My new blog: Windows 11 2022 and new security features - this is the most secure version of Windows we have ever produced. Proud of the work the entire team has done, Let's gooooo
25
164
530
Replies
Shout outs to
@enigma0x3
and
@tifkin_
for the great work pen testing smart app control to get this release ready
1
2
26
@dwizzzleMSFT
any chance of third party access to Credential Guard e.g. store sensitive tokens in VBS; only unseal to same application?
1
1
7
@dwizzzleMSFT
"Presence detection sensors work with Windows Hello to sign you in when you approach, and lock when you leave."
This sounds great
What are the hardware dependencies?
1
0
2
@dwizzzleMSFT
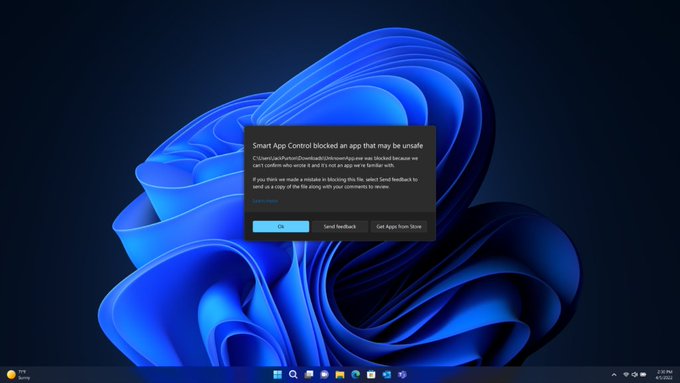
Yeah, sure. I don't like what that dialog is saying at all though. Can I turn it off?
0
0
0
@dwizzzleMSFT
@MsftSecIntel
Sweet noticed some changes when using FIDO key, is there a reason it switches to other user when signing back in from a locked session?
0
0
0
@dwizzzleMSFT
Personally I think you should have left off the "most secure version of Windows we have ever produced". That's tempting fate
0
0
1
@dwizzzleMSFT
Most secure version of Windows is like saying the least poisonous version of poison 🤷♂️
Active directory is still an unmaintainable mess, as are UAC and other windows internals.
#icannotshruganyharder
0
0
7
@dwizzzleMSFT
Thank you for the great post! But what about Windows security features on ARM-based CPU: 1. How memory is protected? 2. How TPM is involved? 3. What are the key differences between new Windows security mechanisms on Intel-based and ARM-based CPU? Thank you!
0
0
0
@dwizzzleMSFT
great post! here are a few additional mitigation ideas that i would love to see:
- a unified syscall enable/disable mechanism :each process having a list of allowed syscalls. Would permit to restrict kernel attack surface from sandbox and simplify code by merging several 1/N
2
0
1
@dwizzzleMSFT
Is it expected behavior that the The Microsoft vulnerable driver block list does not ever get updated on endpoints, with Windows Update or whatever other mechanism may be present with a powered-on machine?
0
0
11