have a character-to-character dynamic and interaction instead of existing just to say 'He's on a different level'"
the fact that the only character on the cover art is just protag being put there three times is insanely ironic
0
1
4
0
0
6
One of my goals in 2026 is to support Cyber friends with laptops. There will be no pressure, it will be based on my capacity.
56
51
308
Why is Gimp in there. Lol
0
0
1
The fact that "Oranges" could've been any other fruit is irrelevant because any other fruit is treated the same as Oranges, as the strength in my analogy is based on Apples being the focal point of the convo. 8/8
0
0
0
Apples are substituted with women, and men are substituted with oranges. 7/8
1
0
0
This exact logic can be applied to the initial discussion with substituted values. "If the discussion is focused SOLELY on the women-only cybersecurity sponsorship, then considerations of initiatives for the other gender or any other unrelated initiatives are irrelevant." 6/8
1
0
0
This is English for "If the discussion is focused SOLELY on apples, then considerations of oranges or any other fruit or unrelated topic are irrelevant." 5/8
1
0
0
The statement "If the topic is about apples and only apples, oranges or any other fruit or an unrelated topic is irrelevant" is logically represented as, like I've stated: (Tx∧¬Ty∧¬Tz)→(Iy∧Iz) 4/8
1
0
0
Irrelevances: Iy: represent "Oranges are irrelevant to the current discussion." Iz: represent "Any other fruit or unrelated topic is irrelevant to the current discussion." 3/8
1
0
0
Tx∧¬Ty∧¬Tz: meaning "The topic is about apples, and not about oranges, and not about any other fruit or unrelated topic." 2/8
1
0
0
The logical expression for my analogy is: (Tx∧¬Ty∧¬Tz)→(Iy∧Iz) Let Tx represent "The topic is about apples." Let Ty represent "The topic is about oranges." Let Tz represent "The topic is about any other fruit or unrelated topic (e.g., bananas, or something different)." 1/8
@damnsec1 @i4gaau No it won't. The direct involvement comes from the fact that it was the availability of only two genders that brought about the question in the first place. Your analogy can only stand or hold water if the setting is one in which only Apples and oranges are available.
3
0
1
Tech bros: "We need more women in tech fr" Tech bros when there's an initiative to bring more women in tech:
1
4
19
I'm trying so hard, yet not hard enough. Not hard enough to even look back at my achievements with a smile. My eyes aren't letting me see that I've done well. It looks so bland in comparison to the standard I've set for myself. It's never enough. I must win, I have to.
5
6
51