Moonbeom(Daniel)
@krNeoTra
Followers
952
Following
9K
Media
69
Statuses
5K
CPO(Chief Product Officer) at 78ResearchLab, Hacking incident analysis, Digital Forensic, Research on hacking technique, Profiling hacking source.
Joined September 2010
#exploit 1⃣. CVE-2025-50165: Critical Flaw (RCE) in Windows Graphics Component - https://t.co/p3KATYNDYX // Windows 11 24H2 x64/ARM64, Windows Server 2025 2⃣. CVE-2025-9491: Windows UI misrepresentation vulnerability - https://t.co/9qKIOSQ7Fd // PoC tool for demonstrating the
zscaler.com
CVE-2025-50165, a flaw in the Microsoft Windows Graphics Component, enables attackers to execute code remotely without privileges using a malicious JPEG.
0
2
3
🚨 Indirect-Shellcode-Executor Tool Exploits Windows API Vulnerability to Evade AV and EDR Source: https://t.co/uR14i7Wq5r A new offensive security tool developed in Rust is demonstrating a novel method for bypassing modern Endpoint Detection and Response (EDR) systems by
4
125
430
Analysis and Exploit Demo of the CVE-2024-38077(Windows Remote Desktop Licensing Service Pre-auth 0-Click Remote Code Execute Vulnerability) https://t.co/gEWn6IkeCi
#0_Click_RCE #CVE_2024_38077 #Remote_Desktop
0
0
1
#ParallelPulse @nanosec_asia 2025 kicks off with our Technical Training series! Welcome back to KL @krNeoTra & Sangsoo Jeong of @78_lab ! The stage is set. 🦸♂️ 𝖶𝖾’𝗋𝖾 𝗋𝖾𝖺𝖽𝗒! 𝗍𝗁𝖾 𝗋𝖾𝖺𝗅 𝗊𝗎𝖾𝗌𝗍𝗂𝗈𝗇 𝗂𝗌: 𝖠𝖱𝖤 U?! 🔜 https://t.co/jBLXTqIf1m
0
5
7
#ParallelPulse wrapped up 𝐀𝐝𝐯𝐚𝐧𝐜𝐞𝐝 𝐓𝐡𝐫𝐞𝐚𝐭 𝐇𝐮𝐧𝐭𝐢𝐧𝐠 & 𝐈𝐑 training with an amazing cohort! Huge 🫶 to everyone who dug into the labs & pushed through the challenges. 🙏to @krNeoTra & Sangsoo @78_lab for your amazing sharing. Onward we go, stronger & sharper!
0
2
10
🔍Think #ParallelPulse is “too technical”? Nah-it’s built for everyone who cares about cyber resilience. Whether you’re in security, IT, audit, or leadership, we’ve got sessions that break down complex threats into real-world impact you can actually use. https://t.co/JUdp71IdH4
0
5
5
🚀 #ParallelPulse '25 agenda is LIVE! 2 days of high-impact talks, deep-dive tech sessions & max fun! +💻awesome activities! 1️⃣ @sherpasecmy SherpaCTF2025 2️⃣ @stealthmole_int OSINT Hands-On 3️⃣ The Range Village AD Range https://t.co/jBLXTqIf1m
https://t.co/2pJqqwBzOk
0
9
17
#Lazarus have recently resorted to utilizing JSON storage services like JSON Keeper, JSONsilo, and npoint/.io to host and deliver malware from trojanized code projects, with the lure being a use case or demo project as part of an interview process. #InvisibleFerret
1
8
28
#exploit High severity Windows vulnerabilities: 1⃣. CVE-2025-26686: RCE in Windows 10/11/Srv TCP/IP stack - https://t.co/kswysi2zzg // leaves sensitive memory unlocked, allowing remote attackers to hijack systems. Exploitable over the network, it risks full compromise. Patch
github.com
A critical RCE vulnerability in Windows TCP/IP stack (CVE-2025-26686) leaves sensitive memory unlocked, allowing remote attackers to hijack systems. Exploitable over the network, it risks full comp...
3
47
170
🚨 New talk #ParallelPulse2025: @78_lab breaks down Gunra, a Conti-variant that hit major SK banks. Learn how @78_lab reverse-engineered the malware, found a critical vuln & replicated decryption via a known-plaintext attack. 👉 https://t.co/ZXy0cHrO9Q
0
3
8
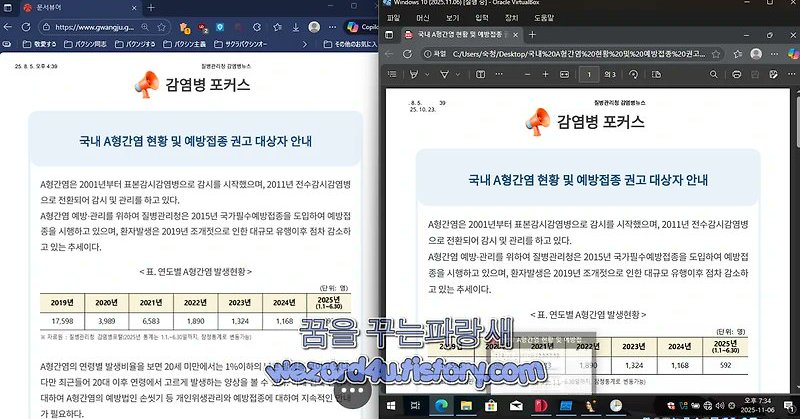
김수키(Kimsuky) 한컴 에이전트-국내 A형간염 현황 및 예방접종 권고 대상자 안내.pdf.scr.exe https://t.co/c8Fbo0C8mY #김수키 #Kimsuky #악성코드
wezard4u.tistory.com
오늘은 북한 김수키 에서 만든 악성코드인 국내 A형간염 현황 및 예방접종 권고 대상자 안내.pdf.scr.exe에 대해서 간단하게 알아보는 시간을 가져 보겠습니다.ファイル名:국내 A형간염 현황 및 예방접종 권고 대상자 안내.pdf.scr.exeサイズ:3 MBMD5:0f3e5058154de146fb3f1921c7f89952SHA-1:6a79104f950...
0
1
1
Hello, while investigating the Midnight or EndPoint ransomware, for which a decryption tool was recently released, I discovered several suspicious points and decided to compile a brief report about them Report : https://t.co/HvJZIEkkgl
#Ransomware #Kimsuky #Lazarus #APT
github.com
Contribute to errbody/DPRK-Research development by creating an account on GitHub.
0
18
87
Windows Graphics Vulnerabilities Lead to Remote Code Execution and Memory Exposure https://t.co/hmbhV2oDD0
0
38
192
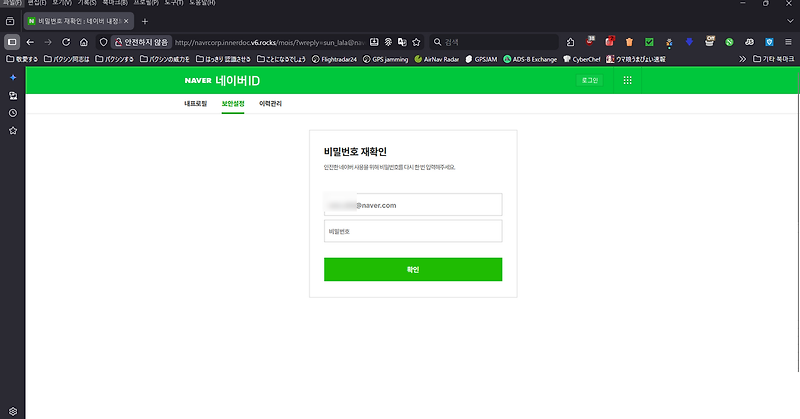
김수키(Kimsuky) 행정안전부 사칭 이메일 분석(2025.10.9) https://t.co/zAYFcoh2Bf #김수키 #Kimsuky
wezard4u.tistory.com
오늘은 북한 김수키(Kimsuky) 행정안전부 사칭 이메일 분석(2025.10.9)에 대해서 양자역학적으로 분석으로 해보겠습니다. wwww해당 피싱 메일은 행정안전부에서 보낸 것으로 돼 있지만, 행안부에서 그런 것을 보낸 것이 아닌 피싱 메일 입니다.피싱 메일 내용새로운 전자문서가 도착했어요. ???**** 님, 지금 확인해보세요. 개인정보가 포함된...
0
1
1