Adrian Grigorof
@AdiGri
Followers
426
Following
214
Media
63
Statuses
269
CTO @ Managed Sentinel
Toronto, Ontario
Joined July 2008
Our latest diagram is covering the Microsoft Copilot for Security - any feedback is appreciated! . #copilotforsecurity @BlueVoyant
0
1
3
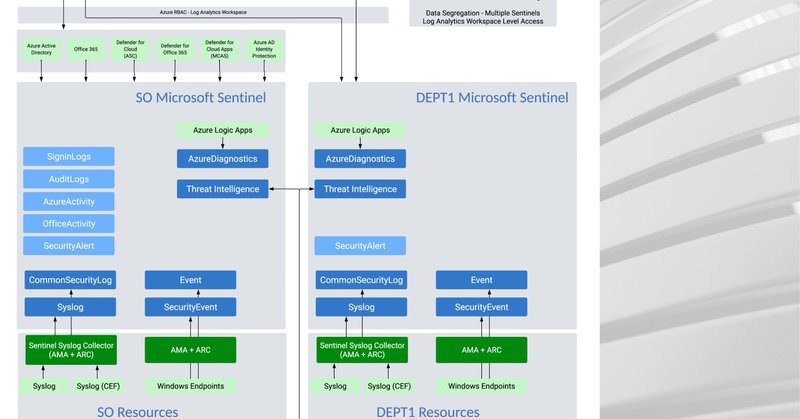
Segregation of access to logging data is a crucial topic that arises during Microsoft Sentinel architecture sessions. This blog post provides some of the common ways to implement it. @BlueVoyant #microsoftsentinel.
managedsentinel.com
So, you want to segregate your data in Sentinel? Well, you came to the right place! In this blog we are going to review four different ways that you can segregate data in Microsoft Sentinel. Keep in...
0
0
1
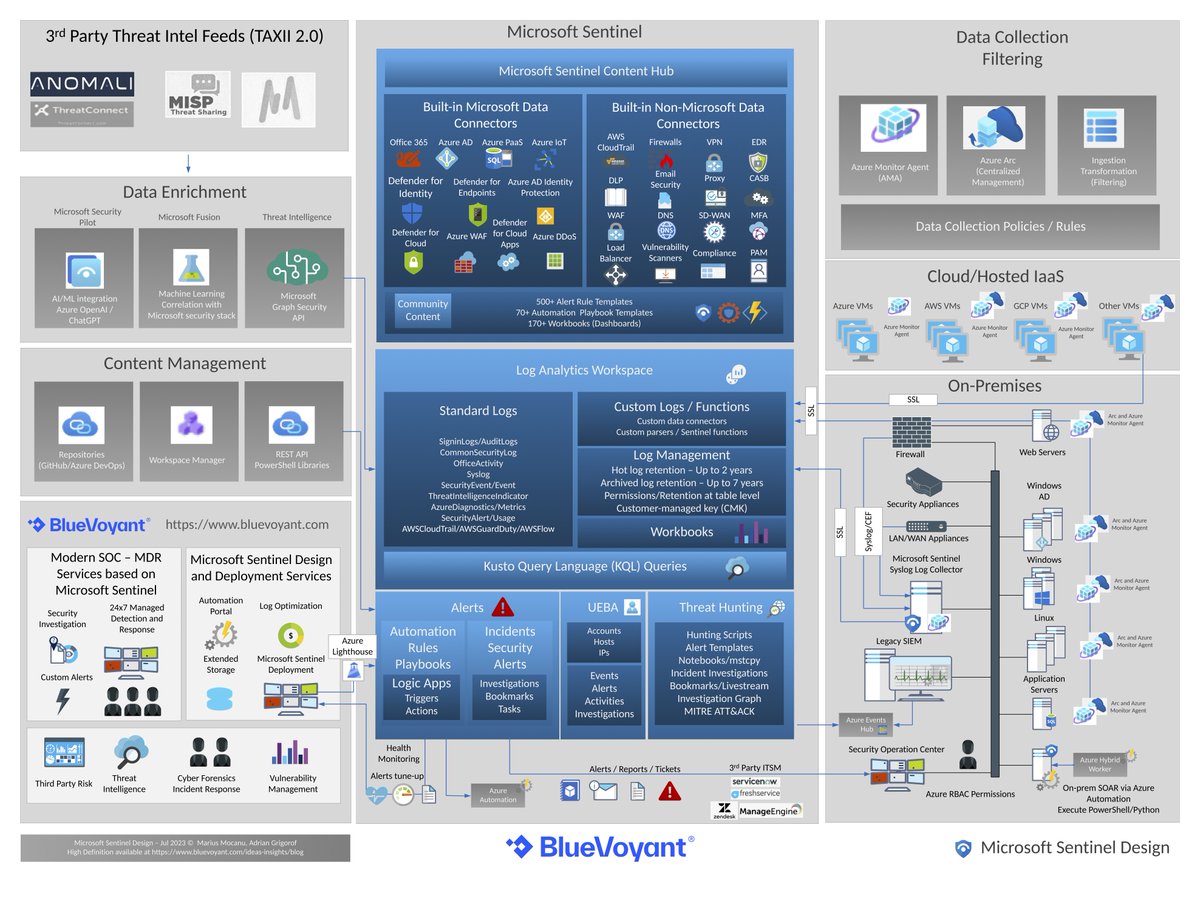
Microsoft Sentinel introduced a significant number of new features and improvements of existing ones since our last diagram update. This one page diagram attempts to cover the core components and the integration with log sources. #microsoftsentinel #siem
1
24
95
2 new Microsoft Sentinel alert rule templates published:. - Workspace deletion activity from an infected device.- TI map IP entity to Network Session Events (ASIM Network Session schema). #microsoftsentinel .@BlueVoyant.
0
2
2
2 new Microsoft Sentinel alert rule templates published:.#microsoftsentinel .@BlueVoyant. Chia_Crypto_Mining IOC - June 2021.(Preview) TI map IP entity to DNS Events (ASIM DNS schema).
0
3
2
2 new Microsoft Sentinel alert rule templates published:.#microsoftsentinel .@BlueVoyant . Front Door Premium WAF - SQLi Detection.Front Door Premium WAF - XSS Detection.
0
1
4
2 new Microsoft Sentinel alert rule templates published:.#microsoftsentinel @bluevoyant. Guest accounts added in AAD Groups other than the ones specified. Guest accounts changed user type from guest to members in AzureAD.
1
4
12
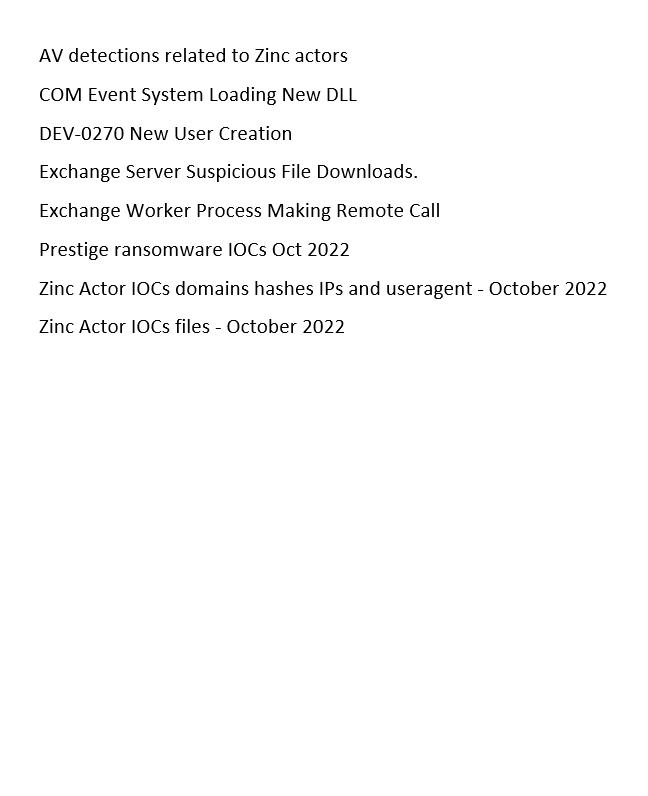
8 new Microsoft Sentinel alert rule templates published (471 in total):.#microsoftsentinel @bluevoyant
0
5
18
SIEM engineers wanted for Microsoft Sentinel and Azure cloud security journey. Good wages, work from home, flexible hours. Safe return (to previous job) doubtful. Honour, recognition and advancement in event of success. @BlueVoyant #MicrosoftSentinel.
4
1
3
New Microsoft Sentinel alert rule templates published:.#microsoftsentinel . AV detections related to Europium actors.Azure Diagnostic settings removed from a resource.Europium - Hash and IP IOCs - September 2022.Unusual Anomaly.Unusual identity creation using exchange powershell.
2
10
27
New Microsoft Sentinel alert rule template published:. AD FS Abnormal EKU object identifier attribute. Uses Security events from the AD FS Auditing provider to detect suspicious object identifiers as part event ID 501 (from the Enhanced Key Usage attributes). #microsoftsentinel.
0
1
2
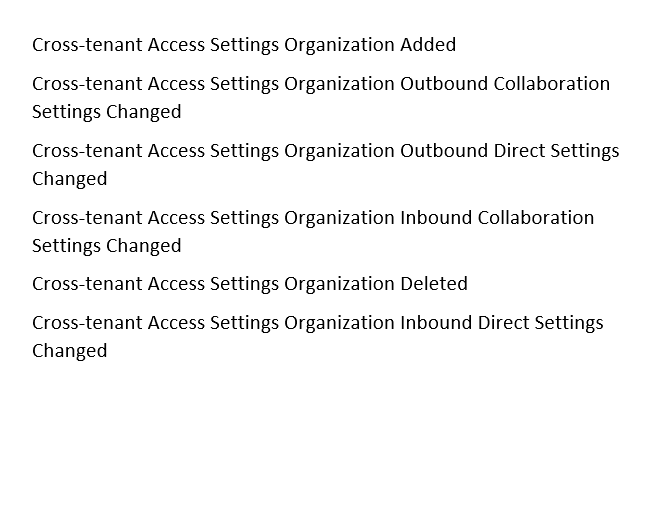
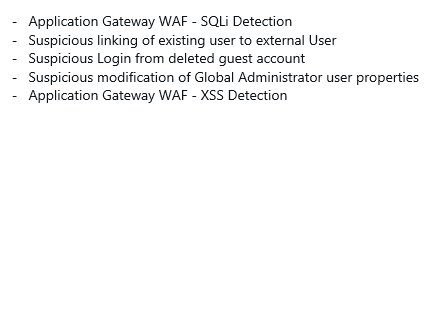
New Microsoft Sentinel alert rule templates published:.#MicrosoftSentinel @BlueVoyant @ManagedSentinel
1
3
11