Chris Sanders 🔎 🧠
@chrissanders88
Followers
31,915
Following
505
Media
1,590
Statuses
14,263
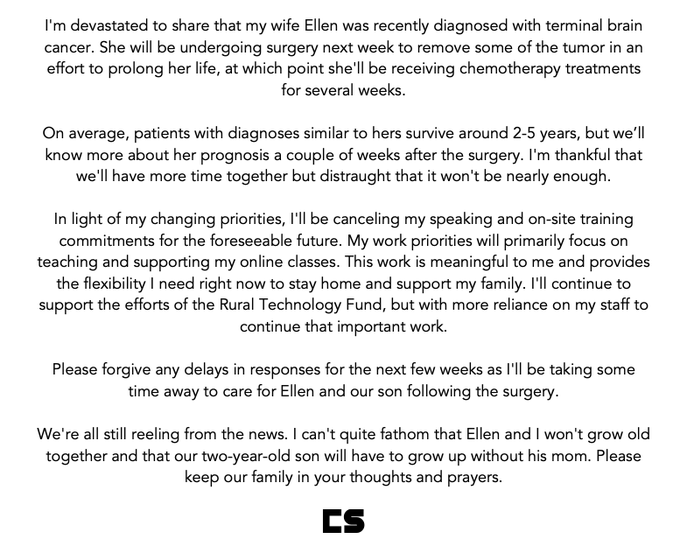
Ed.D. | Founder @networkdefense @RuralTechFund | Former @Mandiant , DoD | Author: Intrusion Detection Honeypots, Practical Packet Analysis, Applied NSM
Mayfield KY ➡️ Gainesville GA
Joined July 2008
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
Rio Grande do Sul
• 201547 Tweets
Madonna
• 156305 Tweets
Bucks
• 74997 Tweets
Dame
• 58630 Tweets
Knicks
• 53496 Tweets
Racing
• 53112 Tweets
Pacers
• 45184 Tweets
Sixers
• 34213 Tweets
#911onABC
• 32151 Tweets
bruno mars
• 28205 Tweets
憲法改正
• 27325 Tweets
Pabllo
• 26750 Tweets
dua lipa
• 22312 Tweets
Giannis
• 21496 Tweets
Rony
• 20947 Tweets
Bruins
• 15629 Tweets
Anne Hathaway
• 15150 Tweets
Costas
• 14848 Tweets
Lillard
• 14237 Tweets
#SnowMan結成12周年
• 13473 Tweets
76ers
• 12529 Tweets
Arias
• 12285 Tweets
Estevão
• 11858 Tweets
#LeafsForever
• 11422 Tweets
Talleres
• 10575 Tweets
Last Seen Profiles
Look at this slice of awesome. The new Wireshark version in dev (3.3.0) has a packet diagram view.
A fantastic teaching and learning tool! When released, I'll be making pretty extensive use of this in my classes! Great job
@geraldcombs
and
@WiresharkNews
team.
93
3K
7K
I know a lot of teachers right now are getting their classrooms ready for the new year. You're loved and appreciated.
If you've got a classroom wishlist...
Reply to this tweet with your wish list link
AND
Follow me or open your DMs so I can message you
#clearthelist
📚🎁😄
1K
273
866
I know a lot of teachers right now are getting their classrooms ready for the new year. You're loved and appreciated.
If you've got a classroom wishlist...
Reply to this tweet with your wish list link
AND
Follow me or open your DMs so I can message you
#clearthelist
📚🎁😄
1K
278
728
I’m excited to launch our latest online course, YARA for Security Analysts.
We built this course for people who want to learn to write YARA rules for detection engineering, system triage, incident response, and threat intel research.
#Yara
#DetectionEngineering
#DFIR
#Malware
6
174
655
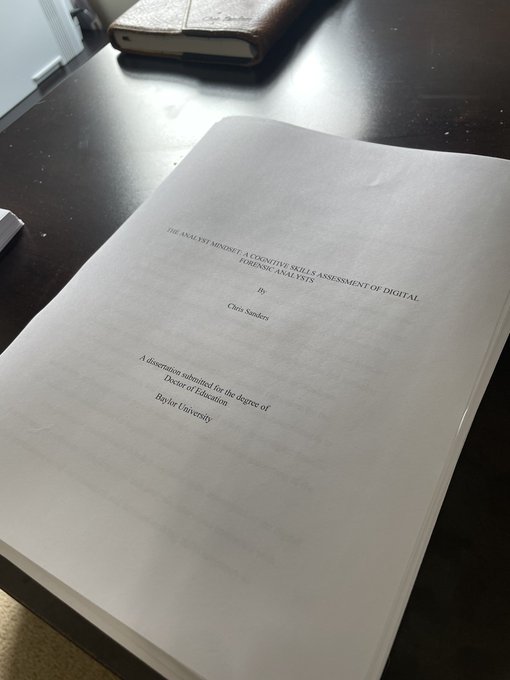
My newest book, Intrusion Detection Honeypots: Detection through Deception, is out today. 🍯
You can read about it here:
You can buy it here:
#idhbook
42
172
595
My entire
#cuckoosegg
Intro to Infosec course is now available as a free download here:
This includes recordings, lecture notes, and slides.
9
287
507
After many months of design, planning, and building... I finally finished this massive set of built-in bookshelves today.
#woodworking
#shelfie
43
7
463
Investigation Scenario 🔎
HR suspects that a former employee may have taken sensitive data when they quit.
What do you look for to investigate this event?
Assume you have access to any evidence source you want, but no commercial DLP tools.
#InvestigationPath
#DFIR
#SOCAnalyst
72
81
462
I'm beyond excited to announce the newest
@NetworkDefense
online course: CyberChef for Security Analysts. 👨🍳👩🍳
You can learn more and sign up for it here: .
7
129
413
I've also got a free signed copy for whoever replies to *this* tweet with their favorite recipe that includes honey as an ingredient.
299
129
325
I’ve been working with
@da_667
to turn his Building Virtual Labs book into a “Choose Your Own Adventure" online course for
@NetworkDefense
. I think it turned out really well, and it’ll be open on Thursday.
You can read about it here:
14
80
281
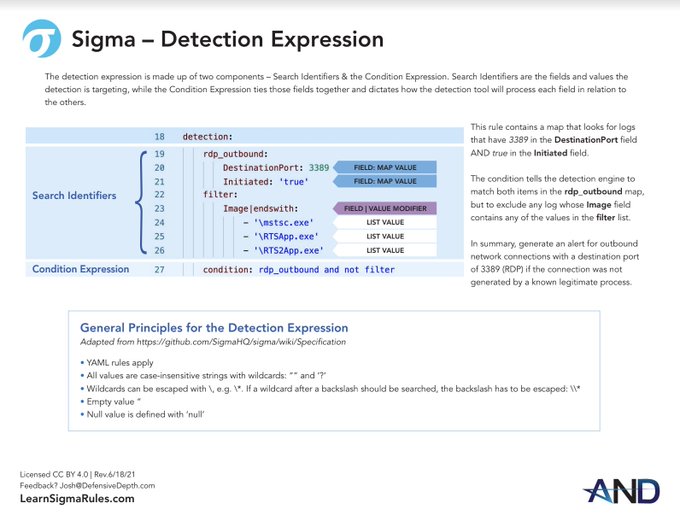
We put together a
@sigma_hq
cheat sheet while building our Detection Engineering with Sigma online course.
Even if you don't take the course, you can grab the cheat sheet for free here:
Course Details:
2
114
268
By the way, when I say great tools don't just help people do a job, they teach them how to do it...this is an example.
Sometimes it's nudging people toward decisions. Here, it's simplifying complexity using visual reference models.
Look at this slice of awesome. The new Wireshark version in dev (3.3.0) has a packet diagram view.
A fantastic teaching and learning tool! When released, I'll be making pretty extensive use of this in my classes! Great job
@geraldcombs
and
@WiresharkNews
team.
93
3K
7K
3
53
247
Investigation Scenario 🔎
While hunting through O365 logs, you discovered the depicted entry related to one of your user’s mailboxes.
The user is on vacation for a week and unreachable. What do you look for to investigate whether an incident occurred?
#InvestigationPath
#DFIR
40
47
238
Well folks, we raised $11,000 for the
@RuralTechFund
at
@DerbyCon
. That’ll change a lot of lives.
Thank you to everyone who came by and bought a shirt or raffle ticket.
7
44
242
Shout out to
@CISAKrebs
and others like him in government service who lose their jobs doing what’s right. I’ve been there too. You’re on the right side of history and we see you.
1
21
238
I just published the third article in my series dedicated to analyzing large PCAPs.
This one focuses on distilling PCAPs down to key events with Suricata, Bro, PRADS, and more.
I also mention the
@securityonion
so-import-pcap script.
3
112
232
It's been a while since I've updated on Ellen's condition. Unfortunately, her cancer has progressed significantly in the past couple of months. We recently decided to forgo further treatment and pursue hospice care as she enters her final weeks.
88
3
228
Couldn’t have this list without this book.
21
16
223
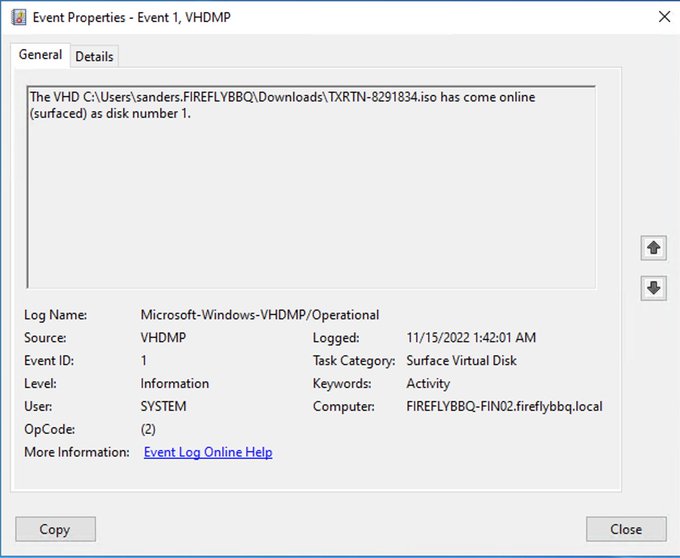
Investigation Scenario 🔎
A system mounted a file named TXRTN_8291834.iso.
What do you look for to determine if this system is infected and identify the potential malware?
The file is no longer available but you can use any other evidence source you like.
#InvestigationPath
14
37
207
Very excited to share that we raised over $8000 for
@RuralTechFund
at
@Derbycon
. This shatters last years total. 100% of that will go to classrooms in rural areas, helping us introduce thousands of students to technical education. I’m grateful for everyone who contributed!
6
48
192
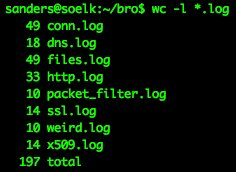
I'm pretty impressed with Brim. It's a really quick way to break down a PCAP into Zeek logs, do some quick analysis, and even pivot back into smaller PCAPs.
#SOC
Repo:
Download:
Demo:
3
84
193
I've purchased about $5K worth of items off of teacher wishlists so far. I'll be doing some more tomorrow and through the weekend.
#clearthelist
🚀
123
20
183
I'm really honored to have won the SANS Difference Makers Award for my work with the RTF.
This was quite a shock, and I appreciate SANS recognizing the cause of helping expose more rural kids to technology education.
Congratulations to the winners of the 2018 Difference Makers Award! The Difference Makers Awards were created to honor the unsung heroes in
#cybersecurity
whose innovation, skill, and hard work have resulted in real successes in information security.
1
11
22
17
18
183
@mattifestation
Another way I've heard this said is "There comes a time when you have to stop admiring the problem."
2
40
179
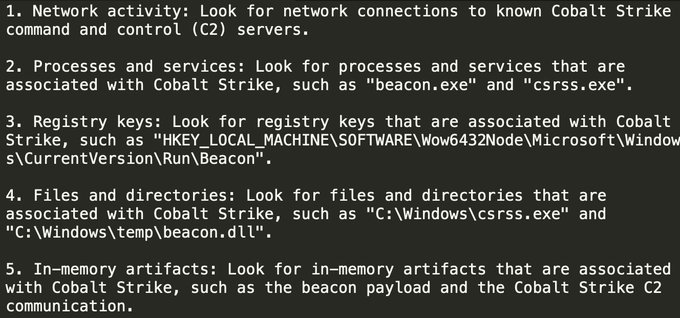
Investigation Scenario 🔎
A user reported their mouse moving around on the screen by itself for a few minutes. The cursor appeared to open and close a few documents on the desktop.
What do you look for to investigate whether an incident has occurred?
#InvestigationPath
#DFIR
42
35
178
Some of the work I'm most proud of from my time at Mandiant was pioneering the building of investigative actions *into detection signatures* as they were written. This had profound impact across the detection and product teams, and made the tool so much more accessible.
4
36
179
Investigation Scenario 🔎
You’ve discovered regsvr32.exe running from the C:\Users\Username\Appdata\Roaming directory on a Windows system.
What do you look for to investigate whether an incident occurred?
#InvestigationPath
#DFIR
#SOC
16
26
174