Talence Security
@TalenceSecurity
Followers
535
Following
1,073
Media
26
Statuses
543
We specialize in offering training programs that cover both defensive and offensive #cybersecurity
Joined September 2016
Don't wanna be here?
Send us removal request.
Explore trending content on Musk Viewer
Taylor Swift
• 1099755 Tweets
عيد الغدير
• 114617 Tweets
Kennedy
• 112372 Tweets
#النصر_الفيحاء
• 60982 Tweets
Title IX
• 43048 Tweets
Snyder
• 36614 Tweets
Push Ups
• 33738 Tweets
Zidane
• 31953 Tweets
Fallout 4
• 25798 Tweets
Ryan Garcia
• 20454 Tweets
AbdülalimKaya TahliyeEdilmeli
• 20203 Tweets
Max Azzarello
• 18224 Tweets
Rebel Moon
• 17082 Tweets
Watcher
• 16250 Tweets
Adele
• 15013 Tweets
Jason Wilcox
• 14862 Tweets
Inès
• 14581 Tweets
Tyler Perry
• 13561 Tweets
LO SIENTO IS COMING
• 11503 Tweets
$NVDA
• 11195 Tweets
Aaron Bushnell
• 10839 Tweets
Mandisa
• 10227 Tweets
Last Seen Profiles
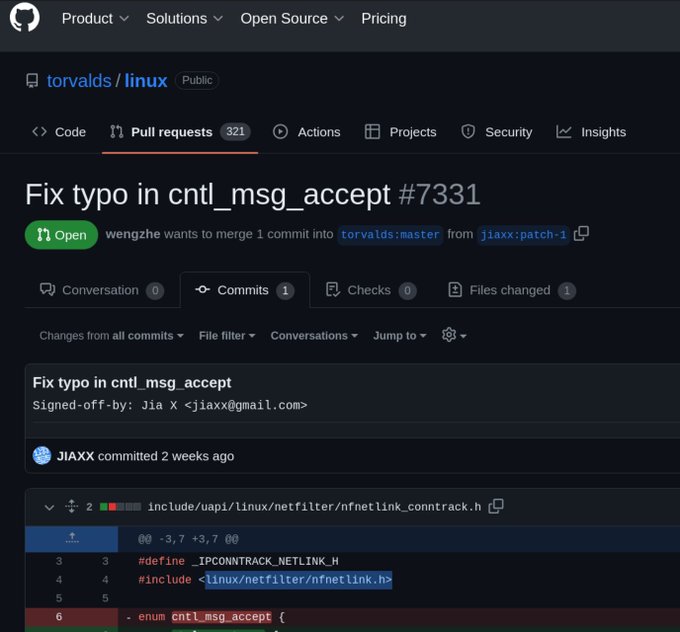
🚨 ALERT:
#LinuxKernel
backdoor in netfilter! JIAXX user's pull request malicious code 2 wks ago, manipulating 'cntl_msg_accept' in netfilter/nfnetlink_conntrack.h so netfilter may permit incoming TCP connections via a specific magic packet sequence, potentially resulting in RCE!
56
142
1K
Log4J - CVE 2021-44228 (Log4Shell) - Exploitation & Mitigation by
@HackerSploit
#Log4J
#Log4Shell
#CVE
#cybersecurity
#infosec
#pentesting
#ethicalhacking
#redteam
0
7
14
@Sudhans42246878
Only if there is an open
#bugbounty
program... Otherwise it's jail program for you.
1
0
10
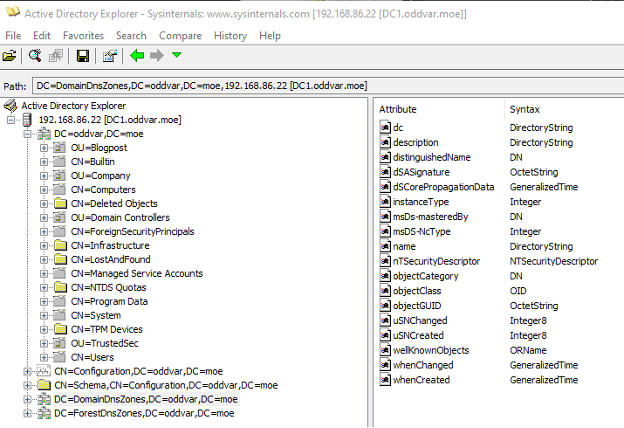
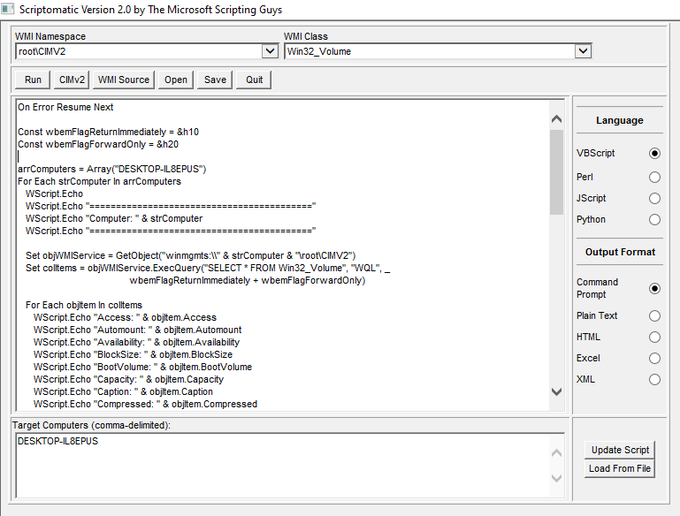
PowerShell commands for enumerating Active Directory Environments. Very nice list by
@joehelle
.
#Windows
#PowerShell
#PowerView
Useful for
#cybersecurity
#RedTeam
&
#PenTest
too
1
2
9
@woodyatpch
@summer__heidi
There is an obvious glitch in the Matrix here.
The car is from 2019, but the guy came straight from 1992.
0
0
7
@Itskaranxa
@Bugcrowd
@Hacker0x01
@hakluke
@codingo_
1) Set goals for progress
2) Continuously keep learning
3) Understand the tools or even better, do manual actions
0
1
6
Fight CONTI ransomware: an API block cheat sheet by
@Marco_Ramilli
#Malware
#Ransomware
#threatintelligence
#blueteam
0
3
5
@UK_Daniel_Card
@EricaZelic
@shotgunner101
@tazwake
@SOSIntel
@HackingLZ
@vysecurity
@lkarlslund
@cybersecstu
What a gang!
@EricaZelic
+
@shotgunner101
+
@tazwake
+
@SOSIntel
+
@HackingLZ
+
@vysecurity
+
@ZephrFish
+
@lkarlslund
+
@cybersecstu
1
0
3
Hunting for samAccountName Spoofing (CVE-2021–42278) & Domain Controller Impersonation (CVE-2021–42287) by
@mvelazco
#cybersecurity
#infosec
#pentesting
#ethicalhacking
#redteam
0
3
3
Cobalt Strike Decoding and C2 Extraction - 3 Minute Malware Analysis by Matthew
@embee_research
Watch now:
#Malware
#ReverseEngineering
0
1
2
Our "Comprehensive Introduction to Cyber Security" course is available for FREE (1000 seats)
(or use coupon: FREE-DEC2022-TW)
Please share and Enjoy!
#udemy
#cybersecurity
#training
#freecourses
#infosec
#infosecurity
#courses
#computersecurity
1
2
2
Cloud Native Fuzzing: Istio - 40 crashes and high-severity CVE by
@IstioMesh
@AdamKorcz4
#Fuzzing
#CyberSecurity
0
0
2
@shotgunner101
@UK_Daniel_Card
@EricaZelic
@tazwake
@SOSIntel
@HackingLZ
@vysecurity
@lkarlslund
@cybersecstu
It's now out of control, I prefer Dragon Ball (Goku kid) and DBZ (especially the Kai version). DB GT was also great before the Dragons chapter. Wdyt?
1
0
2
@Essb33
Those there have 1 to 10% of specific knowledge, which can be theirs, they have acquired the remaining 90-99% by people, they should thank them and their approach of sharing, otherwise they would never have acquired this 1-10% themselves.
Receive and share.
0
0
2
MalApi () by
@mrd0x
=> List Windows APIs used by
#Malware
=> Great project to support!
#BlueTeam
#ThreatIntel
#threatintelligence
#forensics
1
2
2
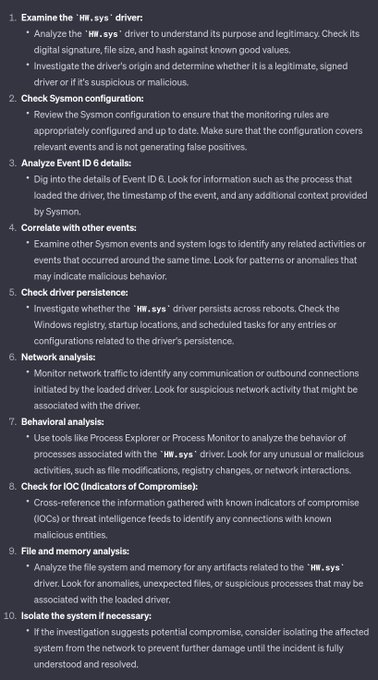
"ADEXPLORER ON ENGAGEMENTS"
Using ADExplorer from an offensive perspective by
@Oddvarmoe
#PenetrationTesting
#PenTest
#RedTeam
#CyberSecurity
0
0
1
@mrd0x
, the current list is pretty impressive. Well done!
Just submitted a few APIs to contribute!
1
0
1
Palo Alto Warns of Zero-Day Bug in Firewalls Using GlobalProtect Portal VPN
CVE-2021-3064, CVSS score: 9.8, impacts PAN-OS 8.1 versions earlier than PAN-OS 8.1.17
#threatintelligence
#BlueTeam
#0days
#exploit
0
2
1
@BrocktonPTS
@cybersec_feeds
It aims to detect Log4Shell exploitation attempts, no to detect if an environment is vulnerable ;-)
cc:
@cyb3rops
0
0
1
@Octoberfest73
Interesting idea. Depending on the tools and the possibilities of obtaining them elsewhere, if all are not yours?
0
0
1
A great list of popular and trusted domains used to conduct attacks.
#ThreatIntel
#ThreatIntelligence
0
1
1
@MrTuxracer
Ah yes, I understand your point better. Thanks.
The question is really very complex and multifaceted, maybe more transparency and/or regulation is needed for this new (amazing) technology.
1
0
1
"Introducing Mystikal" for macOS initial access payloads by Leo Pitt
@_D00mfist
from
@SpecterOps
#redteam
#PenTest
#macOS
0
0
1
Interesting perspective! "on-premises employees" versus "cloud employees" 🤣
0
0
1
@Sudhans42246878
I agree with you, but some companies may not like it when you watch something without having a clear mandate. I wouldn't take a chance at this game, seriously...
1
0
1
You really need to execute a backdoor to confirm its presence. Live your most exciting life!
0
0
1
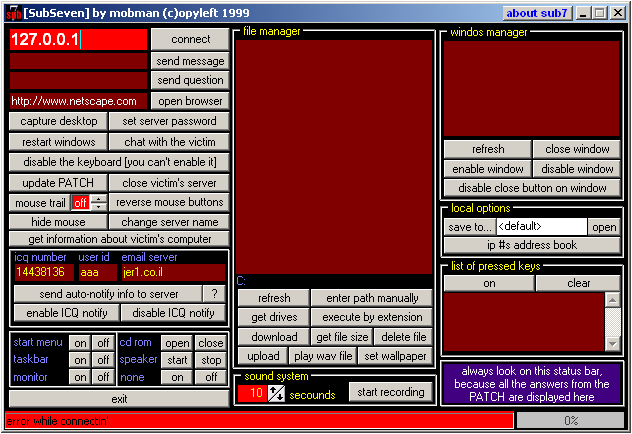
Oldies but goodies
0
0
1
Regarding the XZ backdoor, Debian 12 stable remains unaffected.
Thanks
@Kostastsale
for the safe one-liner
@debian
#xzbackdoor
#xz
#XZUtils
0
0
1
2/n: Open-source projects often face challenges due to a lack of human, financial, and material support, as seen with the recent XZ backdoor incident
#xzbackdoor
#XZUtils
1
0
0
@fleming_matt
Very interesting work, congratulations and well done for making the code open source.
0
0
1
Anti-Ransomware Next-Gen protection 🤣
0
0
1
@joehelle
Ignoring that email may result in receiving an email with the same information. Ignoring that email may result in receiving another email with the same information. Sorry.
1
0
1
@0xTib3rius
I'll throw
@TalenceSecurity
shamelessly. Feel free to follow; we've got an exciting project lined up for the year as a new company 🙏
0
0
1
@Kostastsale
You really need to execute a backdoor to confirm its presence. Live your most exciting life!
0
0
1
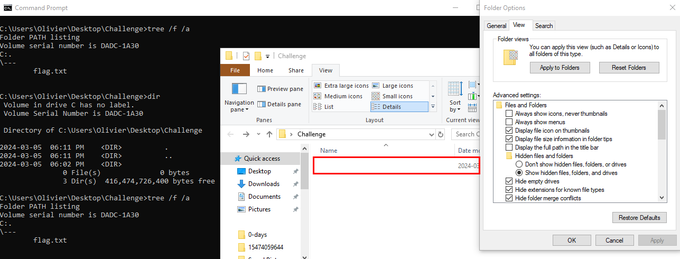
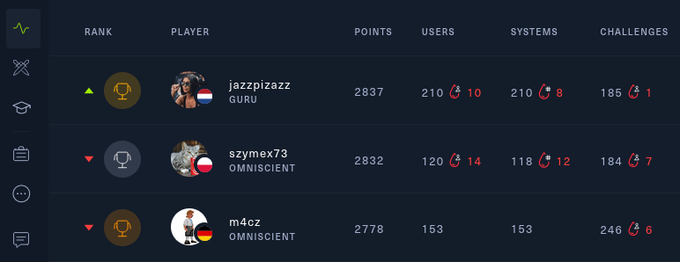
Congratz!
Today I reached
#1
on
@hackthebox_eu
! It probably won't be for long but it's still a huge achievement for me 😎 Special shoutouts to Tabacci for helping me with crypto,
@clubby789
for making a cheesable 9 point challenge and
@devx00
for recommending HeapLap :)
20
15
490
0
0
1
Elastic Security uncovers BLISTER malware campaign.
Awesome work and analysis by
@SBousseaden
@dez_
@elastic
#ThreatIntelligence
#ThreatIntel
#BlueTeam
#CyberSecurity
#YARA
0
2
1